Mathematical Models of Predator-Prey Interactions: From Ecological Foundations to Biomedical Applications
This comprehensive review explores mathematical models of predator-prey interactions, tracing their evolution from classical Lotka-Volterra systems to contemporary computational frameworks.
Mathematical Models of Predator-Prey Interactions: From Ecological Foundations to Biomedical Applications
Abstract
This comprehensive review explores mathematical models of predator-prey interactions, tracing their evolution from classical Lotka-Volterra systems to contemporary computational frameworks. We examine foundational theories, diverse methodological approaches including ODE, discrete, and stochastic models, and address troubleshooting through stability and bifurcation analysis. The article highlights validation techniques and comparative frameworks while emphasizing growing applications in biomedical research, particularly in tumor-immune dynamics and drug market modeling. This synthesis provides researchers, scientists, and drug development professionals with both theoretical understanding and practical insights for applying ecological modeling principles to complex biological systems.
Theoretical Foundations: From Lotka-Volterra to Contemporary Frameworks
The Lotka-Volterra equations represent a foundational mathematical model in theoretical ecology, providing a framework for understanding the dynamics of interacting biological species. Independently developed by Alfred J. Lotka and Vito Volterra in the 1920s, this system of nonlinear differential equations describes the oscillatory behavior observed in predator-prey interactions [1] [2]. The model has since become a cornerstone in mathematical biology, extending beyond its original ecological context to applications in economics, epidemiology, and social sciences [1] [3]. This article examines the historical development, core mathematical principles, and methodological protocols for applying the Lotka-Volterra model within predator-prey research, providing researchers with practical tools for implementing and analyzing this classical system.
Historical Origins and Development
Independent Formulation by Alfred J. Lotka
Alfred J. Lotka (1880-1949), an American biophysicist and mathematician, initially sought to establish a new discipline he termed "physical biology," applying physical principles and methods to biological systems [2]. With an educational background in physics and chemistry, Lotka was influenced by the energy-centered concepts of Wilhelm Ostwald during his time at the Physical-Chemical Institute in Leipzig [2]. His interdisciplinary approach led him to formulate the predator-prey equations as part of a broader investigation into energy transformations in biological systems.
Lotka first introduced the core concepts in his 1920 publication "Analytical note on certain rhythmic relations in organic systems," where he demonstrated that interactions between two species could produce sustained oscillations [2] [4]. He further developed this analysis in his seminal 1925 book Elements of Physical Biology (later reprinted as Elements of Mathematical Biology), where he presented a comprehensive treatment of predator-prey interactions within the context of host-parasite systems [1] [2]. Lotka's work represented a radical departure from traditional biological approaches of the era, emphasizing mathematical formalization of biological processes.
Independent Discovery by Vito Volterra
Vito Volterra (1860-1940), a distinguished Italian mathematician, independently developed identical equations in 1926, prompted by a biological question from his son-in-law, the marine biologist Umberto D'Ancona [1] [4] [5]. D'Ancona had been studying fish population data from the Adriatic Sea and observed a puzzling phenomenon: during World War I, when fishing efforts dramatically decreased, the percentage of predatory fish in the catches significantly increased [1] [5].
Presented with this empirical observation, Volterra formulated his mathematical model over several months, concluding that the reduction in overall fishing pressure disproportionately benefited predators, thus explaining D'Ancona's findings [4] [5]. Volterra published his results in 1926 in both Italian and English, making the international scientific community aware of this new modeling approach [2] [4]. His work sparked immediate interest among biologists and began the formal study of population dynamics using mathematical tools.
Historical Convergence and Recognition
Although Lotka's initial publication predated Volterra's work by five years, Volterra was initially unaware of Lotka's contributions [2] [6]. The near-simultaneous independent discovery led to the equations being named after both scientists, though Lotka expressed concern about being overshadowed by the more famous mathematician [2]. The historical record shows that Lotka formulated the equations first, but Volterra's work, particularly through his correspondence with biologists and subsequent lectures, played a crucial role in popularizing the model within ecological science [2] [4].
