Optimizing Host-Device Data Transfer in Biomedical Research: Strategies to Reduce Overhead and Accelerate Discovery
This article provides a comprehensive guide for researchers, scientists, and drug development professionals on reducing host-device data transfer overhead, a critical bottleneck in data-intensive fields like bioinformatics, medical imaging, and...
Optimizing Host-Device Data Transfer in Biomedical Research: Strategies to Reduce Overhead and Accelerate Discovery
Abstract
This article provides a comprehensive guide for researchers, scientists, and drug development professionals on reducing host-device data transfer overhead, a critical bottleneck in data-intensive fields like bioinformatics, medical imaging, and AI-driven drug discovery. It explores the foundational causes of transfer inefficiency, presents practical methodological solutions from edge computing and high-performance computing (HPC), offers advanced troubleshooting and optimization techniques for real-world scenarios, and establishes a framework for validating and comparing strategy effectiveness. By synthesizing current research and emerging trends, this resource aims to equip biomedical teams with the knowledge to significantly accelerate computational workflows, reduce operational costs, and expedite the path from data to discovery.
Understanding the Data Transfer Bottleneck: Why Overhead Slows Down Biomedical Research
Defining Host-Device Data Transfer Overhead and Its Impact on Computational Pipelines
In heterogeneous computing systems, host-device data transfer overhead refers to the performance cost incurred when moving data between the CPU (host) and an accelerator like a GPU (device). This overhead is a critical bottleneck that can severely impact the overall performance and efficiency of computational pipelines, particularly in data-intensive fields such as scientific research and drug development [1] [2]. This guide provides troubleshooting and FAQs to help researchers identify, understand, and mitigate this overhead.
Frequently Asked Questions (FAQs)
1. What exactly is host-device data transfer overhead? This overhead encompasses the time and computational resources required to copy data from the host's memory to the device's memory and back. It includes latency from kernel launches, signaling between host and device, and the physical transfer of data across the PCIe bus [1] [3]. During this transfer, the computational units on the device often sit idle, leading to underutilization.
2. Why does transferring small data chunks result in lower throughput? PCIe is a packet-based transport with fixed overhead per transfer, including packet headers. With small data chunks, this fixed overhead constitutes a larger proportion of the total transfer time, reducing efficiency. Full throughput is typically achieved only with larger transfers (e.g., over 8 MB on PCIe gen3 x16) [3].
3. What is the difference between pageable and page-locked (pinned) host memory?
- Pageable memory is standard memory managed by the operating system, which can be paged out to disk. Transferring data from pageable memory to a device requires the driver to first copy it to a temporary page-locked buffer, adding significant overhead [4] [5].
- Page-locked memory is locked to physical RAM, preventing the OS from paging it out. This allows for direct memory access (DMA) by the device, leading to higher and more consistent transfer bandwidth [4] [5].
4. How can I overlap data transfers with computation on the device? Using asynchronous operations and streams, you can pipeline your workflow. While one stream is executing a kernel on the device, a different stream can be simultaneously transferring data for the next operation, effectively hiding the transfer latency behind useful computation [2] [6].
5. My application processes data in chunks. How can I minimize latency? Instead of offloading one large batch, break the data into smaller chunks and process them with multiple shorter-running kernels. This "streaming" design makes the first pieces of processed data available to the host much earlier, significantly reducing latency [1].
Troubleshooting Guide
Identifying Data Transfer Overhead
Use profiling tools like Intel VTune Profiler or NVIDIA Nsight Systems to:
- Measure the time spent on data transfers (
cudaMemcpycalls) versus kernel execution. - Identify whether the application is bound by data transfer operations.
- Visualize the timeline to see if there are gaps between kernels and transfers, indicating a lack of overlap.
Common Symptoms and Solutions
| Symptom | Possible Cause | Recommended Solution |
|---|---|---|
| Low overall throughput; GPU is often idle. | Data transfers are blocking kernel execution; transfers and computation are sequential. | Use asynchronous streams to overlap data transfers and kernel execution [2] [6]. |
| High latency for receiving first result. | Processing data in one large batch (offload model). | Switch to a streaming model with smaller, more frequent kernel launches [1]. |
| Low PCIe transfer bandwidth, especially with small data sizes. | Using pageable memory; small transfer sizes magnifying PCIe packet overhead. | Allocate critical buffers in page-locked host memory; aggregate small transfers into larger chunks [3] [4] [5]. |
| Performance degrades when multiple tasks are launched. | Suboptimal scheduling of tasks leads to poor overlap of transfers and kernels. | Reorder tasks using a scheduling model to maximize concurrent execution of transfers and compute from different tasks [2]. |
Quantitative Data and Performance Comparison
| Transfer Size | Pageable Memory (GB/s) | Page-Locked Memory (GB/s) |
|---|---|---|
| 16 KB | 6.9 | 11.9 |
| 64 KB | 5.4 | 12.0 |
| 256 KB | 5.4 | 12.4 |
| 1 MB + | ~5.5 | ~12.4 |
| Data Transfer Method | Total Processing Time (seconds) |
|---|---|
| H2D from Pageable Memory | 7.90 |
| H2D from Page-Locked Memory | 7.92 |
| H2D from Page-Locked Memory (with multi-threading) | 4.92 |
Experimental Protocols
Protocol 1: Measuring the Impact of Page-Locked Memory
Objective: To quantify the performance benefit of using page-locked host memory for data transfers.
Methodology:
- Allocation: Create two sets of host buffers: one allocated with standard
malloc(pageable) and another withcudaMallocHostorcudaHostAlloc(page-locked). - Timing: For a range of data sizes (e.g., 16 KB to 16 MB), use
cudaEventtimers to measure the duration ofcudaMemcpyoperations from host to device. - Calculation: Compute the effective bandwidth for each transfer:
Bandwidth = Data Size / Transfer Time. - Analysis: Plot bandwidth against transfer size for both memory types, as shown in Table 1.
Protocol 2: Implementing a Pipelined Workflow with Streams
Objective: To hide data transfer latency by overlapping it with kernel execution.
Methodology:
- Setup: Create multiple CUDA streams. Allocate page-locked memory for input and output buffers.
- Division: Split the workload into N chunks.
- Execution: For each chunk
i:- In a dedicated stream, initiate an asynchronous transfer (H2D) for chunk
i's input data. - Launch the processing kernel in the same stream, which will wait for the transfer to complete.
- Initiate an asynchronous transfer (D2H) for chunk
i's output data.
- In a dedicated stream, initiate an asynchronous transfer (H2D) for chunk
- Overlap: While the kernel for chunk
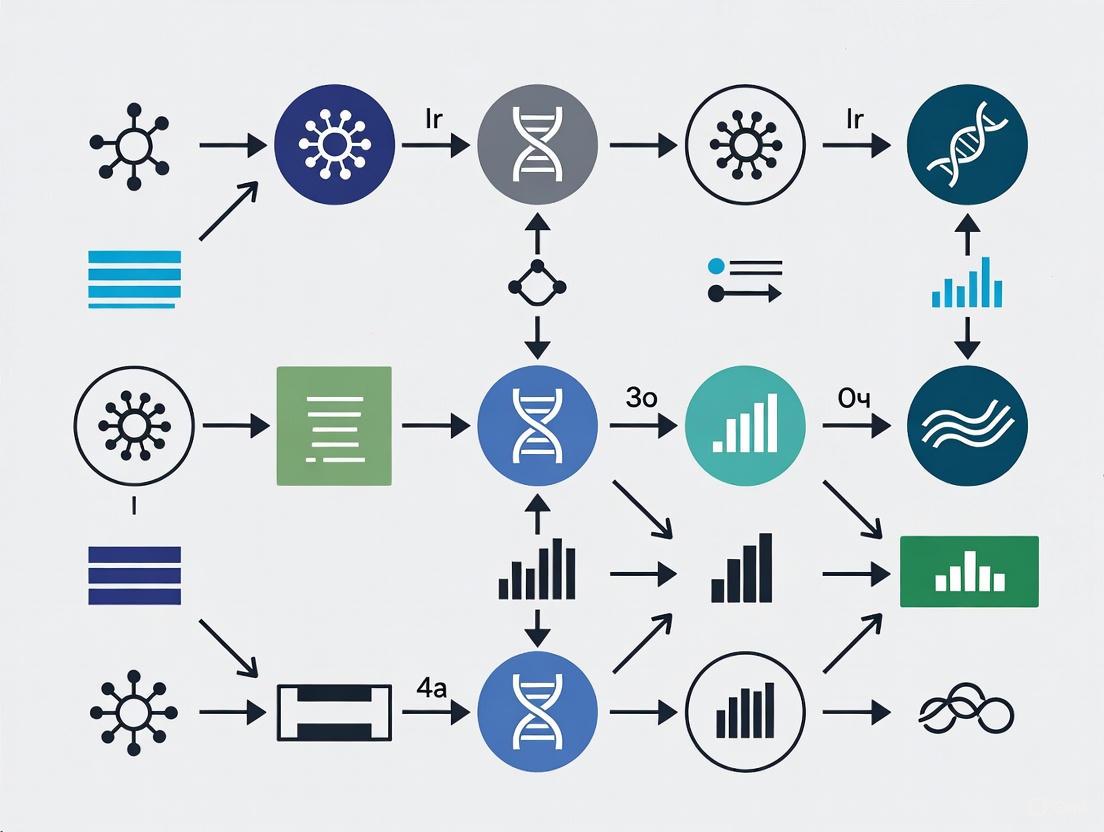
iis running in one stream, the data transfers for chunki+1can occur concurrently in another stream. The following diagram illustrates this pipelined workflow.
Diagram Title: Stream Pipeline Overlap
The Scientist's Toolkit: Key Research Reagents & Solutions
| Item | Function in Experiment |
|---|---|
| SYCL Unified Shared Memory (USM) | A memory management model that simplifies data access across host and device, facilitating zero-copy access and host-device streaming designs [1]. |
| CUDA Streams / OpenCL Command Queues | Software constructs used to queue operations (transfers, kernels) for concurrent execution, enabling overlap of data transfer and computation [2]. |
Page-Locked Memory Allocator (e.g., cudaMallocHost) |
Allocates non-pageable host memory, enabling high-bandwidth, direct transfers to and from the device [4] [5]. |
| nvCOMP Library | A GPU-accelerated compression library that can reduce the volume of data transferred. On NVIDIA Blackwell architectures, it can offload decompression to a dedicated hardware engine [7]. |
| Profiling Tools (e.g., Intel VTune, NVIDIA Nsight) | Essential for identifying performance bottlenecks, measuring transfer times, and verifying the effectiveness of overlap strategies [6] [8]. |
To visualize the fundamental trade-off between latency and throughput that guides the choice of data processing models, refer to the diagram below.
Diagram Title: Processing Model Trade Offs
For researchers, scientists, and drug development professionals, high-performance computing (HPC) and artificial intelligence (AI) have become indispensable tools. The efficiency of moving data between hosts and devices (e.g., CPUs and GPUs) is a critical, yet often overlooked, factor that can make or break an experiment's feasibility, cost, and timeline. Inefficient data transfers create a cascade of negative effects, directly increasing latency, energy consumption, and operational expenses. This guide, framed within the broader thesis of reducing host-device data transfer overhead, provides a technical support center to help you diagnose, understand, and mitigate these inefficiencies in your experimental workflows.
FAQs: Understanding Data Transfer Inefficiency
1. What are the primary technical causes of data transfer inefficiency? Data transfer inefficiency arises from a combination of suboptimal application-layer configurations, hardware limitations, and dynamic network conditions. Key technical causes include:
- Improper Concurrency and Parallelism: The parameters for task-level parallelism (
concurrency) and file-level parallel streams (parallelism) are often set statically. If these values are too low, they underutilize available network bandwidth and I/O capacity. If set too high, they can oversaturate the network, triggering TCP congestion control mechanisms and drastically reducing throughput [9]. - Unoptimized Data Payloads: The format and size of the data being transferred significantly impact performance. Using uncompressed or inefficiently compressed data increases transfer volume and time. Furthermore, transfers involving numerous small files can be hampered by protocol overhead, as opposed to larger, consolidated files [7].
- Hardware and Network Bottlenecks: A chain is only as strong as its weakest link. Slow storage (e.g., HDDs instead of NVMe drives), limited network interface card (NIC) bandwidth, or lack of high-speed interconnects like InfiniBand for multi-node workloads can create severe bottlenecks, leaving powerful accelerators like GPUs idle while waiting for data [10].
2. How does transfer inefficiency directly increase our research costs? The financial impact is twofold, affecting both immediate operational expenditure (OPEX) and long-term capital outlays.
- Cloud Computing Costs: In cloud environments, you pay for GPU/CPU time by the hour. Inefficient data transfers extend the total runtime of your training or analysis jobs. A model that takes 100 GPU hours to train with efficient transfers could take 120+ hours with poor transfers, increasing compute costs by over 20% [11] [10].
- Energy Consumption: Data transfers consume significant energy at the end systems (sender and receiver). Research shows that on a nationwide network, end systems can account for 60% of the total energy consumed during an end-to-end transfer. Inefficient transfers that run longer or overload resources can increase this energy usage by up to 40% [9].
- Infrastructure Investment: To compensate for poor transfer performance, organizations may feel pressured to over-provision hardware (e.g., purchasing more or faster GPUs) or buy more network bandwidth, leading to unnecessary capital expenditure (CAPEX) [12].
3. What is the connection between data transfer performance and energy usage? The relationship is direct and proportional. Prolonged data transfers keep CPUs, NICs, and storage systems under high load for extended periods, consuming more electricity. Actively transferring data also prevents systems from entering low-power idle states. A study on adaptive data transfer optimization demonstrated that intelligent parameter tuning can achieve up to a 40% reduction in energy usage at the end systems compared to baseline methods, highlighting the significant energy waste caused by inefficiency [9].
4. Are there hardware solutions to accelerate data transfer and decompression? Yes, new hardware innovations are specifically designed to offload and accelerate these costly operations. NVIDIA's Blackwell architecture, for example, introduces a dedicated Decompression Engine (DE), a fixed-function hardware block that offloads the task of decompressing common formats like Snappy, LZ4, and Deflate from the general-purpose GPU cores. This not only speeds up decompression but also frees up valuable Streaming Multiprocessor (SM) resources to focus on core computation tasks, thereby reducing overall job completion time and latency [7].
Troubleshooting Guides
Guide 1: Diagnosing Data Transfer Bottlenecks
Use this workflow to systematically identify the source of transfer slowdowns in your experimental pipeline.
Diagnostic Steps:
- Check Network Utilization: Use tools like
nloadoriftopto monitor the network interface during a transfer. If the bandwidth is consistently maxed out (e.g., at 10 Gbps on a 10 Gbps link), the network itself is the bottleneck. - Check CPU Utilization: Use
toporhtop. If the CPU cores on the sending and/or receiving nodes are at or near 100% utilization during the transfer, the data transfer process itself is CPU-bound, likely due to protocol processing or software-based compression/decompression. - Check I/O Wait Times: Use
iostat -x 1. High%utilandawaitvalues for your storage devices (e.g.,/dev/sda) indicate that the storage system cannot keep up with the read/write requests, creating an I/O bottleneck.
Guide 2: Implementing an Adaptive Transfer Tuning Strategy
For environments with dynamic network conditions (e.g., shared research clusters), static tuning is insufficient. This guide outlines a methodology for adaptive optimization based on state-of-the-art research.
Experimental Protocol: Reinforcement Learning for Parameter Tuning
- Objective: Dynamically adjust application-layer parameters (
concurrencyandparallelism) to maximize throughput and minimize energy consumption under changing network traffic. - Background: The relationship between transfer parameters (
cc,p), throughput, and energy is non-linear. Research shows optimal settings can improve performance by up to 10x compared to baseline (cc=1,p=1), but these optima shift with background traffic [9]. - Methodology (Based on SPARTA DRL Framework):
- Define State Space: The state should include real-time metrics such as current throughput, round-trip time (RTT), and CPU idle time on the end systems.
- Define Action Space: The actions are discrete changes to the
concurrencyandparallelismparameters (e.g., increment, decrement, or hold). - Define Reward Function: Design a reward function that balances multiple objectives. For example:
Reward = α * Throughput - β * Energy_Consumption. This encourages the system to find a Pareto-optimal solution between speed and efficiency. - Training: Train a Deep Reinforcement Learning (DRL) agent in an emulation environment that replicates your network conditions. Using logged state transitions from initial real-world episodes can significantly accelerate training and reduce the associated energy costs [9].
- Expected Outcome: Studies have shown this approach can yield up to a 25% increase in throughput and up to a 40% reduction in energy consumption at the end systems compared to static configuration or heuristic-based methods [9].
Quantitative Data on Transfer Inefficiency
Table 1: Documented Impacts of Data Transfer Inefficiency
| Metric | Impact of Inefficiency | Source / Context |
|---|---|---|
| Big Data Project Failure Rate | 85% of projects fail | Gartner analysis of large-scale data projects [12] |
| System Integration Failure Rate | 84% fail or partially fail | Integration research across industries [12] |
| Annual Revenue Loss | 25% of revenue lost | Due to poor data quality and related inefficiencies [12] |
| Productivity Cost of Data Silos | $7.8 million annually | Lost productivity from fragmented data [12] |
| Energy Overconsumption | Up to 40% higher at end systems | Compared to optimized adaptive transfer methods [9] |
| Cloud AI Data Transfer Fees | Up to 30% of total cloud AI spend | For data-intensive applications [11] |
Table 2: Cost Comparison: Cloud vs. Edge AI Processing
This table summarizes the financial trade-offs, which are heavily influenced by data transfer volume and cost [11].
| Cost Factor | Cloud-Based AI Processing | Edge-Based AI Processing |
|---|---|---|
| Cost Model | Operational Expenditure (OPEX) | Capital Expenditure (CAPEX) |
| Primary Costs | GPU instance time, data egress fees, API calls | Upfront hardware investment, power, maintenance |
| Example: Video Analytics (200 stores) | ~$1.92M annually (streaming + processing) | ~$2.8M over 3 years (hardware + maintenance) |
| Example: NLP (1M calls/month) | ~$48,000 annually | ~$111,000 over 3 years |
| Best For | Variable workloads, less data-heavy inference | Predictable, data-heavy workloads, low-latency scenarios |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Optimizing Data Transfers
| Tool / Technology | Function | Relevance to Research |
|---|---|---|
| NVIDIA nvCOMP with Blackwell DE [7] | Hardware-accelerated decompression library. Offloads decompression from GPU SMs to a dedicated engine. | Crucial for accelerating data-loading pipelines in AI-driven research (e.g., drug discovery, genomics). Reduces GPU idle time and overall experiment latency. |
| High-Performance Interconnects (InfiniBand) [10] | Low-latency, high-throughput networking for multi-node systems. | Essential for distributed training of large models across multiple GPU nodes. Prevents communication from becoming the bottleneck. |
| SPARTA DRL Framework [9] | A Deep Reinforcement Learning framework for dynamic parameter tuning of data transfers. | Provides a methodology for researchers to autonomously optimize their data transfers for performance and energy efficiency in shared, dynamic network environments. |
| DataOps Platforms [12] | Platforms that bring rigor and orchestration to data management and flow. | Ensures high data quality and efficient pipeline operations, which is foundational for reliable and reproducible experimental results. The market is growing at a 22.5% CAGR. |
| Hybrid AI Architecture [11] | A strategy that splits AI workloads between cloud and edge computing. | Enables researchers to train models in the cloud but run inference locally (at the edge), minimizing ongoing data transfer costs and latency for real-time analysis. |
Quantifying the cost of transfer inefficiency is the first step toward building more robust, cost-effective, and sustainable research computing environments. The latency, energy waste, and operational expenses are not merely theoretical but are quantifiable drains on research budgets and timelines. By leveraging the diagnostic guides, experimental protocols, and tools outlined in this technical support center, researchers and scientists can systematically attack the problem of data transfer overhead. Integrating these optimization strategies directly into your experimental design is no longer a niche advanced technique but a core competency for leading-edge research in 2025 and beyond.
Technical Support Center
Troubleshooting Guides
Q1: My GPU inference efficiency is lower than expected. Profiling shows the GPU is often idle. What is the cause and how can I resolve this?
A: This is a classic symptom of host overhead, where the GPU (device) is blocked waiting for the CPU (host) to prepare work [13]. The root cause often lies in the disjoint address spaces between the host and device, which necessitates explicit data transfers that can stall the GPU [6].
Diagnosis and Resolution Protocol:
- Profile Your Application: Use the PyTorch Profiler or NVIDIA Nsight Systems to collect a trace of your application's execution. Visually inspect the trace for "gaps" in the CUDA streams where no kernels are running [13].
- Identify Synchronization Points: In the trace, look for these common culprits:
- Unnecessary data transfers between CPU and GPU within critical loops.
- A high number of small, individual CUDA kernel launches.
- CPU-based operations that must complete before the GPU can proceed.
- Apply Corrective Optimizations:
- Eliminate Redundant Transfers: Construct tensors directly on the GPU instead of on the CPU and then transferring them. Use
cudaMallocManagedfor Unified Memory to let the system manage data movement [14]. - Fuse Kernels: Use the Torch compiler to merge multiple small kernel launches into a single, larger kernel, reducing launch overhead [13].
- Use CUDA Graphs: For a fixed sequence of operations, capture the entire graph of kernels into a single launchable unit using CUDA Graphs. This amortizes the launch overhead and is widely used in production inference servers [13].
- Eliminate Redundant Transfers: Construct tensors directly on the GPU instead of on the CPU and then transferring them. Use
The following workflow diagram illustrates the diagnostic process for identifying and resolving host overhead:
Q2: The data transfer time between my host and device is a major bottleneck. How can I improve the transfer performance?
A: Data transfer overhead is a fundamental challenge in systems with disjoint address spaces [6]. Optimizing it involves both hardware awareness and software techniques.
Experimental Protocol for Data Transfer Optimization:
- Verify Hardware Configuration:
- Run
nvidia-smiduring an active transfer to ensure your GPU is using a PCIe gen3 x16 slot (or higher). Slots configured as x4 or x8 will have lower bandwidth [15]. - In multi-socket CPU systems, set CPU and memory affinity so each GPU communicates with its "near" CPU to avoid inter-socket traffic [15].
- Run
- Use Pinned Host Memory: Allocate page-locked ("pinned") memory on the host using
cudaHostAlloc(). This enables higher bandwidth transfers compared to standard pageable memory [15]. - Maximize Transfer Size: PCIe transfer rates increase with block size. Aim to transfer large, contiguous blocks (e.g., up to 16MB) to achieve full interface throughput [15].
- Overlap Transfers and Computation: Use CUDA streams to perform asynchronous data transfers concurrently with kernel execution. On GPUs with dual copy engines, this also allows simultaneous copies to and from the device [15].
The table below summarizes key quantitative considerations for data transfer optimization:
| Optimization Factor | Target / Best Practice | Quantitative Impact / Rationale |
|---|---|---|
| PCIe Interface | PCIe gen3 x16 (or higher) | Enables >= 10 GB/s throughput for large transfers [15]. |
| Host Memory Type | Pinned (Page-locked) Memory | Can provide ~12 GB/s vs. ~5 GB/s for pageable memory [15]. |
| Transfer Size | Large, contiguous blocks (e.g., 16 MB) | Larger transfers are needed to achieve full PCIe throughput [15]. |
| Execution Overlap | CUDA Streams for Async Transfer | Hides transfer latency by executing kernels concurrently [15]. |
Frequently Asked Questions (FAQs)
Q1: From a research perspective, what is the core architectural reason for host-device data transfer overhead?
A: The fundamental reason is physically separate memories [6]. In conventional heterogeneous systems like CPU-GPU setups, the host (CPU) and device (GPU) have their own distinct, attached physical memories. This design creates disjoint address spaces. Therefore, any data needed for a GPU computation must be explicitly transferred from host memory to device memory, an operation that incurs significant latency and bandwidth costs over the PCIe bus [6]. The staging of data in a temporary area is a direct consequence of this architectural separation.
Q2: What are the trade-offs between using a staging environment for testing versus directly deploying to production?
A: Using a staging environment (a near-exact replica of production) for testing provides significant benefits but also has limitations, leading to alternative strategies like "staging in production."
| Strategy | Benefits | Limitations & Risks |
|---|---|---|
| Staging Environment | - Catches performance and integration issues before production [16]. - Reduces liability and improves regulatory compliance for critical apps [16]. - Enables final User Acceptance Testing (UAT) [16]. | - Cannot perfectly simulate real-world traffic and user behavior [16]. - Configuration mismatches with production can yield inaccurate test results [16]. - Adds management overhead and cost [16]. |
| Direct Production Deployment (e.g., with Feature Flags) | - Tests with real user traffic and data volumes [17]. - Faster iteration by skipping staging setup [16]. - Enables gradual rollouts and instant rollbacks [17]. | - Higher risk of exposing users to bugs [16]. - Requires robust feature flagging and monitoring systems [17]. - Less suitable for highly regulated or mission-critical applications [16]. |
Q3: How can our research team build an efficient and manageable HPC environment for GPU-accelerated drug discovery?
A: Modern managed services can significantly reduce operational overhead. The architecture below, inspired by a real-world implementation, provides a robust foundation [18].
Methodology for a Managed HPC Environment:
- Use a Managed HPC Service: Leverage services like AWS Parallel Computing Service (PCS), which uses Slurm as a job scheduler. This automates cluster management tasks like Slurm version upgrades [18].
- Automate Custom Image Creation: Use a service like EC2 Image Builder to create custom Amazon Machine Images (AMIs). Define a recipe that installs necessary PCS agents, Slurm packages, and your team's specific application software (e.g., molecular modeling tools) [18].
- Streamline User Management: Implement an automated workflow using AWS Step Functions and Systems Manager (SSM) Documents. When compute nodes start, they execute scripts that pull user information from a JSON file and automatically create user accounts, providing immediate access to the HPC environment [18].
The following diagram visualizes this automated HPC environment architecture:
The Scientist's Toolkit: Key Research Reagent Solutions
This table details essential software and hardware "reagents" for conducting high-performance computing experiments focused on reducing host-device overhead.
| Tool / Solution | Function in Experimentation |
|---|---|
| NVIDIA Nsight Systems | A system-wide performance analysis tool used to visualize application execution, identify GPU idle periods ("gaps"), and pinpoint the root cause of host overhead [13]. |
| PyTorch Profiler | A profiling tool integrated with PyTorch that helps diagnose performance issues in ML models, including data transfer bottlenecks and kernel execution times [13]. |
| CUDA Unified Memory | A memory management technology that creates a single address space for CPU and GPU, simplifying programming by reducing the need for explicit data transfers (though it may not eliminate all overhead) [14]. |
| CUDA Graphs | A technique to capture a sequence of kernel launches and dependencies into a single, reusable unit. This dramatically reduces kernel launch overhead and is critical for low-latency inference [13]. |
| Pinned (Page-Locked) Memory | A type of host memory allocation that enables the highest possible data transfer speeds between the host and GPU device [15]. |
| AWS Parallel Computing Service (PCS) | A managed HPC service that reduces operational overhead by automating job scheduling (Slurm) and cluster management, allowing researchers to focus on their experiments [18]. |
In the context of research aimed at reducing host-device data transfer overhead, understanding the "hidden data tax" imposed by security and communication protocols is paramount. For scientists and drug development professionals transmitting sensitive experimental data, Transport Layer Security (TLS) is the essential cryptographic protocol that ensures privacy and integrity. However, this security comes at a cost: significant overhead that can impact data transfer efficiency. This overhead manifests as additional data traffic, increased computational processing, and communication latency, primarily introduced during the initial TLS handshake and through the record layer headers for each data packet [19].
This guide provides troubleshooting and methodological support for researchers measuring and mitigating these overheads in experimental data transfer setups, directly supporting the broader thesis of optimizing data efficiency in research environments.
Quantitative Analysis of TLS Overhead
The overhead caused by TLS can be broken down into two main phases: the connection-establishing handshake and the ongoing data encapsulation in the record layer. The following tables summarize the typical overhead encountered in practice.
TLS Handshake Overhead
The TLS handshake establishes a secure connection by negotiating cryptographic parameters and authenticating the server. The following table quantifies the traffic overhead for different handshake types, based on average message sizes [20].
Table: TLS Handshake Traffic Overhead
| Handshake Type | Description | Approximate Traffic Overhead | Round Trips (TLS 1.2) |
|---|---|---|---|
| Full Handshake | Establishes a new secure session. | ~6.5 KB [20] | 2 |
| Session Resumption | Resumes a previously established session. | ~330 bytes [20] | 1 |
TLS Full Handshake Flow
TLS Record Layer Overhead
After the handshake, application data is transmitted in protected packets. The per-packet overhead depends on the cryptographic cipher suite used [21].
Table: Per-Packet Data Overhead in TLS Record Layer
| Cipher Suite Type | TLS Header | IV/Nonce | MAC (Message Auth.) | Padding | Total Approx. Overhead |
|---|---|---|---|---|---|
| AES-CBC (e.g., TLSRSAWITHAES128CBCSHA) | 5 bytes | 16 bytes [21] | 20 bytes [20] | 0-15 bytes [20] | ~40-55 bytes |
| AEAD (e.g., AES-GCM, ChaCha20-Poly1305) | 5 bytes | 8 bytes [21] | 16 bytes (integrated) | 0 bytes | ~13-21 bytes |
Experimental Protocols for Measuring Overhead
To accurately characterize protocol overhead in a research data transfer environment, follow these experimental methodologies.
Experiment 1: Measuring Handshake Traffic Volume
Objective: To quantify the total bytes transferred solely for establishing a TLS connection. Methodology:
- Setup: Use a packet capture tool (e.g., Wireshark) on either the client or server host device.
- Configuration: Ensure the research application is configured to force a new TLS connection (disable session resumption).
- Execution: Initiate a connection from the client to the server. Filter captures to show only TLS traffic between the two hosts.
- Measurement: In the packet capture tool, select all packets from the initial
ClientHelloto the finalFinishedmessage. The tool's statistics function will report the total bytes captured. This value is the handshake overhead. - Variation: Repeat the experiment with session resumption enabled and compare the total bytes transferred.
Experiment 2: Measuring Record Layer Efficiency
Objective: To determine the efficiency loss due to TLS per-packet encapsulation. Methodology:
- Setup: Configure a test setup where a research host device generates a known, consistent payload size (e.g., 100 bytes, 500 bytes, 1500 bytes).
- Execution: Transmit this payload securely to another device.
- Measurement: Use a packet capture tool to examine the resulting TLS records. Compare the original payload size with the actual wire size of the TLS record(s). Calculate the efficiency as
Payload Size / Wire Size * 100. - Analysis: Repeat with different payload sizes and cipher suites (e.g., AES-CBC vs. AES-GCM) to build a model of overhead impact.
The Scientist's Toolkit: Research Reagent Solutions
This table details key technical solutions and their role in mitigating data transfer overhead.
Table: Key Reagents for Overhead Mitigation
| Reagent / Solution | Primary Function | Role in Reducing Overhead |
|---|---|---|
| TLS 1.3 | The latest TLS protocol version. | Reduces handshake latency from 2 round-trips to 1, significantly cutting connection setup time [19]. |
| Session Resumption | A mechanism to reuse previously negotiated session parameters. | Avoids the full handshake, reducing subsequent connection overhead to a fraction of the original [22]. |
| AEAD Cipher Suites | Cryptographic algorithms like AES-GCM and ChaCha20-Poly1305. | Combine encryption and authentication, eliminating the need for separate MAC and padding, which reduces per-packet overhead [21]. |
| Packet Capture Software | Tools like Wireshark for network analysis. | Enables precise measurement of protocol overhead by inspecting raw traffic between host devices. |
| HTTP/2 | A major revision of the HTTP network protocol. | Allows multiple requests/responses to be multiplexed over a single TLS connection, amortizing handshake overhead across many data transfers [19]. |
Troubleshooting Guide: FAQs
Q1: Our data transfer rates for sensitive experimental data are slower than expected. Could TLS be the cause?
A: Yes. Investigate the following:
- Handshake Frequency: Are you opening a new TLS connection for every transaction? This is highly inefficient. Solution: Modify your application code or configuration to reuse connections (HTTP keep-alive) and leverage TLS session resumption.
- Cipher Suite: Are you using an older cipher suite? Solution: Prioritize modern, more efficient AEAD cipher suites like
TLS_AES_128_GCM_SHA256. This reduces per-packet CPU and traffic load [21] [19]. - Payload Size: Are you sending a vast number of very small packets? Solution: If possible, batch small data points into larger payloads to reduce the relative impact of the fixed record layer overhead.
Q2: We are seeing high CPU usage on our data acquisition server during encrypted transfers. Is this normal?
A: Cryptographic operations are computationally expensive, so some increase is expected. However, high usage can be mitigated.
- Check Cipher Suite: Ensure you are using cipher suites with hardware acceleration, such as AES-NI for AES-GCM, which is common on modern processors [21].
- Consider Offloading: For very high-traffic scenarios, investigate TLS termination at a load balancer or dedicated security appliance, which offloads the CPU cost from your application server [19].
Q3: What is the single most effective change to reduce TLS overhead for a long-lived data stream?
A: Ensure TLS session resumption is working. A full 6.5 KB handshake occurs only for the first connection. All subsequent resumptions on that session use a much lighter ~330-byte exchange, saving substantial bandwidth and latency [20]. Verify this is enabled in your client and server configurations.
Q4: How does the choice of cipher suite directly impact our data usage costs?
A: The cipher suite dictates the per-packet overhead. For a continuous stream of small data packets (e.g., sensor telemetry), the difference between a 55-byte overhead (AES-CBC-SHA) and a 15-byte overhead (AES-GCM) compounds rapidly. Over millions of packets, this can result in a significant increase in transmitted bytes, directly impacting costs if you are paying for bandwidth [21].
TLS Overhead Symptom and Solution Map
Technical Support Center: Troubleshooting High-Throughput Data Workflows
This technical support center provides targeted guidance for researchers facing computational bottlenecks in genomics, medical imaging, and molecular dynamics. The following troubleshooting guides and FAQs address common issues, with a specific focus on methodologies to reduce host-device data transfer overhead, a critical bottleneck in high-performance biomedical computing.
Genomics Data Analysis Support
Frequently Asked Questions
What are the primary data management challenges in genomic research? Genomic research, particularly with Next-Generation Sequencing (NGS), faces several key challenges [23]:
- Volume: A single human genome requires up to 100 GB of storage. NGS workflows generate terabytes of data, straining traditional storage systems [23].
- Variety and Complexity: Workflows involve diverse data types (sequences, ligated variants, linkages) and change frequently with new reagents, protocols, and instruments [23].
- Data Transfer Bottlenecks: Processing and analytics have become the new bottleneck, as moving massive datasets between storage, host (CPU), and device (GPU/accelerator) memory is slow [23] [24].
How can we securely manage genomic data from external collaborators? For collaborations with CROs or academic partners, implement a cloud-based Laboratory Information Management System (LIMS). This provides controlled, role-based data access, ensures data security across locations, and offers the scalability needed for massive genomic datasets. The solution must have robust controls for compliance with regulations like CLIA, GDPR, and HIPAA [23].
Troubleshooting Guide: Slow Genomic Variant Calling Pipeline
- Problem: AI-powered variant calling (e.g., with DeepVariant) is unacceptably slow, delaying analysis [25].
- Investigation Steps:
- Profile the Workflow: Measure the time spent on data loading, host-to-device (H2D) transfer, GPU computation, and result output.
- Check GPU Utilization: Use tools like
nvidia-smito confirm the GPU is being used and is not memory-bound. - Verify Data Locality: Check if data is being read from a remote or slow network-attached storage source.
- Solution: Implement a high-performance, portable data reduction framework like HPDR [24].
- Methodology: HPDR minimizes costly data transfers by executing state-of-the-art reduction algorithms directly on the GPU. It uses an optimized pipeline that adaptively overlaps data reduction with transfer operations.
- Expected Outcome: HPDR can reduce data transfer overhead to just 2.3% of the original and accelerate end-to-end reduction throughput by up to 3.5x [24].
Quantitative Performance Metrics for Data Reduction Frameworks
| Framework/Metric | Transfer Overhead Reduction | End-to-End Throughput Gain | Multi-GPU Speedup Efficiency | Key Feature |
|---|---|---|---|---|
| HPDR Framework [24] | 2.3% of original | Up to 3.5x faster | 96% of theoretical maximum | Portable across CPU/GPU architectures |
| Standard GPU Compression [24] | 34-89% of total time | Baseline (1x) | As low as 74% | Typically optimized for NVIDIA only |
Medical Imaging & Cloud PACS Support
Frequently Asked Questions
Our hospital's on-premise PACS is running out of storage. What are our options? You can implement a Cloud Tiering strategy or migrate to a full Cloud PACS [26] [27].
- Cloud Tiering: Automatically moves older, less frequently accessed "cold" DICOM images to cost-effective cloud storage tiers while keeping current "hot" data on high-performance on-premise storage. This optimizes costs while meeting data retention requirements [26].
- Cloud PACS: A full cloud-based Picture Archiving and Communication System offers scalability, reduced upfront costs, and robust disaster recovery. It also enhances accessibility for remote diagnostics and teleradiology [26] [27].
Is it safe to store patient scans in the cloud? Yes, with proper safeguards. Leading cloud providers implement advanced security measures for healthcare data, including encryption for data at rest and in transit (e.g., TLS for DICOM transfers), role-based access controls, and regular security audits. These measures often exceed the security of on-premise systems and are designed for compliance with HIPAA and other regulations [26] [27].
Troubleshooting Guide: Slow Retrieval of Medical Images for AI Analysis
- Problem: Researchers experience long delays when retrieving large sets of DICOM images from a biobank to train AI models [28] [27].
- Investigation Steps:
- Check Network and Storage Tier: Confirm the images are not stored in a deep, slow "cold" storage archive. Verify network bandwidth sufficiency.
- Analyze Data Access Patterns: Determine if the AI training is accessing the entire dataset or small, random batches.
- Inspect Data Pre-processing: Check if the bottleneck is in decoding or normalizing the DICOM files after transfer.
- Solution: Optimize the storage architecture and data pipeline.
- Methodology: For the biobank, implement a scalable cloud storage solution with a "warm" cache tier for active research projects [26]. Integrate a dedicated DICOM file-sharing solution that uses compression and efficient networking protocols (C-STORE, C-MOVE) to speed up transfer [27].
- Expected Outcome: Faster, secure access to imaging data, enabling efficient training of multimodal AI models that integrate imaging with clinical metadata [29].
Molecular Dynamics & High-Performance Computing Support
Frequently Asked Questions
Our molecular dynamics simulation slows down when visualizing results in real-time. Why? This is a classic host-device data transfer bottleneck. The simulation running on the GPU generates massive amounts of particle data (coordinates, velocities). To visualize it, this data must be transferred back to the host CPU and then to the GPU again for rendering. The PCIe bus linking the CPU and GPU becomes saturated, causing low frame rates and poor interactivity [30].
How can we achieve real-time, interactive visualization of massive MD simulation data? The solution requires a combination of in-situ visualization and advanced scheduling [30].
- In-situ Visualization: Process and render the data as it is generated on the GPU, avoiding the costly transfer back to the CPU host [30].
- GPU Hyper-tasking & Scheduling: A specialized scheduling scheme keeps both the CPU and GPU fully utilized. The GPU is "hyper-tasked" to perform local data compression and participate in rendering, while the CPU handles simulation tasks. An activity-aware technique minimizes redundant data copies [30].
- Expected Outcome: This methodology has been shown to enable interactive visualization of over 1.7 billion protein data points with an average of 42.8 frames per second [30].
Troubleshooting Guide: Low Frame Rate in Real-Time MD Visualization
- Problem: In-situ visualization of a large-scale molecular dynamics trajectory is non-interactive, with a very low frame rate [30].
- Investigation Steps:
- Profile Data Transfers: Use profilers (e.g., NVIDIA Nsight) to quantify H2D and D2H transfer times versus computation time.
- Check Memory Usage: Confirm that the dataset exceeds the GPU's global memory, forcing continuous on-demand data transfers.
- Review Visualization Code: Determine if the rendering is being done on the CPU or if the GPU is used inefficiently.
- Solution: Implement the optimized scheduling and data transfer minimization technique described above [30].
- Methodology:
- Reconstruct the scheduling scheme to hyper-task the GPUs for rendering.
- Use an activity-aware data-transfer minimization algorithm to reduce redundant copies of structural data.
- Leverage all available GPUs in a system by having each compress its local data for rendering.
- Experimental Protocol:
- Software: C++, OpenMP for CPU multi-threading, CUDA for GPU operations, OpenGL for rendering.
- Hardware: A single node with a multi-core CPU (e.g., 44-core Xeon) and multiple GPUs (e.g., NVIDIA Tesla M40).
- Benchmarking: Compare frame rates and interactivity before and after implementing the optimized scheduler.
- Methodology:
Diagram 1: MD Visualization Bottleneck & Optimization.
The Scientist's Toolkit: Essential Research Reagent Solutions
Key Computational Tools & Frameworks for High-Performance Biomedical Computing
| Tool/Framework | Primary Function | Application Context |
|---|---|---|
| HPDR [24] | High-performance, portable data reduction framework. | Minimizes data transfer overhead in genomics and general scientific computing on GPUs. |
| Cloud PACS [26] [27] | Cloud-based Picture Archiving and Communication System. | Securely stores, manages, and provides scalable access to DICOM medical images. |
| In-situ Scheduler [30] | CPU-GPU scheduling for real-time visualization. | Enables interactive exploration of massive molecular dynamics and agent-based simulation data. |
| Modern LIMS [23] | Laboratory Information Management System. | Tracks complex genomic workflows, manages sample lineage, and ensures data integrity. |
| Multimodal AI (Transformers, GNNs) [29] | Integrates imaging, clinical, and genomic data. | Provides comprehensive diagnostic and prognostic models for precision medicine. |
Practical Strategies for Efficient Data Movement: From Compression to Unified Memory
FAQ: Core Concepts and Techniques
What is data reduction and why is it critical in scientific research? Data reduction involves reducing the size or complexity of data while preserving its essential characteristics and minimizing information loss. In scientific research, this is crucial due to the "Big Data" phenomenon, where massive datasets from instruments, sensors, and simulations can lead to inefficient energy consumption, suboptimal bandwidth utilization, and rapidly increasing storage costs in cloud environments. Strategically applying data reduction techniques is fundamental to managing this information overload and streamlining data analysis processes in a resource-efficient way [31].
What is the main difference between lossy and lossless reduction techniques? The primary difference lies in whether the original data can be perfectly reconstructed after the reduction process.
- Lossless Techniques: These methods allow for the exact original data to be reconstructed from the compressed data. They are typically used when absolute data fidelity is required, such as in the storage of raw genomic sequences or final clinical trial data.
- Lossy Techniques: These methods achieve higher reduction rates by permanently discarding some data deemed less critical, accepting a controlled loss of information. They are suitable for scenarios like preliminary data analysis from high-frequency sensors or image data where minor inaccuracies are tolerable [31].
How do I choose the right data reduction technique for my dataset? The choice depends on your data type, the required fidelity, and your specific goal (e.g., reducing storage vs. speeding up transfer). The table below summarizes the purpose and common applications of core techniques [31] [32].
| Technique | Primary Function | Common Scientific Applications |
|---|---|---|
| Compression | Reduces data size by encoding information more efficiently. | Storing large genomic files (FASTQ, BAM), medical images, and historical sensor data [31] [33]. |
| Aggregation | Summarizes detailed data into a concise format (e.g., averages, sums). | Generating daily summary statistics from continuous environmental sensors or high-throughput screening results [31]. |
| Dimensionality Reduction | Reduces the number of random variables or features under consideration. | Preprocessing high-dimensional data (e.g., from transcriptomics or proteomics) for machine learning models [31]. |
| Pruning | Removes less important components from a model. | Compressing large AI models (e.g., BERT) used in drug discovery to reduce computational load and energy consumption [32]. |
| Knowledge Distillation | Transfers knowledge from a large, complex model to a smaller, faster one. | Creating compact, efficient models for real-time analysis of scientific data without significant performance loss [32]. |
| Quantization | Reduces the numerical precision of a model's parameters. | Accelerating inference of AI models on specialized hardware, enabling faster analysis in clinical trial data pipelines [32]. |
Our research involves AI models for drug discovery. Can data reduction help with sustainability? Yes, significantly. Model compression techniques directly address the environmental impact of large AI models. A 2025 study demonstrated that applying pruning and knowledge distillation to a BERT model reduced its energy consumption by 32.1% while maintaining 95.9% accuracy on a sentiment analysis task. Similarly, compression applied to other transformer models like ELECTRA achieved a 23.9% reduction in energy use. This makes AI-driven research more carbon-efficient without compromising critical performance metrics [32].
Troubleshooting Guides
Problem: High Data Transfer Overhead Slowing Down Analysis
Symptoms:
- Delays in moving data from instruments to analysis servers.
- Inability to perform real-time or near-real-time processing.
- High cloud egress costs and inefficient bandwidth utilization.
Solution: Implement a Cloud-Edge Collaborative Framework This approach processes data closer to its source (the "edge") before transferring it to the central cloud, drastically reducing the volume of data that needs to be transferred [34].
- Deploy Edge Nodes: Install small-scale computing devices at the data source (e.g., lab instrument, clinical site).
- Apply Initial Reduction: On the edge node, run a lightweight reduction algorithm. For heterogeneous IoT-style data from sensors, a two-stage approach is effective:
- Transfer Only Reduced Data: Send the significantly smaller, reduced dataset to the cloud for long-term storage or complex analysis.