Table 1: Chronological Development of the Lotka-Volterra Model
| Year | Scientist | Contribution | Publication Context |
|---|---|---|---|
| 1910 | Alfred Lotka | Initial formulation | Theory of autocatalytic chemical reactions [1] |
| 1920 | Alfred Lotka | Extended to biological systems | "Analytical note on certain rhythmic relations in organic systems" [2] [4] |
| 1925 | Alfred Lotka | Comprehensive mathematical treatment | Elements of Physical Biology [1] [2] |
| 1926 | Vito Volterra | Independent formulation | Response to D'Ancona's fish population data [1] [4] |
Core Mathematical Principles and Equations
Fundamental Equations and Parameters
The classic Lotka-Volterra model consists of a pair of first-order, nonlinear differential equations that describe the population dynamics of two interacting species: prey (denoted by x) and predators (denoted by y) [1] [7]. The equations are:
[ \frac{dx}{dt} = \alpha x - \beta xy ] [ \frac{dy}{dt} = -\gamma y + \delta xy ]
Where the variables and parameters are defined as follows:
Table 2: Variables and Parameters in the Lotka-Volterra Equations
| Symbol | Description | Biological Interpretation |
|---|---|---|
| x | Prey population density | Number of prey per unit area (e.g., rabbits/km²) [1] |
| y | Predator population density | Number of predators per unit area (e.g., foxes/km²) [1] |
| t | Time | Temporal variable for population changes [1] |
| α | Prey growth rate | Maximum per capita growth rate of prey in absence of predators [1] [7] |
| β | Predation rate | Effect of predators on prey death rate [1] [7] |
| γ | Predator mortality rate | Per capita death rate of predators in absence of prey [1] [7] |
| δ | Predator growth efficiency | Effect of prey consumption on predator growth rate [1] [7] |
Biological Assumptions and Limitations
The Lotka-Volterra model relies on several simplifying assumptions about the biological system [1] [5]:
- The prey population has unlimited food resources
- The predator population depends entirely on the prey as its only food source
- The rate of change of populations is proportional to their size
- There are no environmental changes favoring either species
- Predators have unlimited appetite
- Populations are well-mixed with no spatial structure
- There are no age or genetic structure effects on population dynamics
These assumptions represent clear limitations when applying the model to natural systems, but they provide a necessary simplification that enables mathematical analysis and reveals fundamental dynamics of predator-prey interactions [1] [8].
Dynamic Behavior and Equilibrium Analysis
The system exhibits characteristic oscillatory behavior, with predator populations lagging behind prey populations by approximately one-quarter phase [1] [7]. The equilibrium populations occur when ( \frac{dx}{dt} = 0 ) and ( \frac{dy}{dt} = 0 ), yielding:
[ x^* = \frac{\gamma}{\delta}, \quad y^* = \frac{\alpha}{\beta} ]
This equilibrium point is a center, around which populations oscillate indefinitely with amplitudes determined by initial conditions [1] [7]. The period of oscillation depends on the model parameters and initial populations [1].
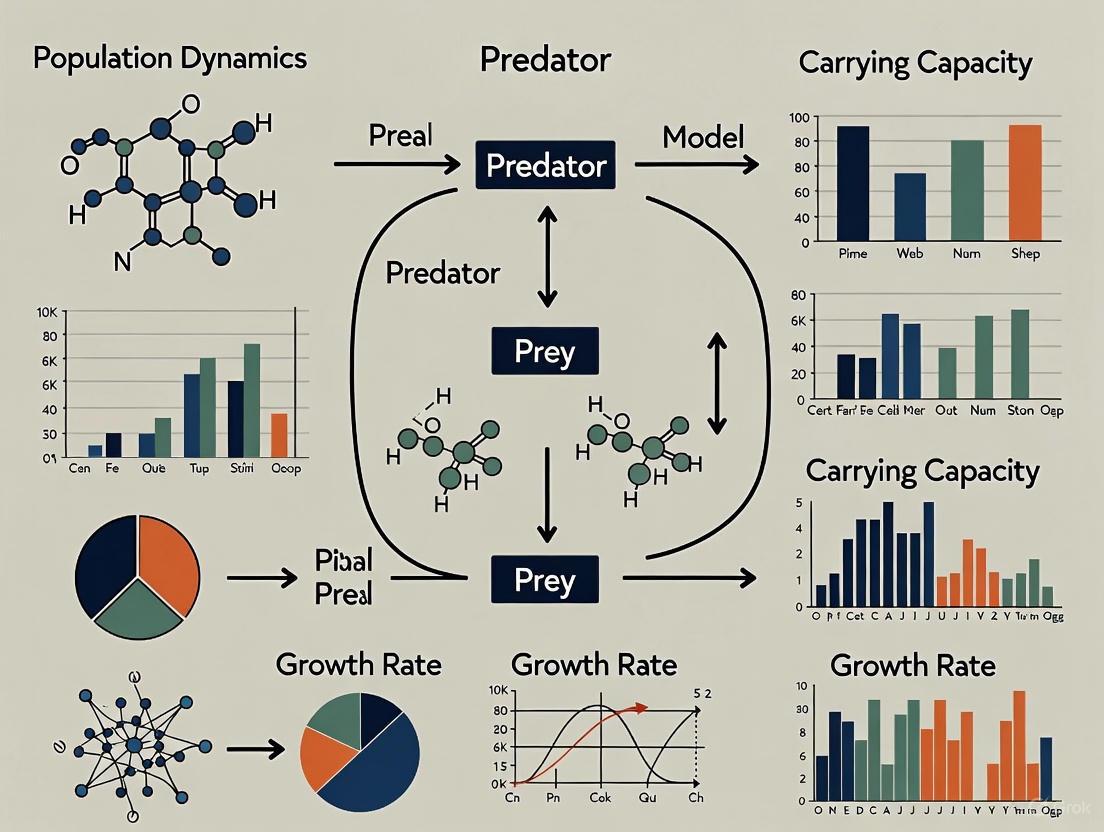
Figure 1: Causal relationships in the Lotka-Volterra predator-prey model
Experimental Protocols and Methodologies
Parameter Estimation Protocol
Accurate parameter estimation is essential for applying the Lotka-Volterra model to empirical data. The following protocol outlines a standardized approach for parameter determination:
Materials Required:
- Historical population time series data for both species