This framework has been shown to achieve compression ratios below 40%, meaning over 60% of data volume is eliminated before transfer [34].
Problem: Loss of Critical Information After Aggregation
Symptoms: Important outliers or subtle patterns in the raw data are lost after applying aggregation (e.g., averaging), leading to incorrect conclusions.
Solution: Adopt a Tiered Fidelity Data Strategy
- Define Data Criticality: Categorize data based on its potential information value. For example, data from a final clinical trial is "high-criticality," while initial exploratory assay data may be "lower-criticality."
- Apply Lossless Reduction to High-Criticality Data: Use lossless compression algorithms (e.g., LZW, GZIP) for all final, validated datasets where every data point must be preserved [31].
- Apply Lossy Reduction for Exploration: For initial data exploration and analysis, use aggressive lossy techniques (e.g., Symbolic Aggregate Approximation - SAX) to quickly identify high-level trends and patterns [31].
- Retain Raw Data Temporarily: Store raw, high-fidelity data in a low-cost storage tier for a predefined period. This allows researchers to revert to the original data if anomalies are detected in the reduced dataset.
Problem: Compressed AI Models Show Significant Performance Degradation
Symptoms: After applying model compression to reduce computational load, the model's accuracy, precision, or other performance metrics drop unacceptably.
Solution: Follow a Structured Compression and Fine-Tuning Protocol
This methodology is based on experimental protocols used for compressing transformer models like BERT and ELECTRA [32].
- Establish a Performance Baseline: Fully train your model on the target dataset (e.g., Amazon Polarity for sentiment) and measure its baseline performance (Accuracy, F1-Score, ROC AUC) and resource consumption.
- Apply Compression Methodically:
- Pruning: Iteratively remove the least important weights (e.g., those with the smallest magnitudes) from the model. Prune in small increments (e.g., 10% of weights at a time).
- Knowledge Distillation: Train a smaller "student" model to mimic the output and intermediate representations of the larger, accurate "teacher" model.
- Quantization: Convert the model's parameters from 32-bit floating-point numbers to lower-precision formats like 16-bit floats or 8-bit integers.
- Fine-Tune the Compressed Model: This is a critical step. After compression, retrain the model for a small number of epochs on the original training data. This allows the model to recover from the performance loss induced by compression.
- Evaluate and Iterate: Compare the performance and energy efficiency of the compressed-and-fine-tuned model against your baseline. If performance is insufficient, adjust compression parameters and repeat.
The table below quantifies the performance and energy savings achieved in a controlled study applying these techniques [32].
| Model & Compression Technique | Performance (Accuracy) | Performance (ROC AUC) | Reduction in Energy Consumption |
|---|---|---|---|
| BERT (Baseline) | (Reference) | (Reference) | (Reference) |
| BERT + Pruning + Distillation | 95.90% | 98.87% | 32.10% |
| DistilBERT + Pruning | 95.87% | 99.06% | 6.71% |
| ELECTRA + Pruning + Distillation | 95.92% | 99.30% | 23.93% |
| ALBERT + Quantization | 65.44% | 72.31% | 7.12% |
The Scientist's Toolkit: Research Reagent Solutions
| Tool / Solution | Function in Data Reduction Research |
|---|---|
| CodeCarbon | An open-source Python package that estimates the amount of carbon dioxide (CO₂) produced by the computing resources used to run machine learning models. It is essential for quantifying the environmental benefits of model compression [32]. |
| Wavelet Transform Toolkits (e.g., PyWavelets) | Software libraries used for the first stage of data aggregation in edge computing, particularly effective for denoising and compressing signal and time-series data from scientific sensors [34]. |
| Tensor Decomposition Libraries (e.g., TensorLy) | Provide implementations of tensor decomposition methods like Tucker decomposition, used for advanced multi-dimensional data compression after initial aggregation [34]. |
| Pruning & Distillation Frameworks | Libraries integrated with deep learning frameworks (e.g., TensorFlow Model Optimization Toolkit, PyTorch) that provide algorithms for pruning model weights and performing knowledge distillation [32]. |
| Electronic Health Record (EHR) APIs (e.g., FHIR) | Standardized application programming interfaces that enable automated, systematic capture of clinical trial data (labs, medications) directly from source systems, reducing manual entry errors and the need for subsequent data verification [35]. |
| Cloud-Native Container Orchestration (e.g., Kubernetes) | Technology used to manage and scale the microservices that perform data reduction in cloud-edge frameworks, ensuring portable, reproducible, and efficient processing pipelines [33] [34]. |
Edge computing is a distributed computing paradigm that processes data near its source, at the "edge" of the network, rather than sending it to distant, centralized cloud servers. [36] [37] For researchers, scientists, and drug development professionals, this approach is transformative. It directly addresses the critical bottleneck of data transfer overhead in research workflows, enabling real-time analytics, reducing bandwidth costs and latency, and enhancing data security and privacy—a paramount concern when handling sensitive experimental or patient data. [38] [39] [37] By filtering and pre-processing data locally, edge computing allows you to transmit only valuable, aggregated insights, minimizing the massive data transfers that can slow down research and increase costs.
Core Architecture: How Edge Computing Works
Understanding the core components of an edge architecture is the first step to successful implementation. The following diagram illustrates how these components interact to process data efficiently.
Edge Computing Data Flow
The architecture consists of several key layers [37]:
- Edge Devices: These are the instruments generating raw data, such as lab sensors, high-throughput screeners, or patient monitoring devices. They perform minimal processing, like initial data filtering.
- Edge Gateways: This layer aggregates data from multiple devices. It handles basic analytics and preprocessing, such as data format conversion and aggregation.
- Edge Servers: Located close to the data source (e.g., in a lab or clinic), these servers perform heavy-duty local processing. This is where critical tasks like running AI inference models or real-time analytics occur. Data is temporarily stored here before only essential information is synced to the cloud.
- Cloud/Data Center: The central cloud provides long-term storage, in-depth analytics, and centralized management, such as training complex AI models that are then deployed back to the edge.
The Researcher's Toolkit: Protocols & Platforms
IoT Protocol Comparison for Research Environments
Choosing the right communication protocol is crucial for optimizing the performance of your edge computing setup. The table below compares the key characteristics of common protocols to guide your selection.
| Protocol | Energy Use | Latency | Bandwidth Efficiency | Security Features | Best For (Research Context) |
|---|---|---|---|---|---|
| MQTT | Moderate | Low | Moderate | Basic encryption | Resource-limited setups; lightweight sensor data collection. [40] |
| AMQP | High | Low | High | Built-in security | Mission-critical systems requiring reliable, secure message delivery. [40] |
| CoAP | Lowest | Lowest | Lowest | Basic security (DTLS) | Battery-powered, low-bandwidth devices; constrained lab environments. [40] |
| HTTP/REST | Highest | High | High | Mature security (HTTPS) | Scenarios prioritizing broad compatibility over efficiency. [40] |
| DDS | Low | Low | Low | Advanced security | Complex, real-time systems requiring high scalability and robustness. [40] |
Leading Edge Computing Platforms for 2025
Selecting a platform that fits your research infrastructure is key. Here are some leading platforms for 2025 [39]:
- Scale Computing Platform: A hyper-converged infrastructure (HCI) that combines virtualization, storage, and computing. It is known for its simplicity and automated self-healing technology, ideal for remote or distributed research sites with minimal IT support. [39]
- Azure IoT Edge (Microsoft): Allows deployment of AI-driven analytics and cloud workloads directly at the edge. It integrates seamlessly with Microsoft's cloud ecosystem, making it strong for projects already using Azure services. [39]
- Eclipse ioFog: An open-source framework designed for scalable, containerized workloads. It integrates with Kubernetes, offering flexibility for managing complex edge computing infrastructure. [39]
- Google Distributed Cloud Edge: Delivers AI-powered analytics and real-time data processing at the edge, with strong support for third-party integrations. [39]
Experimental Setup & Methodology
Workflow for Data Transfer Overhead Experiment
To quantitatively assess the impact of edge computing on data transfer overhead, you can implement the following experimental workflow.
Data Overhead Experiment Workflow
Objective: To measure the reduction in data transfer volume, latency, and bandwidth consumption achieved by implementing edge-based data pre-processing compared to a raw data transfer model.
Methodology [37]:
- Define Data Source and Baseline: Select a high-data-volume source relevant to your research (e.g., a live-cell imaging system, DNA sequencer, or distributed environmental sensor network). Establish a baseline by measuring the total data volume generated over a set period and the time taken to transfer this raw data to a central cloud server.
- Configure Edge Node Hardware: Select and set up an edge server or gateway with adequate CPU, memory, and storage for your processing needs. Ensure it is physically located near the data source. [37]
- Implement Pre-processing Logic: Deploy containerized applications on the edge node to perform data filtering. Examples include:
- Anomaly Detection: Transmit only data points that deviate significantly from a defined baseline.
- Data Compression: Use algorithms to reduce file sizes before transmission.
- AI Inference: Run a pre-trained machine learning model (e.g., for image segmentation or feature extraction) and send only the model's results (e.g., "cell count: 145") instead of the raw image or video feed. [38] [39]
- Execute Experiment and Collect Metrics: Run the data source with edge processing enabled. Collect the following quantitative data for the same duration as the baseline:
- Data Volume Transferred: Total size of data sent to the cloud.
- End-to-End Latency: Time from data generation to the availability of insights in the cloud.
- Bandwidth Utilization: Network bandwidth used during transmission.
- Analyze Results: Compare the metrics from the edge-enabled run against the baseline. Calculate the percentage reduction in data volume and latency.
Frequently Asked Questions (FAQ) & Troubleshooting
General Concepts
Q1: Why can't I just use the cloud for all my data processing? Traditional cloud computing centralizes processing in remote data centers. For large, continuous data streams, this creates a bottleneck due to latency (the delay in sending data and receiving a response), high bandwidth costs, and potential security risks from constantly transmitting sensitive data. Edge computing processes data locally, providing near-instant results and mitigating these issues. [39] [37]
Q2: How does edge computing relate to Federated Learning in drug discovery? They are highly complementary. Edge computing provides the infrastructure to process data locally on devices or within hospital firewalls. Federated Learning is a technique that leverages this infrastructure: it sends an AI model to the edge nodes where data resides, the model trains locally, and only the model updates (not the raw data) are sent back to a central server. This is a powerful paradigm for collaborating on AI model training without sharing sensitive patient or proprietary research data. [38]
Technical Implementation
Q3: My edge device has limited computing power. Which protocol should I use? For resource-constrained devices, CoAP (Constrained Application Protocol) is often the best choice. It is specifically designed for low-power, low-bandwidth devices and has the lowest energy consumption of the major protocols. [40] MQTT is another strong, lightweight candidate for simple messaging.
Q4: I am experiencing high latency even with an edge server. What could be wrong?
- Check the Protocol: Ensure you are not using a protocol like HTTP/REST, which has high latency. Switch to a more efficient protocol like MQTT or CoAP. [40]
- Network Configuration: Investigate local network congestion or interference.
- Server Load: The edge server itself may be overloaded. Monitor its CPU and memory usage to see if it requires more powerful hardware or if workloads need to be optimized. [37]
Q5: How can I ensure my edge node is secure?
- Encrypt Data: Ensure data is encrypted both at rest on the edge device and in transit to the cloud. [37]
- Secure Access: Implement multi-factor authentication and the principle of least privilege for accessing the edge node. [37]
- Regular Updates: Establish a process for regularly updating and patching the software running on your edge devices to fix vulnerabilities. [37]
Data Management
Q6: What kind of data pre-processing is most effective for reducing transfer volume?
- Filtering: Discard irrelevant data (e.g., removing empty or control images from a high-throughput screen).
- Compression: Using lossless or lossy compression algorithms for images and videos.
- Feature Extraction: Running AI models to extract only the relevant features (e.g., protein binding affinity scores) instead of sending the entire raw dataset. [38]
Q7: How do I handle data synchronization between the edge and the cloud if the connection is unstable? This is a core strength of edge architecture. Use local buffering or storage on the edge server to temporarily hold data. Employ messaging protocols like MQTT or AMQP with Quality of Service (QoS) levels that ensure messages are delivered once the connection is restored. The system can continue local operations independently during an outage. [40] [37]
This guide provides a technical framework for researchers, scientists, and drug development professionals to select the optimal data transfer protocol for scientific instrumentation and data acquisition systems. The recommendations are framed within the broader research objective of minimizing host-device data transfer overhead, a critical factor in accelerating experimental throughput and improving the efficiency of data-intensive research workflows.
Protocol Comparison and Selection Criteria
The following table summarizes the core characteristics of MQTT, gRPC, and Custom UDP to aid in initial protocol selection.
Table 1: Quantitative Protocol Comparison for Research Data Transfer
| Feature | MQTT | gRPC | Custom UDP |
|---|---|---|---|
| Architecture/Model | Publish/Subscribe [41] | Request/Response, Streaming [42] | Connectionless Datagrams [43] |
| Underlying Transport | TCP [41] [44] | HTTP/2 (over TCP) [42] | UDP [43] |
| Header Overhead | Very Low (2-byte header) [41] | Moderate (HTTP/2 headers + Protobuf) | Minimal (UDP header only) |
| Data Serialization | Data-agnostic (Binary, JSON, etc.) [41] | Protocol Buffers (Binary) [42] | Any custom binary format |
| Reliability & Delivery Guarantees | Selectable QoS (0, 1, 2) [44] | Inherent via TCP/HTTP/2 | Unreliable; must be implemented in application [43] |
| Typical Latency | Low [43] | Low [42] | Very Low [43] |
| Ideal Research Scenario | Many devices/sensors streaming to multiple consumers [41] | Microservices, high-performance computing, complex data structures [42] | High-frequency, loss-tolerant real-time data (e.g., video streams) [43] |
Experimental Setup and Validation Methodologies
To validate protocol performance within a research context, the following experimental methodologies are recommended.
Experiment 1: Baseline Bandwidth and Latency Profiling
Objective: To establish quantitative performance baselines for each protocol under controlled network conditions.
Research Reagent Solutions:
- Protocol Implementations: Mosquitto MQTT Broker, gRPC with Protobuf, and a custom UDP socket application.
- Network Emulator: A tool like
tc(Linux traffic control) or Wanem to simulate network constraints. - Data Generator: A script to generate standardized, reproducible data payloads of varying sizes.
- Monitoring Tool: Wireshark for precise packet-level analysis of header overhead and transmission behavior.
Methodology:
- Setup: Configure the network emulator to a pristine, low-latency setting.
- Execution: For each protocol, transmit the standardized data payloads from a client to a server, repeating the process to ensure statistical significance.
- Measurement: Record key metrics for each transmission, including round-trip time (for request/response models), end-to-end latency (for streaming), and total bandwidth consumed.
- Constraint Introduction: Re-run the experiment while systematically introducing network constraints via the emulator, such as limited bandwidth (e.g., 1 Mbps), high latency (e.g., 100ms), and packet loss (e.g., 1%).
- Analysis: Compare the performance degradation of each protocol to identify its operational tolerance for unstable network conditions, a common challenge in lab environments.
Experiment 2: Data Reliability and Integrity Verification
Objective: To stress-test the delivery guarantees of each protocol and verify data integrity under duress.
Methodology:
- Controlled Packet Loss: Use the network emulator to introduce a known percentage of packet loss.
- MQTT QoS Validation: For MQTT, publish a known sequence of messages at QoS 0, 1, and 2. On the subscriber side, verify the receipt of messages, checking for duplicates (QoS 1) and guaranteed, single delivery (QoS 2) [44].
- gRPC Stream Integrity: For gRPC, initiate a long-lived bidirectional stream. Intentionally drop the connection at the network level and monitor the time for the client and server to detect the failure and re-establish the stream, noting any data loss during the interruption [45].
- Custom UDP Application-Level Checks: For the custom UDP implementation, transmit data with sequence numbers and a checksum in the payload. On the receiver, measure the actual packet loss rate and validate the integrity of received packets. Implement and test a simple application-level retransmission mechanism for critical data.
Diagram 1: High-Level Experimental Workflow for comparing MQTT, gRPC, and Custom UDP under various network conditions.
Troubleshooting Guides and FAQs
Frequently Asked Questions (FAQs)
Q1: For a high-throughput sensor network in a lab with an unreliable wireless network, which protocol is most suitable? A1: MQTT is often the optimal choice. Its publish/subscribe model efficiently distributes data from many sensors to multiple consumers [41]. Most importantly, its Quality of Service (QoS) levels allow you to guarantee message delivery for critical data even over unstable links, and its lightweight nature conserves bandwidth and power on constrained devices [44].
Q2: We are building a distributed analysis application where services need to request complex, structured data from each other with low latency. What should we use? A2: gRPC is designed for this scenario. Its use of HTTP/2 provides multiplexing for efficient concurrent requests, and Protocol Buffers offer a fast, compact, and strongly-typed serialization format for complex data structures, reducing parsing overhead and bandwidth compared to JSON [42].
Q3: Our experiment involves streaming high-frequency video data where losing an occasional frame is acceptable, but latency must be absolute minimum. What is the best approach? A3: Custom UDP is the foundational protocol for this use case. Its connectionless nature and lack of retransmission mechanisms provide the lowest possible latency [43]. You can build a custom application on top of UDP that sends video frames as datagrams, accepting some frame loss as a trade-off for real-time speed.
Q4: Our gRPC client frequently experiences long delays after a server pod is restarted in our Kubernetes cluster. What is happening? A4: This is a classic "zombie connection" issue. The gRPC client maintains a long-lived connection, and if the server disappears ungracefully (e.g., hardware failure), the client's TCP stack may not immediately detect the failure [45]. To resolve this, enable gRPC Keepalive settings on both client and server. This forces periodic pings to proactively verify the health of the connection, reducing failure detection time from minutes to seconds [45].
Q5: MQTT clients are unable to connect to the broker with an "identifier rejected" error. How can we fix this?
A5: This is typically a broker misconfiguration. Check the broker's configuration file (e.g., mosquitto.conf) for settings related to client IDs. The issue may be caused by restrictive Access Control Lists (ACLs) or a misconfigured allow_duplicate_client_ids setting if you are attempting to reconnect with a previously used client ID [46].
Troubleshooting Guide: Common Connection Issues
Problem: MQTT Broker Connection Refused
- Step 1: Verify Broker Configuration: Check the broker's configuration file (e.g.,
/etc/mosquitto/mosquitto.conf). Ensure it is listening on the correct IP address (bind_address) and port (default 1883) [46]. - Step 2: Check Authentication: If authentication is enabled, verify the client is providing the correct username and password. Ensure the password file path in the broker config is correct and the file has been created using
mosquitto_passwd[46]. - Step 3: Inspect Firewall Rules: Confirm that firewalls (host-based or network) are not blocking traffic on the MQTT port (1883 or 8883 for SSL).
Problem: gRPC Requests Hanging or Timing Out (DEADLINE_EXCEEDED)
- Step 1: Adjust Client Deadlines: Increase the timeout setting in your gRPC client configuration. However, this may only mask a underlying performance issue [47].
- Step 2: Profile Server Performance: Use profiling tools to identify and optimize expensive or slow server-side methods that are causing the bottlenecks [47].
- Step 3: Implement Keepalive: As detailed in FAQ A4, configure gRPC Keepalive to prevent zombie connections from causing long delays [45].
Diagram 2: Troubleshooting workflow for MQTT broker connection issues.
The Scientist's Toolkit: Essential Research Reagents
Table 2: Key Software and Hardware Solutions for Protocol Implementation
| Item | Function in Research Context |
|---|---|
| Mosquitto MQTT Broker | An open-source broker that acts as the central nervous system for MQTT-based data acquisition, routing messages from publishers (sensors) to subscribers (data analysis services) [46]. |
| gRPC Protocol Buffers (.proto files) | The interface definition language for gRPC. Used to strictly define the methods and data structures of your services, ensuring type-safe and efficient communication between different parts of your analysis pipeline [42]. |
Network Emulator (e.g., tc) |
A critical tool for simulating real-world network imperfections (latency, packet loss, bandwidth limits) in a controlled lab environment to validate protocol robustness. |
| Wireshark | A network protocol analyzer used for deep packet inspection. It is indispensable for debugging protocol behavior, verifying handshakes, and accurately measuring header overhead. |
| TLS/SSL Certificates | The foundational reagent for securing data in transit. Essential for encrypting MQTT (via MQTT over SSL/TLS) and gRPC communications to protect sensitive research data [41] [48]. |
FAQs: Core Concepts and Architecture
Q1: What is the fundamental architectural difference between traditional PIM and CXL-PIM that affects data transfer?
A1: The core difference lies in their memory addressing models. Traditional Processing-in-Memory (PIM) uses disjoint host-device address spaces, requiring explicit data staging—copying inputs to PIM memory before computation and results back to host memory afterward. In contrast, CXL-PIM leverages the Compute Express Link (CXL) standard to create a unified, cache-coherent address space. This allows the host CPU to access device memory directly using standard load/store instructions, eliminating the need for explicit copying and enabling a zero-copy programming model [49] [50].
Q2: What are the three types of Unified Shared Memory (USM) allocations, and when should I use each?
A2: USM provides three allocation types, each with distinct performance characteristics [51]:
| Allocation Type | Host Accessible | Device Accessible | Data Location | Ideal Use Case |
|---|---|---|---|---|
malloc_device |
No | Yes | Device | Kernel-only data; fastest device execution. |
malloc_host |
Yes | Yes (remotely) | Host | Rarely accessed or large datasets not fitting in device memory. |
malloc_shared |
Yes | Yes | Migrates between Host & Device | Data frequently accessed by both host and device; enables zero-copy. |
Q3: Under what workload conditions does CXL-PIM outperform traditional PIM?
A3: CXL-PIM excels with workloads characterized by large dataset sizes, high input/output volumes, and irregular access patterns where explicit staging overhead becomes prohibitive. Research shows that when traditional PIM handles large datasets (e.g., 128GB), host-PIM data transfer can dominate 60-90% of total runtime, causing the system to underperform a CPU baseline. CXL-PIM's unified memory avoids this staging penalty. Conversely, traditional PIM can be better for small, tightly-coupled workloads where its lower access latency is beneficial [49].
Troubleshooting Guides
Problem 1: Poor End-to-End Performance with Traditional PIM
Symptoms: Overall application runtime is slower than a CPU-only baseline, especially as dataset sizes or the number of Processing Units (PUs) increase. Performance profiling shows minimal time spent in actual computation.
Diagnosis: The application is likely bottlenecked by explicit data staging overhead between the host and PIM memory. This is a known structural limitation of conventional DIMM-based PIM architectures [49].
Solution:
- Profile Data Transfers: Use profiling tools (e.g., NVIDIA Nsight Systems) to quantify the time spent in Host-to-PIM and PIM-to-Host transfers [52].