- Computational software with optimization capabilities (R, Python, MATLAB)
- Statistical packages for nonlinear regression analysis
Procedure:
- Data Preparation: Compile population data with regular time intervals. The classic Hudson Bay Company dataset of lynx and snowshoe hare pelts (1845-1935) serves as a benchmark validation dataset [5] [9].
- Initial Parameter Guessing:
- Estimate α from prey growth during periods of low predator density
- Estimate γ from predator decline during prey scarcity
- Initial β and δ can be set to small positive values (e.g., 0.01)
- Optimization Method: Implement a least-squares fitting algorithm to minimize the difference between model predictions and empirical data
- Validation: Compare model outputs with reserved validation data not used in parameter estimation
- Sensitivity Analysis: Assess parameter identifiability through local sensitivity analysis or profile likelihood approaches
Numerical Integration Protocol
For simulating the model dynamics, numerical integration is required:
Materials Required:
- Differential equation solver (ODE45 in MATLAB, odeint in Python, deSolve in R)
- Computational environment for visualization
Procedure:
- Initialization: Set initial population values x₀ and y₀
- Parameter Setting: Define values for α, β, γ, δ based on empirical estimates
- Solver Configuration:
- Use a variable-step solver for improved accuracy
- Set appropriate time span for integration
- Specify relative and absolute error tolerances (typically 1e-6)
- Execution: Run the numerical integration
- Visualization: Plot population trajectories over time and phase portraits
Stability Analysis Protocol
Analyzing system behavior around equilibrium points:
Materials Required:
- Symbolic mathematics software (Maple, Mathematica, SymPy)
- Linear algebra packages
Procedure:
- Equilibrium Calculation: Solve the system αx - βxy = 0 and -γy + δxy = 0 to find equilibrium points
- Jacobian Matrix Construction: Compute the community matrix: [ J = \begin{bmatrix} \alpha - \beta y & -\beta x \ \delta y & -\gamma + \delta x \end{bmatrix} ]
- Eigenvalue Analysis: Evaluate the Jacobian at equilibrium points and compute eigenvalues
- Stability Classification:
- Purely imaginary eigenvalues indicate neutral stability (center)
- Positive real parts indicate instability
- Negative real parts indicate stability
Research Toolkit and Reagent Solutions
Table 3: Essential Research Tools for Lotka-Volterra Modeling
| Tool/Reagent | Function/Purpose | Examples/Specifications |
|---|---|---|
| Population Data | Model validation and parameter estimation | Hudson Bay Company lynx-hare data [5] [9], Laboratory protozoan systems [8] |
| Computational Software | Numerical integration and analysis | R with deSolve package [3], Python with SciPy [3], MATLAB [8] |
| Differential Equation Solvers | Numerical solution of ODE systems | ODE45 (MATLAB) [8], odeint (Python) [8], LSODA (R) [8] |
| Optimization Algorithms | Parameter estimation | Nonlinear least squares (Levenberg-Marquardt) [9], Maximum likelihood methods [8] |
| Phase Plane Analysis Tools | Visualization of system dynamics | Custom scripts for phase portraits [7] [3], pplane (MATLAB) [7] |
| Laboratory Organisms | Experimental validation | Protozoans (Paramecium, Didinium) [8], Insect systems [8] |
Advanced Extensions and Modifications
Functional Responses
The classic Lotka-Volterra model assumes a linear functional response (Type I), where predation increases linearly with prey density [10]. More realistic functional responses include:
Type II (Holling's Disc Equation): Accounts for predator handling time [ f(R) = \frac{\lambda R}{1 + h\lambda R} ] where λ is the search rate and h is handling time [10]