- Explore CXL-PIM Architecture: If your workload involves large data volumes, consider migrating to a CXL-PIM model. The unified address space can amortize higher per-access latency by removing transfer bottlenecks [49].
- Optimize Transfers (if using traditional PIM):
- Combine Transfers: Bundle small, sequential transfers into larger ones to better utilize the link bandwidth [52].
- Overlap Transfers and Computation: Use asynchronous operations to overlap data transfers with computation on the PIM cores where possible.
Problem 2: Suboptimal USM Allocation Strategy
Symptoms: Application performance is lower than expected, with high PCIe utilization or low GPU/PIM utilization.
Diagnosis: An inappropriate USM allocation type is being used, leading to unnecessary data movement or remote access penalties.
Solution: Refer to the USM table above and apply the following decision logic:
- Use
malloc_devicefor data used exclusively within device kernels. - Use
malloc_sharedfor data requiring frequent, fine-grained sharing between host and device, accepting potential page migration costs. - Use
malloc_hostonly for data that is too large for device memory or accessed very infrequently by the device, as it forces slower remote access via PCIe [51].
Problem 3: System Crashes or Incorrect Data with Device Allocations
Symptoms: The program crashes or reads incorrect data when the host CPU tries to access a pointer allocated with malloc_device.
Diagnosis: The host is attempting to directly access a device-only allocation, which is not permitted. Device allocations are not accessible by the host CPU [51].
Solution: Ensure that the host code never dereferences a malloc_device pointer. All data in device allocations must be explicitly copied to a host-accessible allocation (using malloc_host or malloc_shared) before the host can access it.
Experimental Protocols & Performance Analysis
Protocol: Quantifying PIM vs. CXL-PIM Transfer Overhead
Objective: To empirically measure the data transfer overhead in traditional PIM and compare it to the effective access latency in a CXL-PIM model.
Methodology:
- Setup: Configure two experimental platforms: a traditional PIM system (e.g., UPMEM PIM-DIMM) and a CXL-PIM simulator or hardware prototype.
- Workload Selection: Use a range of benchmarks from Table 1 below (e.g., VA, SEL, TRNS) scaled to large dataset sizes (e.g., 128GB) [49].
- Measurement: On the traditional PIM system, use profiling to break down the total execution time into components: Host-PIM Transfer, PIM Execution, PIM-Host Transfer, and Inter-PU Communication. On the CXL-PIM system, measure the total execution time and profile the latency of memory accesses over the CXL link.
- Analysis: Calculate the percentage of time spent in data movement for the traditional PIM system. Correlate the performance delta between the two systems with workload characteristics like data volume and access patterns.
Results Summary: The table below summarizes findings from a large-scale characterization study [49].
| Workload | Dataset Size | Host-PIM Transfer (% of Time) | PIM-Host Transfer (% of Time) | PIM Exec (% of Time) | Dominant Bottleneck |
|---|---|---|---|---|---|
| Vector Addition (VA) | 128 GB | ~40% | ~40% | <15% | Symmetric I/O Transfer |
| Selection (SEL) | 128 GB | ~10% | ~70% | <15% | Large Output Size |
| Transpose (TRNS) | 95.36 GB | ~80% | ~5% | <15% | Large Input Size |
| MLP | 95.36 GB | ~20% | ~20% | ~60% (Inter-PU Comm.) | Synchronization |
The Scientist's Toolkit: Key Research Reagent Solutions
| Item / Platform | Function / Description | Relevance to Research |
|---|---|---|
| UPMEM PIM-DIMM | A commercial DIMM-based PIM platform with disjoint host-device memory spaces. | Serves as a baseline for studying explicit data transfer overhead and traditional PIM performance [49]. |
| CXL Type 3 Device | A CXL device class (e.g., memory expansion module) used for enabling CXL.mem protocol. | Provides memory expansion and pooling, forming the hardware basis for CXL-PIM architectures [50]. |
| CENT Architecture | A CXL-enabled, GPU-free system for LLM inference using hierarchical PIM-PNM design. | A real-world case study for implementing and evaluating CXL-PIM for memory-bound workloads [53]. |
| NVIDIA Nsight Systems | A system-wide performance analysis tool for CUDA applications. | Essential for profiling and identifying bottlenecks in data transfer between host and device [52]. |
| OpenMP USM API | APIs (omp_target_alloc_shared etc.) for managing unified shared memory in OpenMP. |
Provides a standardized programming model for leveraging zero-copy, cache-coherent memory [51]. |
Architectural Visualizations
Implementing Asynchronous Transfers and Pipelining to Overlap Communication and Computation
Frequently Asked Questions
Q1: My application uses GPU acceleration for molecular dynamics, but the overall performance is poor. Profiling shows high data transfer overhead. What is the first thing I should check?
The first thing to check is whether your host memory allocations are pinned (page-locked). Using regular pageable host memory forces implicit synchronization, as the driver must first copy data to a pinned temporary buffer before transfer to the device. Only pinned memory allows for truly asynchronous, non-blocking data transfers via cudaMemcpyAsync in CUDA or analogous functions in other frameworks [54].
Q2: I am using non-default streams and cudaMemcpyAsync, but my communication and computation still do not overlap. What could be the cause?
This is a common issue. Please verify the following three prerequisites [54]:
- Device Capability: Confirm your device supports "concurrent copy and execution." You can check the
deviceOverlapfield in acudaDevicePropstruct. - Stream Assignment: Ensure the kernel and the data transfer you wish to overlap are issued to different, non-default streams.
- Dependency Management: Be mindful of implicit dependencies between operations. Using the default stream (or "null stream") will synchronize all operations across all streams. Also, a kernel launch will wait for all previously issued transfers in its stream to complete.
Q3: What is the practical benefit of overlapping communication and computation in a real-world scientific application like virtual drug screening?
The benefit is a significant reduction in total simulation time. In oneAPI, a technique that breaks data into chunks and pipelines the transfer-compute-transfer steps for each chunk across multiple streams can lead to substantial performance gains. On modern hardware like a Tesla C2050, this approach reduced execution time from about 10 ms to under 6 ms compared to a sequential method, effectively nearly doubling throughput [54]. This allows you to screen more compounds in less time.
Q4: When using multi-GPU systems for large-scale data reduction, what is a major overlooked bottleneck, and how can it be mitigated?
A major bottleneck often overlooked is the overhead of CPU-GPU memory transfers (H2D and D2H), which can consume 34% to 89% of the total pipeline time for state-of-the-art compression algorithms [24]. To mitigate this, use a framework designed to overlap reduction with data transfer. The HPDR framework, for instance, uses an optimized pipeline that reduces data transfer overhead to just 2.3% of the original, accelerating end-to-end throughput by up to 3.5x [24].
Q5: How can I implement a basic pipelining strategy like double buffering in my code?
Double buffering uses two sets of buffers. While the device is computing on one buffer (Buffer A), you can asynchronously transfer the results of the previous computation from a second buffer (Buffer B) back to the host and simultaneously transfer the next chunk of input data from the host to Buffer B. This creates a pipeline where computation on one data chunk overlaps with communication for two others, effectively hiding communication latency [55] [56].
Troubleshooting Guides
Issue 1: Ineffective Overlap Despite Using Asynchronous Functions
Problem Description The user has implemented asynchronous data transfer functions and non-default streams, but profiling tools (like NVIDIA Nsight Systems) show that the data transfers and kernel execution are still executing sequentially, not concurrently.
Diagnostic Steps
- Verify Pinned Memory: Confirm that the host memory pointers used in
cudaMemcpyAsync(or similar) were allocated withcudaMallocHostorcudaHostAlloc(in CUDA) or the equivalent pinned memory function in your programming model (e.g.,sycl::malloc_hostwith a queue in SYCL) [54]. - Inspect Stream Usage: Check that the kernel launch and the
memcpycalls are explicitly assigned to different, non-default streams. Remember that operations in the default stream will cause implicit synchronization. - Check Device Properties: Query the device properties to ensure it supports concurrent copy and execution. This is a hardware prerequisite.
- Review Dependencies: Use a timeline profiler to visualize the execution. Look for unintended dependencies between streams. A kernel in Stream 1 will wait for all previously issued operations in Stream 1 to complete, including data transfers.
Resolution The following code illustrates a correct pattern for overlapping a host-to-device (H2D) transfer, kernel execution, and a device-to-host (D2H) transfer for a single data chunk using explicit stream dependencies.
Issue 2: Performance Degradation After Enabling Overlap
Problem Description After implementing overlapping techniques, the application's total run time increases instead of decreases.
Diagnostic Steps
- Profile for Resource Contention: Overlapping communication and computation increases concurrent access to shared resources like the PCIe bus and DMA engines. This can lead to contention [57].
- Check for Excessive Streams: Creating too many streams can lead to high scheduling overhead and resource fragmentation.
- Analyze Kernel Granularity: If the computational kernel is too small, the overhead of managing and synchronizing streams can outweigh the benefit of overlapping.
Resolution
- Batch Operations: Instead of issuing a transfer and kernel for each tiny piece of data, process data in larger chunks to amortize the launch and synchronization overhead.
- Optimize DMA Priority: On advanced architectures like AWS Trainium, you can adjust the static DMA packet size to prioritize computation DMA rings over communication DMA rings, mitigating resource contention. For example, setting
NEURON_RT_DBG_DMA_PACKETIZATION_SIZE=65536andNEURON_RT_DBG_CC_DMA_PACKET_SIZE=4096can improve performance in systems with both Tensor and FSDP parallelism [57]. - Use a Framework: Consider using a high-performance framework like HPDR [24], which provides an optimized pipeline that automatically handles the overlapping of data transfer and reduction computation, reducing transfer overhead to a minimum.
Issue 3: Application Runs Correctly on One GPU but Fails with Multi-GPU
Problem Description When scaling an application to multiple GPUs, the program crashes, produces incorrect results, or shows poor scalability.
Diagnostic Steps
- Check Data Coherency: In a multi-GPU setup, ensure that the data is correctly partitioned and that each GPU operates on its designated portion. After computation, results must be gathered correctly.
- Verify Peer-to-Peer Access: If GPUs need to access each other's memory directly, ensure that peer-to-peer access is enabled and supported between the GPUs.
- Profile Inter-GPU Communication: Use a profiler to see if the communication between GPUs (or between GPUs and the host) is causing a bottleneck. Collective operations like All-Gather and Reduce-Scatter can become saturated [57].
Resolution
- Implement hierarchical communication patterns that minimize data movement across the PCIe bus. For example, use a single master thread to coordinate data transfers for all GPUs to avoid contention [30].
- For complex parallel patterns like Fully-Sharded Data Parallelism (FSDP), enable multi-stream collective communication. This allows, for instance, Tensor Parallelism communication to happen concurrently with FSDP communication, preventing one from blocking the other and improving overall throughput [57].
Experimental Protocols & Data
Protocol 1: Benchmarking Asynchronous Transfer Strategies
This protocol measures the performance of different data transfer strategies, providing a baseline for optimization.
1. Objective: To quantify the performance gain from overlapping data transfers and kernel execution using non-default streams and pinned memory.
2. Methodology (based on CUDA C/C++):
- Materials: A compute node with a multi-core CPU and one or more NVIDIA GPUs that support concurrent copy and execution.
- Software: CUDA Toolkit, a profiling tool like
nvprofor Nsight Systems. - Procedure:
a. Allocate pinned host memory using
cudaMallocHost. b. Allocate device memory usingcudaMalloc. c. Version 1 (Sequential): In the default stream, perform:cudaMemcpy(H2D)kernel<<<..., ...>>>cudaMemcpy(D2H) d. Version 2 (Naive Async): In a single non-default stream, perform:cudaMemcpyAsync(H2D)kernel<<<..., ..., 0, stream>>>(depends on H2D)cudaMemcpyAsync(D2H) (depends on kernel) e. Version 3 (Pipelined/Overlapped): Split the data intoNchunks. For each chunki, in its own streamstream[i], perform the same sequence as Version 2. This allows transfer for chunki+1to overlap with computation for chunki.
3. Data Analysis: Measure the total execution time for each version. The timeline profiler will visually confirm if operations are overlapping.
Quantitative Results from Literature
| Strategy | Device | Execution Time (ms) | Speedup vs. Sequential | Source |
|---|---|---|---|---|
| Sequential Transfer & Execute | Tesla C1060 | 12.92 | 1.0x (Baseline) | [54] |
| Asynchronous (V1 - Naive) | Tesla C1060 | 13.64 | ~0.95x (Slowdown) | [54] |
| Asynchronous (V2 - Pipelined) | Tesla C1060 | 8.85 | 1.46x | [54] |
| Sequential Transfer & Execute | Tesla C2050 | 9.98 | 1.0x (Baseline) | [54] |
| Asynchronous (V1 - Naive) | Tesla C2050 | 5.74 | 1.74x | [54] |
| Asynchronous (V2 - Pipelined) | Tesla C2050 | Data Incomplete | >1.74x | [54] |
Protocol 2: Evaluating Data Reduction Pipeline Overhead
This protocol helps identify if memory transfer is the bottleneck in a GPU-accelerated data reduction pipeline (e.g., compression).
1. Objective: To profile a data reduction pipeline and determine the fraction of time spent on CPU-GPU memory transfers versus the actual computation.
2. Methodology:
- Materials: A system with a GPU and a data reduction tool like MGARD-GPU or cuSZ.
- Software: Profiling tools (e.g., Nsight Systems,
rocproffor AMD,vtunefor Intel). - Procedure:
a. Run the data reduction (compression) workflow on a representative dataset.
b. Use the profiler to trace the following operations:
- Host-to-Device (H2D) memory transfer
- GPU kernel execution for the reduction algorithm
- Device-to-Host (D2H) memory transfer c. Record the time taken by each operation.
3. Data Analysis: Calculate the percentage of the total pipeline time consumed by memory transfers (H2D + D2H). If this percentage is high (e.g., >30%), the pipeline is memory-transfer bound.
Reported Overhead in Data Reduction Pipelines [24]
| Data Reduction Pipeline | Time Spent on Memory Operations (H2D & D2H) |
|---|---|
| Pipeline A | 89% |
| Pipeline B | 78% |
| Pipeline C | 54% |
| Pipeline D | 34% |
Workflow Visualization
Sequential vs. Overlapped Execution
Diagram 1: Contrasting execution models showing overlapped operations.
Optimized Data Reduction Pipeline
Diagram 2: HPDR-optimized pipeline overlapping transfer and reduction [24].
The Scientist's Toolkit: Essential Research Reagents & Solutions
This table lists key software and hardware "reagents" essential for implementing high-performance overlapped communication and computation.
| Item Name | Function/Benefit | Usage Context |
|---|---|---|
| Pinned (Page-Locked) Memory | Host memory allocated for direct DMA access by the device, enabling asynchronous, non-blocking data transfers. | Foundational requirement for any overlapping strategy in CUDA, SYCL, etc. [54] |
| Non-Default Streams (CUDA) / Asynchronous Handles (SYCL) | Sequences of operations that execute independently from other sequences, allowing concurrency. | Required to isolate communication and computation tasks so they can run in parallel [54]. |
| HPDR Framework | A high-performance, portable data reduction framework that optimizes pipeline to overlap reduction with data transfer. | Mitigates memory transfer bottleneck in data reduction, achieving up to 3.5x faster throughput [24]. |
| Multi-Stream Collective Communication | A hardware/software feature that allows multiple collective communication operations to execute concurrently. | Critical for scaling complex parallel training schemes (e.g., FSDP) on multi-GPU/multi-node systems [57]. |
Environment Variables for DMA Tuning (e.g., NEURON_RT_DBG_DMA_PACKETIZATION_SIZE) |
Adjusts the priority of DMA operations to mitigate resource contention between computation and communication. | Advanced optimization on specific architectures (e.g., AWS Trainium) to prevent performance degradation [57]. |
Advanced Optimization and Troubleshooting for High-Throughput Environments
What are the most common symptoms of a host-device data transfer bottleneck in GPU-accelerated applications?
A host-device data transfer bottleneck occurs when the GPU is forced to remain idle, waiting for data to be copied from the CPU (host) before it can begin processing. This severely undermines computational throughput. The most common observable symptoms are detailed in the table below.
Table: Common Symptoms of a Data Transfer Bottleneck
| Symptom | Description | Typical Tool-Based Observation |
|---|---|---|
| Low GPU Utilization | The GPU's compute units are active for only a small percentage of the total application runtime, showing large gaps of inactivity in a timeline profiler [52]. | Timeline shows significant gaps in kernel execution (blue areas) with high memory transfer activity (green/magenta areas) [52]. |
| High Percentage of Time in Memory Transfers | A disproportionate amount of the application's wall-clock time is spent on cudaMemcpy operations or similar transfer functions [52]. |
Profiler reveals that individual CUDA streams spend over 50% of their time on memory transfers (H2D and D2H) instead of computation [52]. |
| Serialized Execution | Memory transfers and kernel executions happen one after another instead of overlapping, creating a stop-and-start pattern on the GPU [52]. | Timeline shows a pattern: H2D transfer -> kernel execution -> D2H transfer, with each step waiting for the previous to finish completely [52]. |
| CPU Maxed Out During Data Loading | The CPU cores are saturated at 100% usage, often due to data pre-processing or augmentation, while the GPU waits idle [58]. | System monitoring tools show high CPU usage concurrent with low GPU usage, indicating the CPU cannot prepare data fast enough [58]. |
Which tools are essential for profiling and diagnosing data transfer overheads?
Effective diagnosis requires system-level profiling tools that can visualize the interaction between CPU and GPU activities over time. The following table summarizes the key tools and their primary functions.
Table: Essential Profiling Tools for Diagnosing Transfer Overheads
| Tool Name | Primary Function | Key Diagnostic Feature |
|---|---|---|
| NVIDIA Nsight Systems | System-wide performance analysis that correlates CPU, GPU, and memory transfer activities on a single timeline [52]. | Provides a zoomable timeline to visually identify gaps in GPU activity and quantify the time spent in memory transfers versus kernel execution [52]. |
| NVIDIA Data Center GPU Manager (DCGM) | A suite of tools for health monitoring and diagnostics of GPUs in data center environments [58]. | Offers commands like dcgm-diag to check overall GPU health and can help rule out hardware issues while identifying low utilization [58]. |
| NVIDIA NCCL Tests | A suite of benchmarks for testing communication performance between GPUs, crucial for distributed training [58]. | Benchmarks like all_reduce_perf help determine if the network interconnect (e.g., InfiniBand) is a bottleneck in multi-node setups [58]. |
Experimental Protocol: Initial Diagnosis with Nsight Systems
Objective: To identify if host-device data transfer is a primary bottleneck in a molecular dynamics simulation (e.g., GROMACS) or a similar CUDA application.
Methodology:
- Profile Collection: Use the Nsight Systems command-line profiler,
nsys, to collect a trace of the application. A typical command for a molecular dynamics run might be:nsys profile -t cuda,nvtx -s none -o my_trace gmx mdrun -dlb no -notunepme -noconfout -nsteps 3000[52].-t cuda,nvtx: Traces CUDA API calls and user-defined NVTX ranges.-s none: Disables CPU sampling to reduce trace clutter.-o my_trace: Specifies the output report file.
Timeline Analysis: Open the generated
.qdrepfile in the Nsight Systems GUI.- Zoom In: Navigate to a representative, repetitive section of the timeline and zoom in to a resolution of around 100ms to see detailed patterns [52].
- Identify Patterns: Look for the repetitive pattern of memory transfers (H2D in green, D2H in magenta) and kernel executions (blue). Note any large gaps between these activities [52].
- Expand Streams: Expand the "GPU" section to view activity per CUDA stream. Observe if the default stream is inactive and if multiple application streams are serialized on memory transfers [52].
Quantify Overhead:
- Use the shift-drag function to select a single iteration of work (from the end of one D2H transfer to the end of the next).
- The summary will show the total time for the iteration. Within this selection, note the cumulative time spent on memory transfers and the duration of any empty gaps [52].
- In a documented case, this analysis revealed that 3ms of a 19ms iteration was an empty gap, implying a potential 17% performance speedup [52].
What are the primary optimization techniques to reduce data transfer overhead?
Once a bottleneck is confirmed, several optimization strategies can be employed to reduce or hide the latency of data transfers.
Table: Optimization Techniques for Data Transfer Overheads
| Technique | Description | Use Case |
|---|---|---|
| Mapped Memory / Zero-Copy | Uses pinned host memory that can be directly accessed by the GPU kernel, eliminating explicit cudaMemcpy calls and their associated latency [59]. |
Ideal for situations where data must be accessed by the kernel only once or in a random pattern, and the data set is too large to fit in GPU memory all at once [59]. |
| CUDA Graphs | Groups a sequence of dependent kernels and memory transfers into a single, reusable unit. This reduces the launch overhead from the CPU and allows the GPU to execute the workflow more efficiently [59]. | Effective for applications with repetitive execution patterns, as it minimizes the CPU-driven overhead of submitting many small operations individually. Case studies show significant speedups in molecular dynamics workflows [59]. |
| Overlapping Transfers and Computation | Uses multiple CUDA streams to concurrently execute memory transfers and kernels. While one stream is executing a kernel on one batch of data, another stream can be transferring the next batch to the GPU [52]. | Crucial for pipelined workflows. This was a key optimization in GROMACS 2020, where moving transfers to the default stream and resizing them allowed for more parallel kernel execution between streams [52]. |
| Consolidating Transfers | Combines many small memory transfers into fewer, larger transfers. This reduces the overall launch overhead and is more efficient for the PCIe bus [52]. | Applied when an application makes many small, frequent data transfers. GROMACS 2020 optimized performance by batching small transfers into larger ones that better utilize transfer buffers [52]. |
| GPUDirect Storage (GDS) | Enables direct data transfer between storage (e.g., NVMe SSDs) and GPU memory, bypassing the CPU and its memory buffers entirely. This requires supported hardware and software [58]. | Used in high-performance AI training and data analytics to prevent the storage I/O subsystem from becoming a bottleneck when loading large datasets [58]. |
Experimental Protocol: Implementing Mapped Memory
Objective: To eliminate explicit memory transfer time for a data-intensive kernel.
Methodology:
- Allocate Mapped Memory: Instead of using
cudaMallocfor device memory andcudaMemcpyfor transfers, allocate mapped host memory usingcudaHostAllocwith thecudaHostAllocMappedflag. - Get Device Pointer: Retrieve the corresponding device pointer for the allocated host memory using
cudaHostGetDevicePointer. - Kernel Execution: Launch the kernel with the device pointer. The GPU can now directly access the data from the host's pinned memory.
- Synchronize: Use
cudaDeviceSynchronizeafter the kernel launch to ensure the kernel has completed before the host accesses the results. The data, now modified, is immediately available on the host side without a D2H copy. This technique can effectively "eliminate data transfer delays" [59].
Workflow Visualization for Bottleneck Diagnosis and Optimization
The following diagram illustrates a structured workflow for diagnosing and mitigating data transfer bottlenecks, based on the tools and techniques described above.
Diagram: Data Transfer Bottleneck Diagnosis Workflow
The Scientist's Toolkit: Key Research Reagent Solutions
This table lists essential software "reagents" and their function in diagnosing and optimizing data transfer workloads.
Table: Essential Software Tools and Libraries for Profiling and Optimization
| Tool / Library | Function | Role in Experimentation |
|---|---|---|
| NVIDIA Nsight Systems | System-wide performance profiler. | The primary instrument for visualizing the CPU-GPU interaction timeline and quantifying transfer overhead [52]. |
| CUDA Mapped Memory | A feature of the CUDA API. | An experimental reagent to eliminate explicit data copies, enabling zero-copy access to host data from GPU kernels [59]. |
| CUDA Graphs | A feature of the CUDA API. | An optimization reagent that packages workflows into a single unit to reduce CPU launch overhead and improve execution efficiency [59]. |
| NVIDIA NCCL | Collective communications library. | A diagnostic and optimization reagent for testing and enabling high-speed multi-GPU and multi-node communication [58]. |
| CUDA Streams | A feature of the CUDA programming model. | A fundamental reagent for concurrency, enabling the overlap of data transfers and kernel execution [52]. |
Frequently Asked Questions
What are the most common symptoms of high host-device data transfer overhead? Common symptoms include longer-than-expected model inference times, low GPU or accelerator utilization despite high CPU activity, and system latency during large-scale data loading operations. High overhead can manifest as the CPU being maxed out while the accelerator sits idle, waiting for data [60] [61].
How can I quickly diagnose if my storage I/O is a bottleneck?
Use system monitoring tools (e.g., iostat on Linux, Performance Monitor on Windows) to check disk read/write throughput and queue lengths. A bottleneck is likely if the disk utilization is consistently at or near 100% while your accelerator's compute utilization is low [60] [62].
My model loads very slowly. What optimization strategies exist? A fast model loading method that eliminates redundant computations during model verification and initialization can drastically reduce load times. Research has demonstrated techniques that reduce total loading time for large models from over 22,000 ms to approximately 1,040 ms [61].
Can network interface configuration impact my distributed training jobs? Yes, improper configuration can lead to significant bottlenecks. Ensure your network drivers are up-to-date and consider using high-throughput, low-latency network settings. Optimizing network topology and using the correct balance of network protocols for your specific cluster setup is also critical [63].
Why is CPU utilization important when my workload runs on an accelerator? The CPU acts as the command center, managing tasks like data pre-processing, scheduling transfers to the accelerator, and launching kernel functions. If the CPU is overloaded or inefficient, it cannot feed data to the accelerator fast enough, leading to poor overall performance and underutilized hardware [60] [61].
Troubleshooting Guides
Guide 1: Diagnosing and Reducing Host-Device Data Transfer Overhead
Problem: Long wait times for data to move from host memory to accelerator device memory, stalling computation.
Diagnostic Methodology:
- Profile Your Application: Use profilers like NVIDIA Nsight Systems or AMD ROCprof to pinpoint time spent in data transfer functions (e.g.,
cudaMemcpy). Look for long gaps between compute kernels. - Monitor System Metrics: Use tools like
htopor Windows Task Manager to observe CPU utilization during transfers. Correlate high CPU usage with low accelerator usage [60]. - Check Transfer Type: Identify if transfers are synchronous (blocking) or asynchronous. Synchronous transfers are simpler but leave the accelerator idle.
Resolution Strategies:
- Implement Zero-Copy Memory Management: Utilize a zero-copy memory management technique using segment-page fusion. This significantly reduces memory access latency and improves overall inference efficiency by allowing the accelerator to access host memory directly without explicit copies [61].
- Use Asynchronous Transfers: Overlap data transfers with computation on the accelerator using asynchronous memory copy functions and streams.
- Batch Data Effectively: Increase the size of data chunks transferred to amortize the fixed overhead of each transfer over more data.
Guide 2: Tuning CPU Utilization to Feed Accelerators Efficiently
Problem: High CPU utilization (often at 100%) creates a bottleneck, preventing it from scheduling and transferring data to the accelerator efficiently [60].
Diagnostic Methodology:
- Identify Process-Level CPU Consumption: Use tools like
topor Windows Task Manager's "Details" tab to see which processes or threads are consuming the most CPU cycles [60]. - Analyze Kernel Launch Overhead: Profiling tools can show time spent launching kernel functions on the accelerator. A high number of small kernel launches can overwhelm the CPU [61].
Resolution Strategies:
- Optimize Kernel Launch Schedules: Research shows that implementing a multi-tiered scheduling framework on the accelerator's management processing element (MPE) can reduce the number of host-device launches to approximately 1/10,000 of a baseline setup, drastically reducing CPU overhead [61].
- Improve Data Loading Pipelines: Use multi-threading and pre-fetching in your data loaders to parallelize data preparation and reduce wait times for the CPU.
- Process Prioritization: Ensure your application process has appropriate OS priority to minimize context switching and interrupt handling delays [60].
Guide 3: Optimizing Storage I/O for Large-Scale Dataset Access
Problem: Reading training data from disk is slow, causing the entire pipeline to stall.
Diagnostic Methodology:
- Monitor Disk I/O: Use tools like
iostat(Linux) orPerfMon(Windows) to check disk read throughput (MB/s), I/O operations per second (IOPS), and I/O queue lengths. - Check File System and Drives: NVMe SSDs over PCIe 4.0 can reach up to 7,000 MB/s read speeds, significantly outperforming SATA interfaces (around 550 MB/s). Ensure your storage hardware matches your data demands [60].
Resolution Strategies:
- Use Efficient File Formats: Switch to columnar or chunked data formats (e.g., HDF5, Apache Parquet) that allow for faster, compressed reads.
- Implement Intelligent Caching: Cache frequently accessed datasets or pre-processed batches in memory. Tools like Redis or Memcached can be used for hot data [62].
- Database Indexing: If your data is served from a database, ensure that high-read columns and foreign keys are properly indexed to speed up query times [62].
Experimental Protocols & Data
Table 1: Quantitative Results from Transformer Inference Overhead Minimization Study [61]
| Optimization Technique | Metric | Baseline Performance | Optimized Performance | Improvement |
|---|---|---|---|---|
| Three-Tier Scheduling (SWAI MPE) | Host-Device Launches | Baseline (PyTorch-GPU) | ~1/10,000 of baseline | ~10,000x reduction |
| Zero-Copy Memory Management | Memory Access Latency | Not Specified | Significantly Reduced | Major inference efficiency gain |
| Fast Model Loading | Total Model Loading Time | 22,128.31 ms | 1,041.72 ms | ~95% reduction |
Table 2: Key Performance Indicators for Hardware Stack Monitoring [60] [62]
| Component | Key Performance Indicator (KPI) | Warning Zone | Critical Zone | Tool for Measurement |
|---|---|---|---|---|
| CPU | % Utilization | Consistently >85% [60] | Consistently >95% | top, htop, Task Manager |
| Idle Time | Suddenly dips | Consistently <10% | vmstat, PerfMon |
|
| Storage I/O | Disk Read/Write Throughput | Below expected for hardware | At max capacity with high latency | iostat, PerfMon |
| I/O Queue Length | Consistently >1 | Consistently >5 | iostat |
|
| Overall System | Response Time | >200 ms [62] | >1000 ms | Application logs, APM tools |
| Error Rate | >0.1% | >1% | Application logs, APM tools |
Experimental Protocol: Measuring Host-Device Transfer Overhead
Objective: Quantify the latency and throughput of data transfers between host and accelerator memory.
Materials:
- Host system with CPU and accelerator (e.g., GPU, AI accelerator).
- Profiling software (e.g., NVIDIA Nsight Systems,
vTune). - Custom benchmark script.
Methodology:
- Baseline Measurement: Write a script that allocates a large buffer in host memory (e.g., 1 GB). Use a system timer to measure the duration of a synchronous transfer of this buffer to the accelerator. Calculate throughput (Buffer Size / Duration).
- Vary Transfer Sizes: Repeat step 1 with different buffer sizes (e.g., 1 MB, 10 MB, 100 MB, 1 GB) to understand how overhead scales.
- Profile the Transfer: Run the benchmark under a profiler to identify CPU-side bottlenecks during the transfer operation.
- Implement Optimization: Apply an optimization strategy (e.g., pinned host memory for zero-copy transfers). Repeat steps 1-3.
- Compare and Analyze: Compare the throughput and latency metrics before and after optimization to quantify the improvement.
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Software and Hardware for Performance Tuning Research
| Item | Function/Benefit | Example Use-Case |
|---|---|---|
| AI Accelerators (e.g., Shenwei SWAI) | Specialized hardware for high-throughput parallel computation, often featuring dedicated management cores (MPE) for low-overhead scheduling [61]. | Minimizing transformer model inference latency for large-scale NLP tasks in drug discovery. |
| System Profilers | Tools that provide granular timing data on CPU, memory, and accelerator activity, essential for identifying performance bottlenecks. | Diagnosing the exact point of host-device transfer overhead in a custom machine learning pipeline. |
| Third-Party Maintenance (TPM) | Provides expert support and hardware maintenance for existing equipment, enabling performance tuning and life-cycle extension without costly OEM renewals [63]. | Maintaining and optimizing a cluster of older GPU servers for non-critical research workloads. |
| Performance Monitoring Platforms | AI-driven tools that autonomously monitor and adjust resources in real-time to maintain SLOs and optimize performance-cost ratios [62]. | Ensuring consistent performance for a cloud-based molecular modeling application with variable user load. |
| Zero-Copy Memory Techniques | Memory management methods that allow accelerators to directly access host memory, eliminating the need for and overhead of explicit data copies [61]. | Accelerating inference pipelines where data pre-processing on the CPU is a known bottleneck. |
System Optimization Workflow
Host-Device Data Transfer Overhead Analysis
Frequently Asked Questions (FAQs)
Q1: What exactly is the "small file problem" in data transfer? The "small file problem" refers to the significant performance degradation that occurs when transferring a large number of files that are individually much smaller than the storage system's default block size. This happens because each small file consumes an entire block and requires separate read/write operations, encryption overhead, and metadata management, leading to excessive memory use, longer access times, and slower processing. [64] [65]
Q2: Why is solving this problem important in drug development research? In research and development, efficient data flow is critical. Slow transfer of numerous small files—such as genomic sequences, molecular data points, or clinical trial records—creates bottlenecks. This directly impacts productivity, increases operational costs, and can delay critical processes like analysis and modeling, ultimately slowing down the entire drug development pipeline. [64] [66] [67]
Q3: What are the primary causes of slow small file transfers? The main causes include:
- File System Overhead: Systems manage files in fixed-size blocks. Many small files lead to inefficient block utilization and increased read/write operations. [64]
- Storage Hardware Limitations: Hard Disk Drives (HDDs) perform poorly with numerous small, random read/write requests compared to Solid State Drives (SSDs). [64]
- Protocol Inefficiency: Standard protocols like TCP-based FTP/HTTP are designed for reliability over speed, suffering from high latency and poor bandwidth utilization on congested or long-distance networks. [68]
- Antivirus Scanning: Real-time file scanning can consume significant resources, introducing delays during the transfer of many files. [64]
Q4: What is the recommended maximum size and file count for a single batch? While the optimal size can depend on your specific storage system, a general guideline is to batch files that are 1 MB or smaller. It is recommended to limit batches to around 10,000 files, with the total size of each batch being no larger than 100 GB to ensure efficient processing and extraction. [69]
Q5: How do accelerated file transfer protocols achieve higher speeds? These protocols replace or augment traditional TCP with UDP-based foundations, implementing custom flow control, error correction, and congestion control. They use techniques like parallel data streams to utilize multiple network paths simultaneously and checkpoint restart to resume interrupted transfers without starting over, achieving up to 100 times faster speeds than FTP/HTTP. [68]
Troubleshooting Guides
Issue 1: Slow Transfer of Massive Volumes of Small Files
Problem: Transferring thousands of small files (e.g., molecular structure data, lab instrument outputs) is taking too long, creating a bottleneck in your research workflow.
Solution: Implement a file batching strategy.
Step 1: Identify and Group Files Use scripting tools (e.g., Bash, Python) to scan your source directory and identify all files below a size threshold (e.g., 1 MB). Group them logically, such as by experiment date or data type.
Step 2: Create Batched Archives Use archiving tools to combine these small files into a single, larger archive file. Supported formats include TAR, ZIP, and TAR.GZ. [69]
- Linux/macOS Command Example:
- Windows Command Example (using 7-Zip):
Step 3: Transfer the Batched File Transfer the single, large archive using your standard method (e.g., SCP, Aspera, Raysync). This single transfer operation is far more efficient than thousands of individual ones.
Step 4: Auto-extract at Destination (if supported) If your target system supports it, use auto-extraction to return the files to their original, unbatched state. For example, with AWS Snowball, you would use a command like:
bash aws s3 cp experiment_batch_001.tar.gz s3://destination-bucket/ --metadata snowball-auto-extract=true[69]
Issue 2: High Latency and Packet Loss on Long-Distance Networks
Problem: Data transfers between geographically dispersed research sites (e.g., from a CRO in Europe to a sponsor in the US) are slow and unreliable due to network latency and packet loss.
Solution: Tune transfer protocols and leverage acceleration technologies.
Step 1: Diagnose Network Health Use tools like
ping(for latency) andtraceroute(for path analysis) to assess the network connection between source and destination.Step 2: Switch to an Accelerated Transfer Protocol Replace standard protocols (FTP, HTTP/S) with an accelerated solution. These are designed to overcome TCP's limitations over high-latency links. [68]
- Example Solutions: IBM Aspera FASP, FileCatalyst, Raysync, or Signiant. [64] [68]
- Key Mechanism: These protocols use UDP to avoid TCP's built-in congestion control, which mistakenly interprets latency as network congestion and throttles speed. They implement their own proprietary congestion control and error correction. [68]
Step 3: Configure Parallel Streams If your transfer tool allows it, increase the number of parallel streams. This breaks a large file into chunks sent simultaneously, helping to saturate available bandwidth. Refer to your specific tool's documentation to adjust this setting.
Step 4: Enable Checkpoint Restart Ensure this feature is activated. It saves progress during the transfer, allowing it to resume from the point of failure instead of restarting, which is crucial for large transfers over unstable connections. [68]
Experimental Protocols & Data
Protocol 1: Methodology for Evaluating Batching Efficiency
This protocol measures the performance gains from batching small files versus transferring them individually.
1. Objective: To quantify the transfer time difference between batched and individual small file transfers.
2. Materials and Reagents:
- Research Reagent Solutions:
- Computational Cluster: A system with sufficient CPU and I/O capability to handle data compression and network throughput.
- Source and Target Storage: Preferably using SSDs to minimize storage I/O as a confounding variable. [64]
- Archiving Tool: Such as
taror7zip. - Network Monitoring Tool: Like
iftoporwiresharkto monitor bandwidth utilization. - Timer Script: A custom script to precisely measure transfer duration.
3. Experimental Procedure:
a. Dataset Preparation: Create a test set of 10,000 small files (e.g., 50 KB each) in a source directory.
b. Baseline Measurement (Individual Transfers): Initiate transfer of all 10,000 files individually using a standard tool (e.g., scp or rsync). Record the total time (Tindividual).
c. Batching: Create a single TAR archive containing all 10,000 files. Record the time taken for archiving (Tarchive).
d. Batched Transfer Measurement: Transfer the single TAR file. Record the transfer time (Tbatchedtransfer).
e. De-archiving: On the target system, extract the archive. Record the time taken (Textract).
f. Calculation: Total batched time is Tarchive + Tbatchedtransfer + Textract. Compare this to Tindividual.
4. Data Analysis: The table below summarizes hypothetical quantitative outcomes from this experiment.
Table 1: Performance Comparison of Individual vs. Batched File Transfers
| Metric | Individual Transfers | Batched Transfers (TAR) | Improvement |
|---|---|---|---|
| Total Transfer Time | 145 minutes | 12 minutes | 91.7% faster |
| Bandwidth Utilization | ~22% of available bandwidth | ~96% of available bandwidth | 4.4x more efficient |
| CPU Usage | Low | High during archiving/decompression | Increased, but offloaded |
| I/O Operations | 10,000+ | ~2 (for the archive) | Significantly reduced |
Protocol 2: Methodology for Testing Accelerated Transfer Protocols
This protocol evaluates the performance of accelerated UDP-based protocols against traditional TCP-based protocols under simulated network stress.
1. Objective: To compare the transfer speed and reliability of accelerated and traditional file transfer protocols under conditions of high latency and packet loss.
2. Materials and Reagents:
- Research Reagent Solutions:
- Two Networked Hosts: Source and destination machines.
- Network Emulator: A tool like
tc(Linux traffic control) or Wanem to artificially introduce latency and packet loss. - Transfer Software: Install both a traditional tool (e.g., FTP/SCP) and an accelerated tool (e.g., Aspera/FileCatalyst).
- Large Test File: A single, large file (e.g., a 10GB genomic dataset) for transfer.
3. Experimental Procedure: a. Baseline Setup: Configure the network emulator for a low-latency (10ms), low-packet-loss (0%) environment. Transfer the file with both traditional and accelerated protocols to establish a baseline. b. Introduce Network Impairment: Re-configure the network emulator to simulate a long-distance link (e.g., 150ms latency, 2% packet loss). c. Execute Test Transfers: Conduct the file transfer three times with each protocol under the impaired conditions. d. Measure and Record: For each transfer, record the total time taken and the effective throughput (MB/s).
4. Data Analysis: The results will typically show that accelerated protocols maintain high throughput despite network challenges.
Table 2: Protocol Performance Under Network Stress (150ms Latency, 2% Packet Loss)
| Transfer Protocol | Average Transfer Time (10GB file) | Effective Throughput | Stability |
|---|---|---|---|
| FTP (TCP-based) | 120 minutes | ~14.2 MB/s | Frequent timeouts |
| HTTP (TCP-based) | 115 minutes | ~14.8 MB/s | Slow but steady |
| Raysync/Aspera (UDP-based) | 8 minutes | ~208.3 MB/s | Stable, no interruptions |
| FileCatalyst (UDP-based) | 9 minutes | ~185.2 MB/s | Stable, no interruptions |
Workflow Diagrams
Diagram 1: Small File Batched Transfer Workflow
Diagram 2: Accelerated vs. Traditional Protocol Logic
Troubleshooting Guides and FAQs
Frequently Asked Questions
Q1: Our research team has observed a significant increase in data transfer times after implementing the required AES-256 encryption for patient data. What are the most effective strategies to mitigate this without compromising compliance?
A1: The performance impact you're observing is a common challenge. Several effective strategies exist:
- Implement Hardware Security Modules (HSMs): Offload cryptographic operations to dedicated hardware. HSMs securely manage keys and perform encryption/decryption at hardware speeds, significantly reducing CPU overhead on your research workstations [70].
- Adopt a Hybrid Encryption Approach: Use symmetric encryption (AES-256) for the bulk of the data due to its speed, and leverage asymmetric encryption (RSA-2048 or higher) only for securely exchanging the symmetric key. This combines the efficiency of symmetric encryption with the security of asymmetric key exchange [70].
- Utilize TLS 1.3 for Data in Transit: Ensure all data transfers use TLS 1.3, which features a more efficient handshake process than its predecessors, reducing latency during connection setup for repeated data transfers common in research environments [70].
Q2: When transferring large spectroscopic imaging files to a cloud analysis platform, our legacy medical devices cannot support modern encryption protocols. How can we bridge this security gap?
A2: This is a prevalent issue with legacy equipment. The solution involves creating a secure bridge:
- Deploy a Network Security Gateway: Place a secure, compliant network appliance between the legacy device and your cloud connection point. This gateway should be capable of handling modern encryption (like TLS 1.3). The legacy device sends data to the gateway over your local network, and the gateway is then responsible for the secure, encrypted transmission to the cloud [70] [71].
- Enforce Strict Network Segmentation: Ensure the legacy device is on a tightly controlled network segment, isolated from other systems. This limits the potential attack surface if the device itself is compromised [71]. This is a critical mitigation technique, especially given that network intrusions affect 44% of healthcare organizations [72].
Q3: Our automated drug discovery pipeline involves real-time data from connected infusion pumps. We are concerned about the latency from encryption affecting the pipeline's responsiveness. What is your recommendation?
A3: Balancing real-time data flow with security is critical. Your approach should be multi-layered:
- Prioritize Data Classification: Not all data generated requires the same level of protection. Work with your compliance team to classify data in real-time. For example, routine operational metrics might use a lighter encryption profile, while sensitive patient health information (PHI) must always use AES-256 [70] [73].
- Leverage Edge Computing: Perform initial data processing and filtering directly at the edge, near the infusion pumps. This reduces the volume of data that needs to be fully encrypted and transmitted over the network in real-time, minimizing latency for critical alerts [74].
- Implement Robust Key Management: Use a secure key management system to regularly rotate session keys. This maintains security without imposing a constant performance penalty from a single, overused key [70].
Quantitative Data on Encryption Performance
The table below summarizes the performance characteristics of key encryption algorithms as outlined in the 2025 HIPAA guidelines, helping you make informed decisions for your data transfer workflows [70].
| Encryption Type | Algorithm | Key Length | HIPAA 2025 Status | Best Use Case | Performance Impact |
|---|---|---|---|---|---|
| Symmetric | AES-256 | 256-bit | Required | Data at rest, bulk encryption | Minimal |
| Symmetric | AES-128 | 128-bit | Acceptable | Legacy system compatibility | Very Low |
| Asymmetric | RSA-4096 | 4096-bit | Recommended | Key exchange, digital signatures | High |
| Asymmetric | RSA-2048 | 2048-bit | Minimum | Basic key exchange | Moderate |
| Asymmetric | ECC P-384 | 384-bit | Recommended | Mobile devices, IoT | Minimal |
| Transport | TLS 1.3 | Variable | Required | Data in transit | Minimal |
| Transport | TLS 1.2 | Variable | Acceptable | Legacy system support | Minimal |
Experimental Protocol: Measuring Encryption Overhead on Host-Device Data Transfer
This protocol provides a detailed methodology to quantitatively assess the performance impact of encryption on your specific research equipment, providing data-driven insights for optimization.
1. Objective: To measure the latency and throughput overhead introduced by mandatory encryption protocols on data transfers from a representative medical device (e.g., patient monitor, infusion pump) to a research data host.
2. Materials and Setup:
- Device Under Test (DUT): The biomedical device from which data is exported.
- Data Host: A server or high-performance workstation acting as the data receiver.
- Network Environment: A controlled, isolated Gigabit Ethernet network switch.
- Testing Software: A custom script or tool (e.g., a modified
iperf; see "Research Reagent Solutions" below) capable of generating and timing data streams with and without encryption. - Monitoring Tool: System resource monitor (e.g.,
htop, Windows Performance Monitor) to track CPU and memory usage.