Type III (Sigmoidal Response): Models situations where predators switch between prey types or require learning [ f(R) = \frac{\lambda R^\theta}{1 + h\lambda R^\theta} ] where θ > 1 determines the sigmoid shape [10]
Figure 2: Major extensions and modifications of the basic Lotka-Volterra model
Stochastic Formulations
Natural populations experience environmental stochasticity, which can be incorporated through:
- Stochastic Differential Equations: Adding Wiener processes to the deterministic model
- Individual-Based Models: Simulating discrete individuals with probabilistic rules
- Parameter Randomization: Incorporating uncertainty in parameter estimates
Multi-Species Extensions
The basic model can be extended to food webs through generalized equations:
[ \frac{dxi}{dt} = xi\left(bi + \sum{j=1}^n a{ij}xj\right) ]
where (a{ij}) represents the effect of species j on species i, and (bi) is the intrinsic growth rate [1].
Applications in Contemporary Research
Ecological Applications
The Lotka-Volterra framework continues to inform modern ecological research:
- Biological Conservation: Predicting population viability of endangered species
- Harvest Management: Informing sustainable fishing and hunting policies
- Invasive Species Control: Modeling impacts of invasive species on native ecosystems
- Climate Change Impacts: Projecting species range shifts under climate scenarios
Non-Ecological Applications
The mathematical structure of the model has been adapted to diverse fields:
- Epidemiology: Modeling host-pathogen dynamics, including COVID-19 transmission [8] [3]
- Economics: Analyzing business competition and market share dynamics [1]
- Social Sciences: Studying information spread and cultural dynamics
- Chemical Kinetics: Describing autocatalytic reactions [1]
The enduring legacy of the Lotka-Volterra model lies in its ability to capture essential features of interacting systems through a mathematically tractable framework, providing insights that transcend its original ecological context.
Functional responses are foundational components of mathematical models in ecology, describing the rate at which a predator consumes prey. This relationship is crucial for predicting the dynamics and stability of interacting populations. The concept was fundamentally advanced by C. S. Holling, who identified three primary forms of functional responses (Types I, II, and III) based on experimental data. A fourth type (IV) and the concept of ratio-dependence were later introduced to describe more complex interactions observed in nature. This document provides application notes and detailed protocols for researchers employing these critical functions in predator-prey interaction studies, framed within the broader context of developing more accurate and realistic mathematical models for ecosystem dynamics and resource management.
Theoretical Foundations of Functional Responses
Historical Context and Definitions
The pioneering work of Lotka and Volterra formed the basis of predator-prey theory but utilized a simplest linear functional response. Holling enhanced the theory significantly by classifying prey-dependent functional responses into three distinct types (I, II, and III) that account for predator satiation and other behavioral constraints. A functional response, or trophic function, quantifies the average amount of prey consumed per unit of time by a single predator as a function of prey density. The incorporation of more realistic functional responses has been essential for resolving paradoxes observed in classical models, such as the "paradox of enrichment" [11].