3. Methodology:
- Step 1 - Baseline Establishment: Configure the DUT and data host to transfer a standardized, large data set (e.g., a 10GB file of synthetic physiological waveforms) using an unencrypted channel. Record the transfer time and calculate throughput (MB/s). Monitor and record host CPU utilization.
- Step 2 - Encrypted Transfer Test: Re-configure the system to use the required encryption protocol (e.g., TLS 1.3). Transfer the same data set and record transfer time, throughput, and host CPU utilization.
- Step 3 - Hybrid Approach Test (Optional): If applicable, test a hybrid model where data is pre-encrypted on the DUT using AES-256 before transmission over a separate channel.
- Step 4 - Data Analysis: Calculate the performance overhead for each configuration using the formulas:
- Latency Overhead:
((T_encrypted - T_baseline) / T_baseline) * 100 - Throughput Degradation:
((TP_baseline - TP_encrypted) / TP_baseline) * 100 - CPU Load Increase:
(CPU_encrypted - CPU_baseline)
- Latency Overhead:
Research Reagent Solutions
The table below lists key software and hardware "reagents" essential for conducting experiments on data transfer and encryption overhead.
| Item Name | Function / Explanation |
|---|---|
| Hardware Security Module (HSM) | A physical computing device that safeguards and manages digital keys and offloads cryptographic processing from the main host system, drastically reducing encryption overhead [70]. |
| CloudSim with DDoS Extension | A simulation framework for modeling and testing cloud computing environments. A 2025 study used an extended "DDoS-aware CloudSim" to evaluate task scheduler resilience, a method adaptable for testing encryption impact under load [75]. |
Custom iperf Modification |
A network testing tool capable of generating TCP/UDP data streams. It can be modified to log detailed, per-packet timing and CPU usage data, making it ideal for benchmarking encryption overhead in custom host-device setups. |
| Wild Horse Optimizer (A-WHO) | An adaptive metaheuristic scheduler shown in 2025 research to be resilient to performance-degrading attacks. Its principles can be applied to develop intelligent data transfer schedulers that dynamically manage encryption loads [75]. |
| PathoGraph Model | A graph-based neural model from recent anomaly detection research. It demonstrates efficient methods for handling structured clinical data, which can inform the design of data pre-processing steps to reduce payload size before encryption [76]. |
Workflow Diagram for Overhead Mitigation
The diagram below outlines a logical workflow for diagnosing and mitigating encryption overhead in a biomedical research data pipeline.
Data Pre-processing Optimization Pathway
This diagram illustrates a strategic data pathway that minimizes the volume of data requiring full encryption, thereby reducing overall transfer overhead.
Core Concepts: Streams, Threads, and Memory
What is the fundamental difference between a CUDA thread and a CUDA stream?
A CUDA thread is the basic execution element on the GPU. You write kernel code for a single thread, and the CUDA execution model groups these threads into blocks and grids to be executed on the GPU's streaming multiprocessors (SMs). The hardware manages thousands of these lightweight threads to maximize parallel throughput [77].
A CUDA stream is a software abstraction on the host side. It is a sequence of operations (such as memory copies and kernel launches) that execute in issue-order relative to each other. Streams allow for concurrency within a single GPU context by enabling operations in different streams to potentially execute concurrently, thus overlapping data transfers and kernel execution [77] [78].
Why is data transfer between the CPU and GPU often a major bottleneck?
Host (CPU) and device (GPU) have separate physical memories [6]. By default, data transfers between them use pageable host memory. The operating system can move this memory around in physical RAM or even swap it to disk, which introduces latency and makes it inefficient for high-throughput data transfer to the GPU [79].
The cost of these transfers can dominate the total execution time. Performance profiles often show cudaMemcpy operations consuming a large portion of the application's timeline. For instance, one developer reported that cudaMemcpy operations accounted for over 93% of their API call time [80].
What is pinned (page-locked) memory and how does it help?
Pinned memory (or page-locked memory) is host memory that is locked in RAM and cannot be paged out by the operating system. CUDA uses this memory to perform Direct Memory Access (DMA), which allows data to move between CPU and GPU directly without going through intermediate CPU buffers [79].
Benefits:
- Higher Transfer Bandwidth: Pinned memory can dramatically increase bandwidth for host-to-device transfers [79].
- Enables Overlap: It is a prerequisite for using
cudaMemcpyAsyncand overlapping data transfers with kernel execution [80].
Considerations:
- It consumes more system resources and has allocation limits compared to pageable memory [79].
- Allocation time is higher, so for a single use, it may not provide a significant win. The benefits are most pronounced with repeated use [80].
Implementation & Configuration
How do I implement basic overlapping of data transfer and computation using streams?
The standard methodology is to break the work into chunks and process one chunk at a time using multiple streams. The following workflow illustrates this process for two concurrent streams, enabling the overlap of data transfer for one chunk with kernel execution on another.
The corresponding code structure for this approach is as follows:
Should I use a single thread with multiple streams or multiple threads with one stream each?
The choice depends on your application's structure and the hardware. The table below summarizes a comparative experiment on an Intel i9-9900K CPU and NVIDIA RTX 2080 Ti GPU [81].
Table: Performance comparison of multi-threaded vs. multi-stream approaches
| Configuration | Description | Key Finding | Considerations |
|---|---|---|---|
| Single-Thread, Multi-Stream | One CPU thread manages multiple CUDA streams. | Can effectively overlap copy and compute [81]. | Simpler synchronization. May be sufficient for many applications. |
| Multi-Thread, Single-Stream | Multiple CPU threads, each owning a single CUDA stream. | Can lead to higher host-side throughput by leveraging CPU parallelism. | Warning: CUDA API calls from multiple threads may introduce synchronization overhead and latency (~2µs per call) [82]. |
Recommendation: If you are unsure, start with a single-threaded, multi-stream approach. If the host-side processing becomes a bottleneck, then consider multiple threads, but be aware of potential API call latency. Issuing all work from a single thread can mitigate variation in latency [82].
What are the essential tools and reagents for optimizing CUDA data flow?
Table: Essential "research reagents" for CUDA data transfer optimization
| Tool / Reagent | Function | Key Use Case |
|---|---|---|
| Pinned (Page-Locked) Memory | Host memory locked in RAM, enabling fast DMA transfers. | Mandatory for asynchronous cudaMemcpyAsync and overlap [79]. |
| CUDA Streams | Software abstraction for concurrent sequences of operations. | Managing concurrent data transfers and kernel execution [78]. |
| CUDA Events | Synchronization primitives placed into streams. | Precisely timing operations or making one stream wait for a point in another [78]. |
| NVIDIA Nsight Systems | System-wide performance analysis tool. | Profiling to identify bottlenecks and verify overlap is occurring [83]. |
| CUDA Device Properties | Queried capabilities of the GPU. | Checking concurrentKernels and asyncEngineCount to verify hardware support for overlap. |
Experimental Protocols & Analysis
What is a standard protocol for demonstrating stream overlap?
This protocol provides a methodology to quantify the performance benefits of using multiple streams.
Objective: To measure the reduction in total execution time achieved by overlapping data transfers with kernel computation using multiple CUDA streams.
Materials:
- Host system with a CUDA-capable NVIDIA GPU.
- CUDA Toolkit installed.
- The "research reagents" listed in the table above.
Methodology:
- Baseline Measurement: Implement a version of your algorithm that uses a single stream (the default stream). Process all data with synchronous
cudaMemcpycalls. Measure the total execution time. - Pinned Memory Allocation: Modify the code to allocate host arrays using
cudaMallocHost. - Stream Creation: Create multiple CUDA streams (e.g., 2, 4, 8) using
cudaStreamCreate. - Work Decomposition: Divide the input and output arrays into contiguous chunks. The number of chunks should be an integer multiple of the number of streams.
- Asynchronous Execution: For each chunk, use
cudaMemcpyAsyncand launch the kernel into a specific stream, cycling through the available streams. - Synchronization: Use
cudaStreamSynchronizeon all streams after all operations have been issued. - Experimental Measurement: Run the multi-stream version and measure the total execution time. Compare it to the baseline.
Expected Outcome: A significant reduction in total wall-clock time for the multi-stream version compared to the single-stream baseline, as data transfers and kernel executions from different streams overlap in the GPU's execution timeline.
How can I present quantitative results from stream experiments?
After running the experimental protocol, you can summarize your findings in a table. The following is an example based on a common performance profile.
Table: Example time profile breakdown for a data-intensive application
| Operation Type | Time in Single-Stream Setup | Time in Multi-Stream Setup | Notes |
|---|---|---|---|
| Host-to-Device Memcpy | 1.06 s (67.9%) | ~0.75 s | Overlapped with compute, reducing effective wait time. |
| Kernel Execution | 251.30 ms (16.0%) | ~251.30 ms | Largely unchanged. |
| Device-to-Host Memcpy | 252.32 ms (16.1%) | ~180 ms | Overlapped with later H2D copies and compute. |
| Total Wall-Clock Time | ~1.56 s | ~1.10 s | Achieved speedup: ~1.4x. |
Note: Example data is adapted from a real-world profile where data transfer was the dominant cost [80].
Troubleshooting FAQs
I implemented multiple streams, but Nsight Systems shows no overlap. Why?
This is a common problem with several potential causes:
- Insufficient use of pinned memory: This is the most common error. Asynchronous transfers
cudaMemcpyAsyncrequire the host memory to be allocated withcudaMallocHost. Using ordinarymallocwill force the operation to be synchronous [79]. - Dependence on the default stream: The default stream (stream 0) has special synchronization semantics. If you launch a kernel in a non-default stream but then use a
cudaMemcpy(without a stream parameter) or a kernel in the default stream, the default stream operation will wait for all previous operations in all streams to finish, breaking concurrency. Consistently use non-default streams for all operations you wish to overlap. - Hardware limitations: Verify that your GPU supports true concurrency. Check the
deviceOverlapandasyncEngineCountproperties using the CUDAdeviceQuerysample. - Resource contention: If kernels in different streams use excessive amounts of shared resources like shared memory or registers, the GPU scheduler may not be able to run them concurrently [78].
My multi-threaded application has high latency when threads call CUDA APIs. Why?
Any CUDA API call may block or synchronize for various reasons related to contention for internal resources [82]. When multiple CPU threads in the same process issue commands to the same GPU context, the driver may need to serialize them internally, causing microsecond-level pauses in the calling threads [82].
Solution: To mitigate this, consider consolidating CUDA API calls (like cudaMemcpyAsync and cudaLaunchKernel) to a single CPU thread dedicated to managing GPU work. Other threads can prepare data and then pass tasks to this manager thread. This reduces contention and variation in latency [82].
How do CUDA streams interact with accelerated libraries like cuFFT?
Many CUDA libraries, such as cuFFT and cuBLAS, are stream-aware. They allow you to set the stream in which their computations will execute using functions like cufftSetStream() [77].
Best Practice: To integrate a library call into a concurrent workflow, assign it to a non-default stream. This allows the library's computation to overlap with data transfers or kernels in other streams. Ensure that any data the library operates on has been transferred to the device in the same stream (or a preceding, synchronized stream) using asynchronous copies.
Benchmarking and Validation: Measuring Strategy Efficacy in Research Contexts
FAQs on Performance Baselines for Data-Intensive Research
What is a performance measurement baseline and why is it critical for my research on data transfer overhead?
A Performance Measurement Baseline (PMB) is a combination of your project's scope, schedule, and cost baselines [84]. In the context of your research, it translates to defining the initial, stable measurements for latency, throughput, and resource utilization before you implement any optimizations [84]. This baseline serves as an objective yardstick. It helps you determine if the changes you make—such as using a new decompression engine or a different memory allocator—genuinely improve performance or introduce regressions. Without it, quantifying the impact of your research on reducing host-device data transfer overhead is nearly impossible.
What are the most common performance bottlenecks when establishing a baseline for GPU-accelerated workflows?
Common bottlenecks often relate to inefficient data movement and resource contention [7] [8]:
- Excessive Host-Device Data Transfer: Copying data between the CPU (host) and GPU (device) is a major source of latency. The baseline should measure the time spent on these transfers [8].
- Suboptimal Buffer Allocations: Using standard
cudaMallocinstead of allocations compatible with hardware accelerators like the NVIDIA Blackwell Decompression Engine can force fallbacks to slower software paths, reducing throughput [7]. - Unbalanced Workloads: If your GPU kernels do not create enough concurrent tasks to keep all compute resources busy, utilization will be low, and latency will be high [8].
- Incorrect Memory Access Patterns: Accessing memory with a stride that causes multiple compute cores to contend for the same memory bank can drastically slow down performance [8].
How can I accurately measure throughput and latency in a distributed research environment?
Accurately measuring these metrics requires using the right tools and understanding their definitions [85]:
- Latency is the time taken for a single operation to complete, measured in milliseconds (ms). You can measure it using tools like
ping,iPerf, or profilers like Intel VTune [8] [85]. - Throughput is the number of operations processed per unit of time, measured in requests per second (RPS) or transactions per second (TPS). Tools like
JMeter,k6, orLoadRunnercan simulate load and measure throughput [85].
The key is to measure both metrics together, as they are interdependent. A graph plotting latency against throughput under increasing load will clearly show your system's performance envelope and breaking point [85].
Troubleshooting Guides
Problem: High latency and low throughput during host-to-device data decompression.
This is a classic symptom of data transfer bottlenecks. The following workflow outlines a systematic approach to diagnose and resolve this issue:
Diagnosis and Solution:
- Minimize Data Transfer: The primary goal is to reduce the volume of data moved across the PCIe bus. Use hardware decompression engines, like the one on the NVIDIA Blackwell architecture, to decompress data in transit without first performing a host-to-device copy [7].
- Use Compatible Memory Allocations: To leverage hardware accelerators, you must use specific allocation types. Replace standard
cudaMallocwithcudaMallocFromPoolAsyncorcuMemCreate, ensuring you use the flagscudaMemPoolCreateUsageHwDecompressorCU_MEM_CREATE_USAGE_HW_DECOMPRESS[7]. - Optimize Buffer Batching: If your workload involves many small buffers, the launch overhead can be significant. For best performance, ensure your batch of buffers (input, output, sizes) are pointers offset into a single, large allocation rather than coming from many separate allocations [7].
Problem: Low GPU utilization despite high computational workload.
Low utilization indicates that the GPU's compute resources are idle, often due to poor workload partitioning or synchronization issues.
Diagnosis and Solution:
- Profile to Identify Hotspots: Use profiling tools like Intel Advisor or Intel VTune Profiler to analyze your code. Look for kernels with low occupancy and identify the ratio of memory access to computation [8].
- Increase Parallelism: GPUs excel when there is a massive amount of parallelism. Structure your computation to create many more independent tasks than there are available compute resources. This allows the hardware scheduler to keep all cores busy as tasks complete [8].
- Minimize Host-Device Synchronization: Every time the host CPU launches a kernel and waits for it to finish, it incurs overhead. Restructure your code to launch larger kernels or use asynchronous operations to minimize the number of kernel launches [8].
- Keep Data on the Device: Avoid transferring intermediate results back to the host between computations. Design your workflow to chain operations on the GPU, only copying back the final result [8].
Quantitative Performance Metrics
Table 1: Key Metrics for Establishing a Performance Baseline
| Metric Category | Specific Metric | Definition & Measurement Unit | Target/Benchmark |
|---|---|---|---|
| Latency | Request Latency | Time for a single request/operation to complete. Measured in milliseconds (ms) [85]. | < 100 ms for a responsive user experience [86]. |
| Token Processing Time | Overhead introduced by rate-limiting or processing logic. Measured in milliseconds (ms) [86]. | < 5 ms to minimize system overhead [86]. | |
| Throughput | System Throughput | Number of requests processed per unit of time. Measured in Requests/Second (RPS) or Transactions/Second (TPS) [85]. | Target depends on system capacity; should be stable or increasing with load until saturation [85]. |
| Data Decompression Throughput | Volume of data processed per second. Measured in Megabytes/Second (MBps) or Gigabytes/Second (GBps) [7] [87]. | Compare software (SM) vs. hardware (DE) decompression performance [7]. | |
| System Resource Utilization | GPU Utilization | Percentage of time GPU compute units are busy. | Aim for consistently high utilization (e.g., >80%) during compute phases [8]. |
| CPU Utilization | Percentage of CPU resources used. | 60-80% to balance efficiency with system headroom [86]. | |
| Memory Bandwidth | Rate of data read from/written to memory. Measured in GBps. | Monitor for bottlenecks; compare against hardware's peak bandwidth. | |
| Success & Compliance | Request Success Rate | Percentage of requests processed successfully [86]. | > 99.9% for high system reliability [86]. |
| Hardware Decompression Max Size | Maximum buffer size supported by hardware decompression engine. Measured in Megabytes (MB) [7]. | Query via CU_DEVICE_ATTRIBUTE_MEM_DECOMPRESS_MAXIMUM_LENGTH (e.g., 4 MB on B200) [7]. |
Table 2: Experimental Protocols for Key Performance Experiments
| Experiment Objective | Methodology & Workflow | Tools Required | Key Performance Indicators (KPIs) to Record |
|---|---|---|---|
| Compare Decompression Methods | 1. Allocate input/output buffers using HW-compatible methods (e.g., cudaMallocFromPoolAsync).2. Transfer compressed data to device.3. Decompress using both software (SM) and hardware (DE) paths.4. Measure end-to-end time. |
nvCOMP library, NVIDIA Blackwell GPU (or similar), cudaEvent timers [7]. |
• Decompression Throughput (GBps)• End-to-end Latency (ms)• GPU Utilization during task |
| System Load & Saturation Analysis | 1. Use a load testing tool to simulate increasing concurrent users/requests.2. For each load level, measure throughput and latency simultaneously.3. Incrementally increase load until throughput peaks and latency spikes. | k6, JMeter, or LoadRunner [85]. | • Throughput (RPS) at each load level• Average and P95 Latency (ms) at each load level• System resource (CPU, RAM) usage |
| Data Transfer Overhead Assessment | 1. Run a GPU kernel with data already on the device (baseline).2. Run the same kernel, but include host-to-device data transfer before kernel launch.3. Compare total execution times. | Profiler (e.g., Intel VTune, NVIDIA Nsight Systems), custom timers [8]. | • Kernel execution time (ms)• Data transfer time (ms)• Total workflow time (ms) |
The Scientist's Toolkit: Essential Research Reagents & Solutions
Table 3: Key Software and Hardware Solutions for Performance Research
| Tool / Solution | Function in Research | Application Context |
|---|---|---|
| nvCOMP Library | Provides GPU-accelerated compression and decompression routines. Automatically leverages hardware decompression engines when available [7]. | The primary API for integrating high-speed decompression into data pipelines, crucial for reducing data transfer volume. |
| Hardware Decompression Engine (DE) | A fixed-function hardware block (e.g., on NVIDIA Blackwell) that offloads decompression of Snappy, LZ4, and Deflate formats from the main compute cores [7]. | Used to investigate the performance benefits of hardware offloading for data-intensive workloads like LLM training and genomics. |
| Intel oneAPI Toolkits | A cross-architecture programming model and toolset. Includes profilers (VTune, Advisor) and compilers for performance analysis and code optimization on GPUs and CPUs [8]. | Used for identifying performance hotspots, analyzing memory access patterns, and projecting performance on different accelerators. |
cudaMallocFromPoolAsync / cuMemCreate |
Memory allocation functions that, with specific flags, create buffers compatible with hardware accelerators like the Decompression Engine [7]. | Essential for ensuring memory allocations are optimized for use with fixed-function hardware, avoiding fallbacks to slower software paths. |
| Asynchronous Processing & Streams | A programming model that allows data transfers and kernel computations to occur concurrently, hiding latency [8]. | Applied to improve overall workflow throughput by overlapping data movement with computation. |
Technical Support Center
Frequently Asked Questions (FAQs)
FAQ 1: What is data reduction and why is it critical for reducing host-device data transfer overhead?
Data reduction involves minimizing the size of datasets while retaining their essential information [88]. In the context of host-device communication, this technique is vital for optimizing bandwidth consumption, decreasing the computational load on systems, and reducing cloud storage costs. Strategically, this is often implemented in middle servers or gateways, where data is compressed or aggregated before being sent to the cloud, thereby significantly improving transfer efficiency [31].
FAQ 2: What is the fundamental trade-off between bandwidth savings and data accuracy?
The core trade-off lies in choosing between lossy and lossless techniques. Lossless compression preserves all original data, ensuring perfect accuracy but typically offering more modest bandwidth reduction. Lossy techniques, such as filtering or aggregation, can achieve substantial bandwidth savings (often over 90%) but may result in some loss of information or introduce a degree of inaccuracy (e.g., 4.74% data loss in one studied approach) [31]. The choice depends on the specific accuracy requirements of your application.
FAQ 3: Which data reduction technique offers the best balance for high-velocity sensor data?
Prediction-based data reduction approaches can be highly effective for streaming data from sensors. However, their performance is not universal; the efficiency in reducing transmissions depends heavily on the sensed phenomena, user requirements, and the specific architecture used to make the predictions [31]. There is no single "best" technique, and experimentation is required for your specific dataset.
FAQ 4: How can I quantify the performance of a data reduction technique in my experiments?
Two primary metrics are used to evaluate and compare techniques [31]:
- Data Size Reduction: The percentage-based decrease in data volume after reduction.
- Data Accuracy: The fidelity of the reduced dataset to the original, also expressed as a percentage.
Troubleshooting Guides
Problem: High bandwidth usage persists despite applying a data reduction technique.
- Potential Cause 1: The technique may be lossless, which has a lower maximum reduction potential.
- Solution: If your application allows, consider a lossy technique (e.g., aggregation, symbolic approximation) that can achieve higher compression ratios [31].
- Potential Cause 2: The technique is not suited to the data type.
- Solution: Experiment with different techniques. For example, use dimensionality reduction for high-heterogeneity data and deduplication for data with many duplicates [31].
Problem: Data accuracy after reduction is unacceptable for analysis.
- Potential Cause: The parameters of a lossy technique are too aggressive, discarding too much information.
- Solution: Adjust the error bounds or tolerance parameters of the reduction algorithm. For instance, in a two-stage compressor, you could dynamically switch from lossy to lossless parameters to better preserve critical data segments [31].
Problem: Implementing data reduction at the sensor node is draining battery life too quickly.
- Potential Cause: The computational overhead of the chosen compression algorithm is too high for the sensor's hardware.
- Solution: Investigate less computationally intensive algorithms or shift the data reduction process to a middle server or gateway that has more processing power and energy resources [31].
Comparative Analysis of Techniques
The table below summarizes the performance of various data reduction techniques as found in the literature, providing a benchmark for your experiments.
Table 1: Performance Comparison of Data Reduction Techniques
| Technique / Approach | Data Reduction Percentage | Data Accuracy | Key Characteristics |
|---|---|---|---|
| SAX + LZW Compression [31] | > 90% | ~95.26% (Worst-case loss: 4.74%) | Two-stage process: lossy symbolic aggregation followed by lossless compression. |
| Spatiotemporal (K-Means + Similarity) [31] | ~54% | ~95% | Preserves location (spatial) and time-based (temporal) information. |
| Fast Error-Bounded Lossy Compression [31] | Up to 103x | 98% | Specifically suited for multisensory reading compression; improves energy efficiency. |
| Feature Selection (Forward Feature Elimination) [31] | 68% | Not Specified | A dimensionality reduction technique that selects the most relevant features from a dataset. |
Experimental Protocols
This section provides detailed methodologies for key experiments cited in the comparative analysis.
Protocol 1: Evaluating a Two-Stage Compression Technique (SAX + LZW)
- Objective: To assess the reduction in data volume and potential data loss from a lossy quantization stage followed by a lossless compression stage.
- Materials: Time-series sensor data, computing node (e.g., sensor or gateway).
- Procedure [31]:
- SAX Quantization: Apply the Symbolic Aggregate Approximation (SAX) method to the raw sensor readings. This step transforms the time-series data into a string of symbols, minimizing its dynamic range (this is the lossy step).
- LZW Compression: Apply the Lempel-Ziv-Welch (LZW) lossless compression algorithm to the output string from step 1.
- Transfer & Decompress: Transfer the compressed data to the host device and perform decompression (reversing step 2).
- Metrics Calculation: Calculate the Data Size Reduction percentage by comparing the original and final data sizes. Calculate Data Accuracy by comparing the reconstructed signal to the original.
Protocol 2: Implementing a Spatiotemporal Data Reduction Approach
- Objective: To reduce structured IoT data while preserving essential location and time-based information.
- Materials: IoT-structured dataset with spatial and temporal components.
- Procedure [31]:
- Spatial Treatment (K-Means): Apply the K-Means clustering algorithm to the spatial data to group locations and preserve key location information.
- Temporal Treatment (Similarity Check): Apply a data similarity technique on a time basis to group or filter data points, preserving temporal patterns.
- Data Aggregation: Combine the results from the spatial and temporal processing to form the final, reduced dataset.
- Validation: Calculate the overall data reduction and accuracy against the original dataset.
Experimental Workflow Visualization
The following diagram illustrates a generalized, high-level workflow for conducting experiments that compare different data reduction techniques.
Data Reduction Experiment Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials and Methods for Data Reduction Research
| Item / Concept | Function in Experiment |
|---|---|
| Time-Series Dataset | Serves as the raw input data for testing reduction techniques, typically representing sequential measurements from sensors or devices. |
| Symbolic Aggregate Approximation (SAX) | A lossy technique that converts time-series data into a symbolic string, reducing its complexity and dynamic range as a pre-processing step [31]. |
| Lempel-Ziv-Welch (LZW) Compression | A lossless compression algorithm used to further reduce the size of data after an initial processing step, ensuring no further data loss [31]. |
| K-Means Algorithm | A clustering algorithm used in data reduction to group similar data points, often applied to spatial data to preserve essential location information with fewer data points [31]. |
| Principal Component Analysis (PCA) | A dimensionality reduction technique that transforms a large set of variables into a smaller one, preserving as much variance as possible, making data easier to process and analyze [31]. |
| Error-Bounded Lossy Compressor | A type of lossy compression algorithm that allows the user to set a maximum acceptable error, providing a direct trade-off control between accuracy and compression ratio [31]. |
Frequently Asked Questions
Q1: My large-scale genome assembly runs slower on a PIM system than on my CPU. Why does this happen, and how can I fix it?
This occurs due to the disjoint address spaces in conventional Processing-in-Memory (PIM) architectures. Your data must be explicitly transferred between host and PIM memory before and after computation [49]. For large datasets, this staging overhead dominates total execution time. To resolve this:
- Solution A: Utilize CXL-PIM if available. The Cache-Coherent Unified Address Space of CXL-PIM eliminates explicit staging transfers, directly addressing this bottleneck [49].
- Solution B: Optimize data allocation. If using conventional PIM, batch your data transfers to overlap communication with computation where possible, reducing the perceived overhead.
Q2: What is the fundamental architectural difference between PIM and CXL-PIM that I should consider for my experimental design?
The core difference lies in their memory model:
- Conventional PIM uses disjoint host-device address spaces. You must manually manage data movement via Direct Memory Access (DMA) transfers, which is efficient for very small, compute-intensive kernels but becomes a bottleneck for large inputs/outputs [49].
- CXL-PIM provides a unified, cache-coherent address space. The host CPU can access device memory directly using standard load/store instructions, removing the need for explicit copies. This simplifies programming but may have higher per-access latency over the CXL link [49] [53]. Your choice should depend on the data-intensity and access patterns of your bioinformatics workload.
Q3: For which specific biomedical workloads is CXL-PIM the superior choice?
CXL-PIM shows significant advantages for workloads with:
- Large dataset sizes that exceed host cache capacity.
- Low operational intensity (i.e., low data reuse), making them memory-bound.
- Unpredictable or fine-grained access patterns that are difficult to optimize with batched DMA transfers in conventional PIM. Prime examples include scanning large genomic databases (e.g., for sequence alignment), processing high-resolution medical images, and running inference with large language models on biomedical literature [89] [53].
Q4: When should I prefer a traditional PIM architecture over a CXL-PIM one?
Stick with conventional PIM for workloads characterized by:
- Small, compute-intensive kernels where the compute time can amortize the fixed cost of data transfer.
- Very regular, predictable data access patterns that can be perfectly optimized for batched DMA transfers.
- Scenarios where the highest possible memory bandwidth to local DRAM banks is critical, and the higher latency of CXL's unified access is detrimental [49].
Troubleshooting Guides
Issue 1: Poor Performance Scaling with Increased PIM Cores
Problem: Adding more Processing Units (PUs) or DRAM Processing Units (DPUs) to your PIM system does not improve performance; sometimes it even makes it worse [49].
Diagnosis: This is a classic symptom of the data transfer bottleneck. The host CPU's memory bandwidth, or the interface connecting it to the PIM modules, is saturated by the staging of input and output data. The time spent moving data overshadows the computation speed gained from extra cores [49].
Resolution:
- Profile your application: Measure the time spent in
Host–PIMandPIM–Hosttransfers versusPIM Execution. If transfers consume over 60% of the time, your workload is transfer-bound [49]. - Reduce staging frequency: Re-structure your algorithm to perform more computation per unit of data transferred. Process larger chunks of data within PIM memory before sending results back.
- Consider CXL-PIM: If algorithm optimization is insufficient, migrate to a CXL-PIM architecture. Its unified memory model removes explicit transfers, directly solving this scaling issue [49].
Issue 2: High and Unpredictable Latency in Memory Accesses
Problem: Memory read/write operations on your CXL-PIM device sometimes have high, variable latency.
Diagnosis: This is an inherent trade-off of the CXL-PIM model. While it eliminates staging, each memory access traverses the PCIe-based CXL link, which has higher latency than accesses to local CPU memory or a PIM core's local bank [49]. The operating system's page fault and migration mechanism can also contribute to latency variability [90].
Resolution:
- Improve data locality: Optimize your code for spatial and temporal locality to benefit from CPU cache hierarchies and reduce the frequency of CXL accesses.
- Use large, contiguous memory allocations: This helps the CXL memory manager operate more efficiently.
- For transfer-bound workloads on conventional PIM, the total latency may still be lower with CXL-PIM despite higher per-access latency, because the costly staging phase is removed [49].
Issue 3: Inefficient Execution of Complex Operations on PIM Cores
Problem: Kernels involving complex operations (e.g., Softmax, square root, division) run inefficiently on the simple PIM processing cores.
Diagnosis: Conventional PIM cores are often lightweight and optimized for high-throughput, simple operations (like MAC operations), not complex, control-heavy tasks [53].
Resolution:
- Adopt a hybrid processing model: Offload simple, parallelizable operations (like matrix multiplication) to the PIM cores and leave complex operations to be executed on the host CPU or a specialized near-memory accelerator.
- Leverage a hierarchical PIM-PNM architecture: Some modern systems, like CENT, combine PIM cores (for high-bandwidth math) with more powerful Processing-Near-Memory (PNM) units (e.g., RISC-V cores or custom accelerators) in the memory controller to handle special functions efficiently [53].
Experimental Data & Performance Comparison
Table 1: Quantitative Comparison of PIM and CXL-PIM Architectures
| Metric | Conventional PIM (e.g., UPMEM) | CXL-PIM (e.g., CENT) | Notes |
|---|---|---|---|
| Address Space Model | Disjoint | Unified, Cache-Coherent | Fundamental difference affecting programmability [49] |
| Data Transfer Model | Explicit Staging (DMA) | Direct Load/Store | CXL-PIM eliminates staging overhead [49] |
| Typical Transfer Overhead | 60-90% of total runtime [49] | None (integrated into access latency) | For large-scale, memory-bound workloads |
| Scalability with more Cores | Poor (due to transfer bottleneck) [49] | Good | CXL-PIM performance scales more linearly with compute units |
| Ideal Workload Type | Compute-intensive, small I/O | Memory-bound, large dataset, low operational intensity [53] | |
| Sample Performance (vs CPU) | Can be slower than CPU for large data [49] | 2.3x higher throughput for LLM inference [53] | Workload-dependent |
Table 2: Essential Research Reagents & Tools
| Item | Function/Benefit | Example Use Case |
|---|---|---|
| PrIM Benchmark Suite [91] [92] | First benchmark suite for real-world PIM; contains 16 memory-bound workloads from various domains. | Characterizing PIM performance on bioinformatics, graph processing, and linear algebra. |
| UPMEM PIM Hardware [49] [91] | The first publicly-available real-world PIM architecture for experimental validation. | Running large-scale experiments and collecting performance data on conventional PIM. |
| CENT Simulator [53] | An open-source simulator for CXL-enabled, PIM-based systems. | Exploring CXL-PIM design space and performance for LLM and large-model inference. |
| CXL System Profiler [89] | A profiling framework to analyze the microarchitecture and latency of CXL devices. | Understanding performance bottlenecks and access patterns in CXL-PIM systems. |
Detailed Experimental Protocols
Protocol 1: Characterizing Data Transfer Overhead in PIM
Objective: To quantify the performance bottleneck caused by explicit data staging in a conventional PIM architecture.
Methodology:
- Setup: Use a real PIM system (e.g., UPMEM) and select a benchmark from the PrIM suite (e.g., Vector Addition, Selection) [49] [92].
- Execution: Run the benchmark with a small dataset (e.g., 1 GB) and a large dataset (e.g., 128 GB). Use profiling tools to measure:
T_host_to_pim: Time to transfer input data from host to PIM memory.T_exec: Time for PIM cores to execute the computation.T_pim_to_host: Time to transfer results back to host memory.T_total: Total end-to-end execution time.
- Analysis: Calculate the percentage of time spent in data transfer:
Transfer Overhead % = [(T_host_to_pim + T_pim_to_host) / T_total] * 100. The large dataset will reveal a significantly higher overhead, often between 60-90% [49].
Protocol 2: Benchmarking Unified vs. Disjoint Memory Models
Objective: To compare the end-to-end performance of a biomedical workload (e.g., genome sequence alignment) on PIM versus CXL-PIM.
Methodology:
- Workload Selection: Choose a memory-bound biomedical kernel, such as a sequence similarity scan from the PrIM bioinformatics benchmarks [91].
- Platforms:
- Platform A (PIM): A system with conventional PIM DIMMs.
- Platform B (CXL-PIM): A system using a CXL-PIM simulator or hardware (e.g., CENT framework) [53].
- Execution: Scale the input dataset from small (a few GB) to very large (over 100 GB). Measure the total execution time on both platforms.
- Expected Result: For small datasets, conventional PIM may be faster due to lower access latency to its local memory. For large datasets, CXL-PIM will outperform PIM as the unified memory model avoids the crushing overhead of explicit staging [49].
Architectural Diagrams and Workflows
Diagram 1: PIM vs. CXL-PIM Dataflow
Diagram 2: Experimental Benchmarking Workflow
Technical Support Center: Troubleshooting Guides and FAQs
This technical support center provides targeted solutions for researchers and scientists implementing Federated Learning (FL) in privacy-sensitive domains, with a specific focus on optimizing host-device communication—a critical aspect of reducing data transfer overhead.
Frequently Asked Questions (FAQs)
Q1: Our global FL model is converging very slowly. What are the primary strategies to reduce communication rounds?
Slow convergence is often a symptom of communication bottlenecks and data heterogeneity. The core strategy is to increase local computation to decrease global communication [93]. Key approaches include:
- Increase Local Epochs: Train the local model for more iterations on each node before sending updates [93]. This improves the quality of each update, reducing the total rounds needed.
- Optimize Client Selection: Instead of random selection, use algorithms that prioritize clients with higher-quality data or better connectivity [93] [94]. This prevents slow nodes from delaying aggregation and improves the informational value of each round.
- Implement Adaptive Learning Rates: Use optimization algorithms that help the global model converge faster, thus requiring fewer communication rounds [93] [94].
Q2: How can we protect our FL system from malicious clients performing data poisoning attacks?
Byzantine-robust aggregation schemes are essential to defend against data poisoning [93]. Your options include:
- Distance-based Schemes: Identify and reject parameter updates that deviate significantly from the norm, for example, by using the Krum algorithm [93].
- Statistical Schemes: Use robust statistical measures for aggregation, such as calculating the median or trimmed mean of the updates, which diminishes the impact of extreme, potentially malicious values [93].
- Performance-based Schemes: Evaluate updates based on their performance on a held-out validation dataset before incorporating them into the global model [93].
Q3: We are facing high node dropout rates, especially with mobile or IoT devices. How can we make our FL process more resilient?
Node dropout is a common challenge in dynamic environments. Implement asynchronous communication and fault-tolerant protocols [94]:
- Asynchronous Aggregation: Allow the server to aggregate updates as they arrive, rather than waiting for all nodes in a round. This prevents slow or dropped nodes from halting the entire process [94].
- Checkpointing: Regularly save the state of the global model. When a node reconnects, it can resume training from the last checkpoint instead of starting over [94].
- Set Realistic Timeouts: Define reasonable timeouts for client responses and have a minimum quorum for proceeding with aggregation [94].
Troubleshooting Common Federated Learning Experiments
Issue: Significant Accuracy Drop After Implementing Differential Privacy You observe that adding Differential Privacy (DP) noise to preserve privacy has degraded your model's performance unacceptably.
- Root Cause: The privacy-accuracy trade-off is not optimally tuned. The privacy budget (epsilon) is likely too restrictive [95].
- Investigation & Resolution:
- Quantify the Trade-off: Systematically test different privacy budgets (ε) to find the optimal point where privacy is sufficient and accuracy remains acceptable. As shown in the table below, a slightly higher epsilon can often restore performance [95].
- Use Local DP: Consider adding noise locally on client devices before sending updates, which can provide stronger privacy guarantees than adding noise only at the server (Central DP) [93].
- Validate on Your Dataset: The optimal ε is dataset-dependent. The following table summarizes results from a breast cancer diagnosis study, illustrating this trade-off.
Table 1: Performance-Privacy Trade-off in a Federated Learning Experiment for Breast Cancer Diagnosis [95]
| Model Type | Accuracy | Privacy Budget (ε) | Key Characteristic |
|---|---|---|---|
| Centralized Model | 96.0% | Not Applicable | Raw data is centralized, high privacy risk. |
| FL with DP | 96.1% | 1.9 | Optimal balance of privacy and accuracy. |
| FL with Stronger DP | 92.5% | 0.5 | High privacy, but significant accuracy loss. |
Issue: Global Model Performance is Biased Towards Clients with Specific Data Distributions The global model performs well on some data types but poorly on others, a classic sign of performance bias.
- Root Cause: Data heterogeneity (non-IID data) across clients. Simple averaging during aggregation gives equal weight to all updates, unfairly favoring majority data patterns [93] [96].
- Investigation & Resolution:
- Data Quality Validation: Implement a data quality gate that profiles local data for issues like extreme class imbalance or anomalous distributions before allowing a node to participate [94].
- Use Weighted Aggregation: Modify the aggregation algorithm (e.g., Federated Averaging) to weight each client's update based on its sample size or data quality [93]. This prevents small or low-quality datasets from having a disproportionate influence.
- Test for Fairness: Evaluate the final global model on held-out test datasets that represent all participating data distributions to identify specific biases.
Experimental Protocols for Validating FL Performance
Protocol 1: Measuring the Impact of Communication Optimization Strategies
This protocol evaluates techniques to reduce host-device data transfer overhead.
- Objective: Quantify the reduction in communication cost and time-to-accuracy achieved by model compression and client selection algorithms.
- Methodology:
- Baseline: Run FL with full model updates and random client selection.
- Intervention: In subsequent runs, implement one or more optimization techniques from the table below.
- Metrics: Track (a) total data transferred (MB), (b) number of communication rounds to reach target accuracy, and (c) final model accuracy.
- Key Materials:
- Research Reagent Solutions: A simulated or real-world FL testbed (e.g., using TensorFlow Federated or PySyft).
- Dataset: A standardized benchmark dataset (e.g., CIFAR-10 for vision, Shakespeare for NLP).
- Evaluation Scripts: Custom scripts to monitor network traffic and model performance.
Table 2: Key Techniques for Reducing FL Communication Overhead [93]
| Technique | Methodology | Primary Function |
|---|---|---|
| Model Compression | Reducing the precision (quantization) or number (pruning) of model parameters sent during updates. | Drastically reduces the size of each individual update. |
| Client Selection | Using algorithms to select a subset of clients with high-quality data or fast connections in each round. | Reduces the number of participants per round, lowering total traffic. |
| Increased Local Epochs | Performing more local training steps before communicating with the server. | Reduces the total number of communication rounds required for convergence. |
The following workflow diagram illustrates the optimized FL process integrating these techniques.
Protocol 2: Validating a Privacy-Preserving FL System for AI-Enabled Drug Screening
This protocol outlines how to integrate and test Differential Privacy (DP) within an FL framework for a sensitive task like drug screening.
- Objective: Develop a predictive model for drug-target interactions that protects patient/privacy data, achieving accuracy within 5% of a non-private centralized baseline.
- Methodology:
- Setup: Partner with multiple pharmaceutical research units, each holding proprietary molecular data. A central coordinator is established.
- Local Training: Each unit trains a model on its local dataset. Before sending updates, they add calibrated random noise (Local DP) [93] [95].
- Aggregation: The coordinator collects the noisy updates and uses secure aggregation (e.g., with SMPC) to compute a new global model [93].
- Validation: The final global model is evaluated on a standardized, held-out validation set of known drug-target interactions.
- Key Materials:
- Research Reagent Solutions:
- DP Library: A software library like TensorFlow Privacy or Opacus to implement the noise-adding mechanism.
- Drug-Target Database: A curated database such as ChEMBL or BindingDB for validation.
- FL Framework: A platform such as NVIDIA FLARE or IBM FL to orchestrate the process.
- Research Reagent Solutions:
Table 3: Essential Research Reagents for a Privacy-Preserving FL Drug Screening Experiment [97] [95]
| Item | Function | Example Tools/Techniques |
|---|---|---|
| Federated Learning Framework | Software platform to orchestrate the distributed training, aggregation, and communication. | NVIDIA FLARE, IBM Federated Learning, TensorFlow Federated. |
| Differential Privacy Engine | Adds mathematically-proven noise to model updates to guarantee privacy. | TensorFlow Privacy, PyTorch Opacus. |
| Molecular Datasets | Decentralized, proprietary data from partners used for local training; a public benchmark for final validation. | Partner-specific data; public benchmarks like ChEMBL. |
| Secure Aggregation Protocol | Combines model updates in a way that the server cannot inspect individual contributions. | Secure Multi-Party Computation (SMPC) [93]. |
The logical relationship between privacy techniques and the FL workflow is shown below.
FAQs on Data Transfer Overhead and Computational Cost
Q1: What are the primary strategies for reducing host-to-device data transfer latency in computational workloads? A1: The primary strategies involve optimizing both data transfer methods and computational patterns.
- Pinned Memory: Using pinned (page-locked) host memory is fundamental. It can significantly increase transfer bandwidth compared to pageable memory. For instance, benchmarks show pinned memory can achieve transfer speeds of 12 GB/s versus 5 GB/s for pageable memory [15].
- Asynchronous Transfers and Streams: Leveraging CUDA streams or SYCL queues allows for overlapping data transfers with device computation. This helps conceal the data transfer overhead by executing kernels while data is being moved in the background [15] [1].
- Batching and Chunking: Instead of processing a single large dataset, break the data into smaller chunks and process them through a sequence of shorter-running kernels. This "streaming" design makes processed data available on the host much earlier, drastically reducing latency. The choice of chunk size is a trade-off between latency and throughput [1].
- Hardware Utilization: Ensure your hardware is fully leveraged. This includes using a PCIe slot with the maximum available lanes (e.g., x16) and, in multi-socket systems, ensuring GPUs are talking to the "near" CPU to optimize memory affinity [15].
Q2: How can I quantify the cost-efficiency of my cloud or on-premise computing environment?
A2: For cloud environments, a standardized metric like the Cost Efficiency formula can be used [98]:
Cost efficiency = [1 - (Potential Savings / Total Optimizable Spend)] × 100%
This metric, used by AWS, combines potential savings from rightsizing, idle resource cleanup, and commitment discounts against your total spend on optimizable services. A higher percentage indicates greater efficiency [98].
For a broader Total Cost of Ownership (TCO) analysis comparing cloud and on-premise setups, you must account for all cost components [99]:
- Cloud TCO: Includes pay-as-you-go subscription fees, data egress costs, and staffing for cloud management (FinOps, DevOps) [100] [99].
- On-Premise TCO: Includes Capital Expenditures (CapEx) for hardware (GPUs, servers) and Operational Expenditures (OpEx) for electricity, cooling, maintenance, and IT staff [101] [99].
Q3: At what usage level does an on-premise GPU cluster for large language models (LLMs) become more cost-effective than using commercial cloud APIs? A3: The breakeven point is highly dependent on the model size and your usage volume. Research indicates that on-premise deployment can become economically viable for organizations with extreme high-volume processing requirements (≥50 million tokens per month) [101].
- Small Models: Breakeven can be within a few months [101].
- Medium Models: Breakeven may occur around 2 years [101].
- Large Models: The payback period can extend to 5 years, making it viable primarily for organizations with massive, sustained workloads or strict data governance requirements [101].
Q4: What are common causes of unexpected high costs in cloud environments for data-intensive research? A4: Key factors include:
- Unoptimized Data Transfer: High costs can stem from data egress fees and inefficient transfer methods that increase compute time [102] [103].
- Idle and Over-provisioned Resources: Leaving resources running when not in use or provisioning overly large instances for the workload is a major source of waste [102] [104] [98].