The Shift to Ratio-Dependence
Classical prey-dependent models, where consumption depends solely on prey density, sometimes lead to unrealistic dynamic patterns contradicting field observations. To address this, Arditi and Ginzburg proposed a spectrum of predator-dependent responses, with prey-dependence and ratio-dependence as two extremes. Ratio-dependence posits that the per capita predator growth rate depends on the ratio of prey to predator populations (N/P), providing a parsimonious way to model predator interference. This formulation often offers a more realistic null model for many natural systems, resolving inconsistencies between theoretical predictions and empirical data [11].
Classification, Formulations, and Quantitative Comparison
The table below summarizes the defining characteristics, mathematical formulations, and primary ecological applications of the standard Holling types and the ratio-dependent framework.
Table 1: Comparative Summary of Functional Response Types
| Type | Graphical Shape | Mathematical Formulation | Key Parameters | Typical Ecological Applications |
|---|---|---|---|---|
| Holling Type I | Linear increase, then constant [12] | ( \Phi_I(N) = \begin{cases} \frac{c}{2a}N, & N < 2a \ c, & N \geq 2a \end{cases} ) | (c): max consumption rate(a): half-saturation constant | Filter feeders (e.g., cladocerans) [12] [11], some parasitoids [11]. |
| Holling Type II | Concave, saturating [11] | ( g(N) = \frac{aN}{1 + ahN} ) | (a): attack rate(h): handling time | Arthropod predators [13], standard model for many consumers. |
| Holling Type III | Sigmoidal (S-shaped) [11] | ( g(N) = \frac{aN^2}{1 + ahN^2} )or ( \frac{aN^\theta}{1 + ahN^\theta} ) with ( \theta > 1 ) | (a): attack rate(h): handling time(\theta): shape parameter | Vertebrate predators, learning predators, systems with prey switching [11] [14]. |
| Holling Type IV | Humped (inhibited at high prey density) | ( g(N) = \frac{aN}{m + N^2} ) | (a): search rate(m): protection constant | Scenarios with prey toxicity or group defense [15]. |
| Ratio-Dependent | Varies with N/P ratio [11] [16] | ( g\left(\frac{N}{P}\right) = \frac{a\left(\frac{N}{P}\right)}{1 + ah\left(\frac{N}{P}\right)} ) (Type II form) | (a): attack rate(h): handling time | Systems with significant predator interference; often used as a basic minimal model for interference [11]. |
The following diagram illustrates the logical decision process for selecting an appropriate functional response type based on the known ecological characteristics of the predator-prey interaction.
Diagram 1: A workflow for selecting an appropriate functional response type based on the ecological characteristics of the predator-prey system.
Experimental and Modeling Protocols
Protocol 1: Parameterizing a Holling Type II Response from Feeding Experiments
Objective: To empirically determine the attack rate ((a)) and handling time ((h)) for a Holling Type II functional response.
Background: The disc equation, (g(N) = \frac{aN}{1 + ahN}), is the most common form. Parameter estimation requires data on consumption rates across a range of prey densities.
Materials and Reagents:
- Experimental Arenas: Appropriately sized containers to hold predator and prey.
- Predator Species: A cohort of size-matched, starved (for a standardized time) predator individuals.
- Prey Species: A large number of live prey items of uniform size and age.
- Environmental Control Chamber: To maintain constant temperature, light, and humidity during experiments.
Table 2: Key Research Reagent Solutions for Feeding Experiments
| Item | Specification / Function |
|---|---|
| Experimental Arena | Size must preclude predator satiation due to space limitation rather than time; environment should mimic natural habitat. |
| Starved Predators | Standardizes hunger levels across experimental replicates to ensure consistent motivational state. |
| Live Prey | Provides natural stimulus for predator attack and consumption behaviors. |
| Environmental Chamber | Controls for external abiotic factors that could influence predator activity and feeding rates. |
Procedure:
- Prey Density Series: Establish a series of prey densities (e.g., N = 5, 10, 20, 40, 80). Include enough replicates per density (e.g., n=5) to account for variability.
- Predator Introduction: Introduce a single, starved predator into each arena.
- Experimental Duration: Allow a fixed period for feeding (e.g., 24 hours). The duration must be short enough to prevent significant prey reproduction or natural death.
- Termination and Counting: Remove the predator and count the number of prey consumed ((C)).
- Data Analysis: Fit the data to the Holling Type II equation using non-linear regression software (e.g., in R or Python). The dependent variable is the number of prey consumed ((C)), and the independent variable is the initial prey density ((N)). The model to fit is: (C = \frac{aN}{1 + ahN}).
Troubleshooting:
- If consumption does not saturate at high densities, consider extending the range of prey densities tested.
- If variance is high at low densities, increase the number of replicates.
Protocol 2: Incorporating Time Delay in a Ratio-Dependent Model
Objective: To construct and analyze a discrete-time, ratio-dependent predator-prey model with a time delay, accounting for non-overlapping generations or seasonal reproduction.
Background: Discrete-time models are often more appropriate for species with distinct breeding seasons. Time delays can represent gestation or maturation periods. Standard discretization methods can lead to inconsistencies; the Nearly Exact Discretization Scheme (NEDS) is recommended [16].
Materials:
- Computational Software: Mathematica, MATLAB, or Python with scientific computing libraries (NumPy, SciPy).
- Parameter Values: Derived from literature or prior experimentation (e.g., intrinsic growth rates, mortality, conversion efficiency).
Procedure:
- Define the Continuous Model: Start with a delayed, ratio-dependent model. For example: [ \frac{dN}{dt} = r1 N - \epsilon P N, \quad \frac{dP}{dt} = P \left( r2 - \theta \frac{P(t-\tau)}{N} \right) ] where (\tau > 0) is the time delay [16].
- Apply NEDS Transformation: Use the NEDS to discretize the continuous model. This involves a novel transformation to ensure the discrete system reduces to the correct non-delay model when (\tau = 0) [16].
- Analyze the Discrete System:
- Find Fixed Points: Solve for the population densities where (N{t+1} = Nt) and (P{t+1} = Pt).
- Stability Analysis: Calculate the Jacobian matrix of the system at the fixed points. The eigenvalues of the Jacobian determine local stability.
- Bifurcation Analysis: Vary a key parameter (e.g., growth rate (r_1) or delay (\tau)) and observe transitions in system dynamics (e.g., to Neimark-Sacker bifurcations, leading to periodic or quasi-periodic behavior) [16] [13].
Troubleshooting:
- If the discrete model exhibits unrealistic behavior (e.g., negative populations), check the discretization method and time step size. NEDS is designed to preserve fundamental properties.
- If analysis of the high-dimensional discrete system is computationally intensive, consider using specialized bifurcation analysis software like MATCONT or DDE-BIFTOOL.
Advanced Formulations and Current Research Directions
Non-Smooth and Generalized Responses
Recent research explores functional responses that are non-smooth or have generalized forms, such as (p(x) = \frac{u(x)}{1+hu(x)^{m1}}) where (0 < m1 < 1). These "sub-critical" responses are non-Lipschitz and can lead to the phenomenon of finite-time extinction of the prey population, a dynamic impossible in classical smooth models. This has significant implications for pest control and epidemic models, where the goal is eradication [17].
Stochastic Models in Random Environments
Population dynamics are inevitably affected by environmental noise. A current research frontier involves incorporating stochasticity into functional response models. This is typically done by adding a noise term to parameters like the catchability coefficient or intrinsic growth rate, transforming ordinary differential equations into stochastic differential equations. Analysis then focuses on properties like stochastic permanence, extinction probability, and the existence of stationary distributions, providing a more robust framework for real-world predictions [18].
The Role of Fear and Other Non-Consumptive Effects
Beyond direct consumption, the fear of predators can induce changes in prey physiology and behavior (e.g., reduced foraging), which can reduce prey growth and reproduction rates. Modern models are beginning to incorporate these non-consumptive effects, often by multiplying the prey's intrinsic growth rate by a factor like (1/(1 + A y)), where (A) represents the fear effect. This effect can interact with the functional response to alter system stability and persistence [13].
The dynamics of predator-prey systems are fundamental to ecosystem stability and function. The integration of spatial and temporal components has revolutionized our understanding of these interactions, moving beyond the limitations of classical, non-spatial models. This document details the application notes and experimental protocols for studying these complex dynamics, with a specific focus on the roles of refuge (spatial heterogeneity providing prey safety), delay (temporal lags in biological responses), and heterogeneity (non-uniform distribution of individuals and resources). Framed within a broader thesis on mathematical models for predator-prey research, these guidelines are designed to equip researchers and scientists with the methodologies to quantitatively analyze how these factors influence population stability, pattern formation, and disease spread within ecological systems.