- Complex Pricing Models: The intricate and dynamic nature of cloud pricing can lead to unexpected bills if not carefully managed [100] [103].
- Lack of Visibility and Governance: Without proper monitoring, tagging, and governance policies, it is difficult to track spending back to specific projects or teams, leading to cost overruns [102].
Q5: What is a "FinOps" culture and why is it important for research teams? A5: FinOps is a cultural practice that brings financial accountability to the variable spend model of the cloud. It involves collaboration between finance, IT, and technical teams (like researchers) to make data-driven spending decisions [103]. For research teams, this means:
- Treating cost as a first-class metric alongside performance and scientific outcomes.
- Empowering engineers and researchers to see the cost impact of their code and experimental designs in near real-time.
- Fostering a culture of cost awareness and continuous optimization, ensuring that cloud resources are used efficiently without hampering innovation velocity [102] [103].
Quantitative Data for Cost-Benefit Analysis
The tables below summarize key pricing and cost data to inform your analysis.
| Provider | On-Demand Model | Commitment Model (1-3 Year) | Spot/Preemptible Model | Sustained Use Discounts |
|---|---|---|---|---|
| AWS | Pay per second [100] | Savings Plans (up to 72% off) [100] | Spot Instances (up to 90% off) [100] | - |
| Microsoft Azure | Pay per second/minute [100] | Savings Plans (up to 72% off) [100] | Spot VMs [100] | - |
| Google Cloud (GCP) | Pay per second [100] | Committed Use Discounts (up to 57% off) [100] | Preemptible VMs (up to 80% off) [100] | Automatic discounts for sustained usage [100] |
| Oracle Cloud (OCI) | Pay per second/hour [100] | Reserved Instances (up to 65% off) [100] | Preemptible Instances (up to 70% off) [100] | - |
Commercial LLM API Pricing (Input/Output per 1M Tokens) [101]
| Model Provider | Model Name | Input Cost (USD) | Output Cost (USD) |
|---|---|---|---|
| OpenAI | GPT-5 | $1.25 | $10.00 |
| Anthropic | Claude-4 Opus | $15.00 | $75.00 |
| Anthropic | Claude-4 Sonnet | $3.00 | $15.00 |
| xAI | Grok-4 | $3.00 | $15.00 |
| Gemini 2.5 Pro | $1.25 | $10.00 |
Approximate On-Premise GPU Break-Even Timeline [101]
| Model Size Category | Estimated Breakeven Period | Typical Viable Usage |
|---|---|---|
| Small Models | A few months | High-volume processing |
| Medium Models | ~2 years | ≥50M tokens/month |
| Large Models | ~5 years | ≥50M tokens/month |
The Scientist's Toolkit: Research Reagent Solutions
| Tool / Technique | Function / Explanation |
|---|---|
| Pinned (Page-Locked) Memory | Allocates non-swappable host memory to enable maximum data transfer bandwidth between host and device [15]. |
| CUDA Streams / SYCL Queues | Enables concurrency by allowing asynchronous data transfers and kernel execution to overlap, hiding transfer latency [15] [1]. |
| Host-Device Streaming Design | A software design pattern that processes data in small, sequential chunks to minimize end-to-end latency compared to bulk offload processing [1]. |
| Cost Efficiency Metric | A standardized formula ([1 - (Potential Savings / Total Optimizable Spend)] × 100%) to quantify the cost-effectiveness of cloud resources [98]. |
| FPGA Producer-Consumer Kernels | For multi-kernel FPGA designs, this setup uses dedicated kernels to stream data to/from the host, minimizing launch overhead and latency regardless of the number of processing kernels [1]. |
Experimental Protocols & Workflows
Protocol 1: Methodology for Benchmarking Host-to-Device Data Transfer Performance
- Hardware Setup Verification:
- Bandwidth Measurement:
- Latency vs. Throughput Optimization (Streaming):
- Offload Processing (Baseline): Transfer the entire dataset to the device, run a single large kernel, and transfer results back. Measure total execution time and time to first result [1].
- Streaming Processing: Break the dataset into
Nchunks. For each chunk, use a dedicated stream to asynchronously copy the chunk to the device, run a processing kernel, and copy the result back. Measure the time to first result and total execution time [1]. - Analysis: Compare the time to first result between the two methods. Systematically vary the chunk size to analyze the trade-off between latency (smaller chunks) and overall throughput (larger chunks) [1].
Protocol 2: Framework for Cloud vs. On-Premise TCO Analysis for LLM Deployment
- Define Workload Parameters:
- Determine the model size (parameters) and the expected monthly inference volume (tokens).
- Estimate the required GPU infrastructure (e.g., number of H100 or A100 GPUs) for target throughput [101].
- Calculate Cloud Costs:
- Calculate On-Premise Costs:
- CapEx: Sum the upfront costs of servers, GPUs, networking, and initial setup. Amortize this cost over the expected hardware lifespan (e.g., 3-5 years) to get a monthly value [101] [99].
- OpEx: Estimate monthly costs for electricity (including cooling), physical space, hardware maintenance, and dedicated IT staff [101] [99].
- Perform Break-Even Analysis:
- Compare the total monthly cloud cost with the total monthly on-premise cost (amortized CapEx + OpEx).
- The break-even point is when the cumulative cost of the on-premise solution becomes lower than the cumulative cost of the cloud solution. Plot these cumulative costs over time to visualize the crossover point [101] [99].
Protocol 3: Implementing a Cloud Cost Optimization Feedback Loop
- Establish Visibility:
- Identify Optimization Opportunities:
- Use recommendation engines (e.g., AWS Cost Optimization Hub, Azure Advisor) to get automated recommendations for rightsizing, deleting idle resources, and purchasing commitment plans [98].
- Conduct regular audits to find and eliminate unused storage volumes (e.g., EBS, blob storage) and over-provisioned compute instances [104].
- Take Action and Monitor:
Workflow and System Diagrams
Latency vs Throughput Trade-off
Cloud vs On-Premise Cost Analysis
Conclusion
Reducing host-device data transfer overhead is not merely a technical exercise but a strategic imperative for accelerating biomedical research and drug development. The synthesis of strategies covered—from foundational architectural shifts like CXL-PIM and USM to practical applications of data reduction and protocol optimization—provides a comprehensive toolkit for overcoming a critical computational bottleneck. Looking forward, the integration of Edge AI for intelligent, context-aware data filtering and the maturation of cross-layer optimization frameworks promise even greater efficiencies. By proactively adopting these approaches, research teams can unlock faster iterations in virtual screening, manage the exploding data volumes from high-resolution imaging and omics technologies, and ultimately shorten the timeline for delivering novel therapeutics to patients. The future of computational biology hinges on the seamless flow of data, making its efficient management a cornerstone of scientific innovation.
References
- 1. Simple Host-Device Streaming [https://www.intel.com/content/www/us/en/docs/oneapi-fpga-add-on/developer-guide/2025-0/simple-host-device-streaming.html]
- 2. A tasks reordering model to reduce transfers overhead on ... [https://www.sciencedirect.com/science/article/abs/pii/S0743731517302046]
- 3. Why is the transfer throughput low when transferring small ... [https://forums.developer.nvidia.com/t/why-is-the-transfer-throughput-low-when-transferring-small-size-data-from-host-to-device-or-device-to-host/153962]
- 4. Page-Locked Host Memory for Data Transfer - Lei Mao [https://leimao.github.io/blog/Page-Locked-Host-Memory-Data-Transfer/]
- 5. Pipelining data processing and host-to-device data transfer [https://www.telesens.co/2019/02/16/efficient-data-transfer-from-paged-memory-to-gpu-using-multi-threading/]
- 6. CUDA C++ Best Practices Guide [https://docs.nvidia.com/cuda/cuda-c-best-practices-guide/]
- 7. Speeding Up Data Decompression with nvCOMP and the ... [https://developer.nvidia.com/blog/speeding-up-data-decompression-with-nvcomp-and-the-nvidia-blackwell-decompression-engine/]
- 8. oneAPI GPU Optimization Guide [https://www.intel.com/content/www/us/en/docs/oneapi/optimization-guide-gpu/2025-0/introduction-001.html]
- 9. Optimizing Data Transfer Performance and Energy ... [https://arxiv.org/html/2503.13662v1]
- 10. Top GPU Hosts for AI Machine Learning in 2025 [https://www.gmicloud.ai/blog/gpu-hosting-for-ai-projects-top-gpu-hosts-for-ai-machine-learning-in-2025]
- 11. The AI Edge Computing Cost: Local Processing vs Cloud ... [https://www.getmonetizely.com/articles/the-ai-edge-computing-cost-local-processing-vs-cloud-pricing]
- 12. 50 Statistics Every Technology Leader Should Know in 2025 [https://www.integrate.io/blog/data-transformation-challenge-statistics/]
- 13. Host overhead is killing your inference efficiency [https://modal.com/blog/host-overhead-inference-efficiency]
- 14. How to Move Data to the GPU - Cornell Virtual Workshop [https://cvw.cac.cornell.edu/gpu-migration-portability/gpu-migration-paths/gpu-migration-move-data]
- 15. Improving data transfer performance from host to device [https://forums.developer.nvidia.com/t/improving-data-transfer-performance-from-host-to-device/36539]
- 16. What is a Staging Environment? | Definition from TechTarget [https://www.techtarget.com/searchsoftwarequality/definition/staging-environment]
- 17. What Is a Staging Environment? [https://launchdarkly.com/blog/what-is-a-staging-environment/]
- 18. How Daiichi Sankyo modernized drug discovery using ... [https://aws.amazon.com/blogs/hpc/how-daiichi-sankyo-modernized-drug-discovery-using-aws-parallel-computing-service/]
- 19. Transport Layer Security (TLS) and application performance [https://gatling.io/blog/transport-layer-security-tls-and-application-performance]
- 20. - netsekure rng TLS overhead [http://netsekure.org/2010/03/tls-overhead/]
- 21. draft-mattsson-uta- tls - overhead -01 [https://datatracker.ietf.org/doc/html/draft-mattsson-uta-tls-overhead-01]
- 22. TLS Handshake [https://entro.security/glossary/tls-handshake/]
- 23. Addressing Data Management Challenges in Genomics ... [https://astrixinc.com/blog/lab-informatics/top-data-management-challenges-in-genomics-research/]
- 24. HPDR: High-Performance Portable Scientific Data ... [https://arxiv.org/html/2503.06322]
- 25. 2025 and Beyond: The Future of Genomic Data Analysis ... [https://blog.crownbio.com/2025-and-beyond-the-future-of-genomic-data-analysis-and-innovations-in-genomics-services]
- 26. The Cloud and Imaging in Healthcare: 2025 Outlook [https://dcmsys.com/project/the-cloud-and-imaging-in-healthcare-2024-outlook/]
- 27. Optimizing Data Storage & Transfer for DICOM Images [https://www.qsstechnosoft.com/blog/dicom-107/optimising-data-storage-and-transfer-capabilities-with-a-dedicated-file-sharing-solution-for-dicom-images-536]
- 28. Standardizing digital biobanks: integrating imaging, genomic ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10845786/]
- 29. The future of multimodal artificial intelligence models for ... [https://dirjournal.org/articles/the-future-of-multimodal-artificial-intelligence-models-for-integrating-imaging-and-clinical-metadata-a-narrative-review/dir.2024.242631]
- 30. High-Performance Host-Device Scheduling and Data-Transfer ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7592707/]
- 31. Analyzing Data Reduction Techniques: An Experimental ... [https://www.mdpi.com/2076-3417/14/8/3436]
- 32. Comparative analysis of model compression techniques for ... [https://www.nature.com/articles/s41598-025-07821-w]
- 33. Optimizing Deployment for Faster Drug Development From ... [https://www.elucidata.io/blog/optimizing-deployment-for-faster-drug-development-from-r-d-to-market]
- 34. Cloud based collaborative data compression technology ... [https://www.sciencedirect.com/science/article/pii/S1110866525000891]
- 35. Systematic data capture reduces the need for source ... [https://www.nature.com/articles/s43856-025-01126-9]
- 36. Edge Computing for Data Science (2025 Guide) [https://medium.com/top-python-libraries/edge-computing-for-data-scientists-a-practical-guide-for-2025-26-a8157db643c4]
- 37. The Complete Guide to Edge Computing Architecture [https://www.mirantis.com/blog/the-complete-guide-to-edge-computing-architecture/]
- 38. Unlocking the Next Frontier in AI-Driven Drug Discovery [https://www.pharmexec.com/view/unlocking-the-next-frontier-in-ai-driven-drug-discovery]
- 39. Top Edge Computing Platforms for 2025 | OTAVA [https://www.otava.com/blog/top-edge-computing-platforms-for-2025/]
- 40. Optimizing IoT Protocols for Edge Microservices [https://blog.dreamfactory.com/optimizing-iot-protocols-for-edge-microservices]
- 41. A Guide to MQTT [https://www.influxdata.com/mqtt/]
- 42. Understanding API gRPC for Efficient Communication [https://www.ai-futureschool.com/en/computing/understanding-grpc-api-for-efficient-communication.php]
- 43. Comparison of TCP/UDP/HTTP/MQTT Protocols [https://www.cdebyte.com/news/733]
- 44. MQTT Protocol - What is it and how does it work? [https://getstream.io/glossary/mqtt-protocol/]
- 45. How gRPC Keepalive Solved Our Zombie Connections ... [https://medium.com/freshworks-engineering-blog/how-grpc-keepalive-solved-our-zombie-connections-mystery-f4f626c8a9f2]
- 46. MQTT Operational issues due to broker misconfiguration. [https://drdroid.io/stack-diagnosis/mqtt-operational-issues-due-to-broker-misconfiguration]
- 47. Troubleshooting gRPC Errors: A Developer's Guide for ... [https://hoop.dev/blog/troubleshooting-grpc-errors-a-developers-guide-for-efficient-debugging/]
- 48. MQTT vs Kafka, HTTP, HTTPS, and CoAP UDP [https://medium.com/data-motion/mqtt-vs-kafka-http-https-and-coap-udp-optimizing-iot-device-communication-aad3120c98b2]
- 49. PIM or CXL-PIM? Understanding Architectural Trade-offs ... [https://arxiv.org/html/2511.14400v1]
- 50. What is Compute Express Link (CXL)? [https://www.trentonsystems.com/en-us/resource-hub/blog/what-is-compute-express-link-cxl]
- 51. Unified Shared Memory Allocations [https://www.intel.com/content/www/us/en/docs/oneapi/optimization-guide-gpu/2024-0/unified-shared-memory-allocations.html]
- 52. Optimizing CUDA Memory Transfers with NVIDIA Nsight ... [https://developer.nvidia.com/blog/optimizing-cuda-memory-transfers-with-nsight-systems/]
- 53. PIM Is All You Need: A CXL-Enabled GPU-Free System for ... [https://arxiv.org/html/2502.07578v1]
- 54. How to Overlap Data Transfers in CUDA C/C++ [https://developer.nvidia.com/blog/how-overlap-data-transfers-cuda-cc/]
- 55. Asynchronous and Overlapping Data Transfers Between ... [https://www.intel.com/content/www/us/en/docs/oneapi/optimization-guide-gpu/2025-0/asynchronous-and-overlapping-data-transfers.html]
- 56. 9.2 Communication Patterns and Overlapping [https://fiveable.me/parallel-and-distributed-computing/unit-9/communication-patterns-overlapping/study-guide/hHtAIflquxEJzH9d]
- 57. Compute-Communication Overlap in Neuron [https://awsdocs-neuron.readthedocs-hosted.com/en/latest/neuron-runtime/explore/compute-comm-overlap.html]
- 58. How to fix poor GPU performance in AI training [https://www.crusoe.ai/resources/blog/the-ai-engineers-checklist-for-optimal-gpu-performance]
- 59. Optimizing Drug Discovery with CUDA Graphs, Coroutines ... [https://developer.nvidia.com/blog/optimizing-drug-discovery-with-cuda-graphs-coroutines-and-gpu-workflows/]
- 60. CPU Utilization 2025 [https://www.rsinc.com/cpu-utilization.php]
- 61. Minimizing transformer inference overhead using ... [https://link.springer.com/article/10.1631/FITEE.2400453]
- 62. Software Performance Optimization: The Expert Guide for ... [https://www.sedai.io/blog/software-performance-optimization-expert-guide]
- 63. Smarter Strategies for Scaling Performance on a Budget [https://worldwidesupply.net/blog/network-optimization-in-2025-smarter-strategies-for-scaling-performance-on-a-budget/]
- 64. The solution of issue of slow transmission of large volumes ... [https://www.raysync.io/news/the-solution-of-issue-of-slow-transmission-of-large-volumes-of-small-files-2023/]
- 65. Small files' problem in Hadoop: A systematic literature review [https://www.sciencedirect.com/science/article/pii/S1319157821002585]
- 66. Five Predictions That Will Drive R&D Effectiveness in 2025 [https://www.appliedclinicaltrialsonline.com/view/five-predictions-rd-effectiveness-2025]
- 67. 5 Challenges Slowing Drug Development and How Tech ... [https://www.linkedin.com/pulse/5-challenges-slowing-drug-development-how-tech-enabled-66gzc]
- 68. Accelerated File Transfer: Complete Guide to Fast, Secure ... [https://www.hivenet.com/post/accelerated-file-transfer-complete-guide-to-fast-secure-data-movement]
- 69. Batching small files to improve data transfer performance ... [https://docs.aws.amazon.com/snowball/latest/developer-guide/batching-small-files.html]
- 70. HIPAA Encryption Protocols: 2025 Updates [https://censinet.com/perspectives/hipaa-encryption-protocols-2025-updates]
- 71. Healthcare Data Security Challenges: Patient Data Risks in ... [https://www.firewalls.com/blog/healthcare-data-security-challenges/?srsltid=AfmBOorysgiDksnexDrHJyxFvTk_f0fG97wXiW-yV57gtV4fH3O1h_Em]
- 72. The Top 7 Medical Device Vulnerabilities of 2025 [https://runsafesecurity.com/blog/top-medical-device-vulnerabilities/]
- 73. 2025 HIPAA Updates: Key Changes Every Organization ... [https://www.metricstream.com/blog/hipaa-updates-2025-key-changes.html]
- 74. AIBIO 2025 - AI in Biomedical Data Workshop - GitHub Pages [https://wsaibio.github.io/ecai2025/]
- 75. A-WHO: Stagnation-Based Adaptive Metaheuristic for ... [https://www.mdpi.com/2079-9292/14/21/4337]
- 76. Anomaly detection in medical via multimodal foundation models [https://pmc.ncbi.nlm.nih.gov/articles/PMC12378924/]
- 77. Thread vs Stream what is the difference? [https://forums.developer.nvidia.com/t/thread-vs-stream-what-is-the-difference/20064]
- 78. CUDA streams [https://haroldbenoit.com/notes/ml/engineering/gpu-programming/cuda-streams]
- 79. Supercharging Data Transfers in CUDA: The Power of ... [https://www.linkedin.com/pulse/supercharging-data-transfers-cuda-power-page-locked-pinned-mohapatra-bejec]
- 80. Request for Suggestions on Optimizing CPU-GPU Data ... [https://forums.developer.nvidia.com/t/request-for-suggestions-on-optimizing-cpu-gpu-data-transfer/319237]
- 81. Multi-Thread Single-Stream VS Single-Thread Multi ... - Lei Mao [https://leimao.github.io/blog/Multi-Thread-Single-Stream-VS-Single-Thread-Multi-Stream-CUDA/]
- 82. Multiple threads calling CUDA API in parallel [https://forums.developer.nvidia.com/t/multiple-threads-calling-cuda-api-in-parallel/301301]
- 83. Can I use streaming to overlap kernels and data transfers ... [https://forums.developer.nvidia.com/t/can-i-use-streaming-to-overlap-kernels-and-data-transfers-in-this-scenario/298621]
- 84. Performance Measurement Baseline: Definition | Example [https://project-management.info/performance-measurement-baseline/]
- 85. Throughput vs Latency Graph [https://www.browserstack.com/guide/throughput-vs-latency]
- 86. Latency vs. Throughput in Distributed Rate Limiting [https://blog.dreamfactory.com/latency-vs.-throughput-in-distributed-rate-limiting]
- 87. What's the Difference Between Throughput and Latency? [https://aws.amazon.com/compare/the-difference-between-throughput-and-latency/]
- 88. What is Data Reduction and Why it Matters? [https://www.fanruan.com/en/glossary/big-data/data-reduction]
- 89. SEElab | research [http://varys.ucsd.edu/research/]
- 90. Unified Shared Memory: Friend or Fue? - Juan Fumero [https://jjfumero.github.io/posts/2023/10/unified-shared-memory]
- 91. An Experimental Analysis of a Real Processing-in-Memory ... [https://arxiv.org/abs/2105.03814]
- 92. GitHub - CMU-SAFARI/prim-benchmarks: PrIM (Processing ... [https://github.com/CMU-SAFARI/prim-benchmarks]
- 93. Federated Learning: Risks and Challenges - Edge AI and Vision Alliance [https://www.edge-ai-vision.com/2025/01/federated-learning-risks-and-challenges/]
- 94. Federated Learning in 2025: What You Need to Know [https://dev.to/lofcz/federated-learning-in-2025-what-you-need-to-know-3k2j]
- 95. Federated learning with differential privacy for breast cancer diagnosis enabling secure data sharing and model integrity | Scientific Reports [https://www.nature.com/articles/s41598-025-95858-2]
- 96. Federated Learning for IoT: A Survey of Techniques, Challenges, and Applications [https://www.mdpi.com/2224-2708/14/1/9]
- 97. AI in Pharma and Biotech: Market Trends 2025 and Beyond [https://www.coherentsolutions.com/insights/artificial-intelligence-in-pharmaceuticals-and-biotechnology-current-trends-and-innovations]
- 98. The Challenge of Measuring Cloud Cost Efficiency [https://aws.amazon.com/blogs/aws-cloud-financial-management/measuring-cloud-cost-efficiency-with-the-new-cost-efficiency-metric-by-aws/]
- 99. Cloud Exit Economics: Real-World ROI And Financial Models [https://cloudtweaks.com/2025/09/cloud-exit-economics-real-world-roi-financial-models/]
- 100. 2025 Cloud Pricing Comparison: An In-Depth Guide [https://www.cloudzero.com/blog/cloud-pricing-comparison/]
- 101. A Cost-Benefit Analysis of On-Premise Large Language ... [https://arxiv.org/html/2509.18101v3]
- 102. Mastering Cloud Cost Optimization? 15+ Best Practices for ... [https://www.cloudzero.com/blog/cloud-cost-optimization/]
- 103. 2025 Guide to Cloud Cost Optimization for Modern ... [https://www.uscloud.com/blog/cloud-cost-optimization-2025-guide/]
- 104. 11 IT Cost Optimization Strategies for Scalable Savings in ... [https://www.digitalocean.com/resources/articles/it-cost-optimization-strategies]