Key Theoretical Frameworks and Quantitative Data
The mathematical foundation for spatiotemporal predator-prey dynamics is built upon several key models and concepts. The classical Lotka-Volterra model, which describes the oscillatory nature of predator and prey populations, is often a starting point [8]. However, contemporary research extends this basic framework to incorporate greater biological realism, as summarized in the table below.
Table 1: Key Mathematical Frameworks in Spatiotemporal Predator-Prey Ecology
| Model/Framework Name | Key Components & Equations | Biological Interpretation | Key References |
|---|---|---|---|
| Classic Lotka-Volterra | ( \frac{dx}{dt} = rx - \alpha xy );( \frac{dy}{dt} = \beta xy - Dy ) | Describes basic oscillatory dynamics; prey grow exponentially, predators consume prey proportionally. | [8] [19] |
| Reaction-Diffusion Systems | ( \frac{\partial N}{\partial t} = d1 \Delta N + F(N, P) );( \frac{\partial P}{\partial t} = d2 \Delta P + G(N, P) ) | Captures population growth/interaction ((F, G)) and random spatial movement (diffusion terms (d1, d2)). | [20] [21] [22] |
| Eco-Epidemiological Models | Extends models to include Susceptible ((S)), Infected ((I)) compartments for prey and/or predators. | Integrates disease dynamics with predation, studying how infection alters ecosystem stability. | [20] [21] |
| Probabilistic Analytical Modelling (PAM) | ( E[Y] = \int{-\infty}^{\infty} h(x)fX(x) dx ) | A data-driven approach that incorporates natural variation in parameters (e.g., speed, turn angles) to predict interaction outcomes. | [23] |
| Geometric Escape Models | Determines optimal escape trajectory (ET) by maximizing time difference of arrival at a safety zone boundary. | Predicts prey escape angles by incorporating turn time and finite predator attack distance. | [24] |
Experimental Protocols and Methodologies
Protocol 1: Quantifying Prey Activity Curves in Response to Predator Threat
This protocol uses camera trap data and a deterministic model to estimate how prey deviate from their ideal activity patterns due to predator presence [25].
1. Research Question and Aim: To quantify the suppressive effect of a predator's activity on the diel activity pattern of a prey species and estimate the prey's sensitivity to predator presence.
2. Experimental Setup and Data Collection:
- Equipment: An array of motion-activated camera traps deployed across the study area (e.g., a wildlife reserve).
- Data Recording: Cameras continuously record timestamped observations of both predator and prey species over an extended period (e.g., several months).
- Data Pre-processing: Timestamps are converted to a circular (0-24 hour) timescale. Observations are aggregated into a histogram of activity counts for each species across the diel cycle.
3. Model Application and Parameter Estimation:
- Idealized Distribution Selection: Fit a known probability density function (e.g., normal, bimodal) to the prey's activity data in the absence of predators. This serves as the a priori ideal activity distribution, ( A_{\text{ideal}}(t) ) [25].
- Model Fitting: Use maximum likelihood estimation to fit a model that describes the observed prey activity, ( A_{\text{obs}}(t) ), as a function of the ideal distribution and predator observations. The model incorporates a sensitivity parameter (( s )) that scales the prey's deviation from its ideal pattern based on discrete predator detection events [25].
- Interpretation: A higher fitted sensitivity value (( s )) indicates the prey species is more behaviorally responsive to the predator's activity, resulting in a greater temporal shift to avoid encounters.
Protocol 2: Analyzing Spatiotemporal Eco-Epidemiological Dynamics
This protocol outlines the numerical analysis of a predator-prey system where a disease, following an SIS (Susceptible-Infected-Susceptible) framework, spreads within the prey population [20] [21].
1. Research Question and Aim: To simulate how disease transmission and spatial diffusion jointly influence the population dynamics and stability of a predator-prey system.
2. Model Formulation: Construct a system of partial differential equations (PDEs) based on the Lotka-Volterra framework, incorporating:
- Compartments: Susceptible prey ((us)), Infected prey ((ui)), Susceptible predators ((vs)), and Infected predators ((vi)).
- Ecological Processes: Prey logistic growth, predator mortality, predation rates ((\beta{ss}, \beta{si}, etc.)), and conversion efficiency.
- Epidemiological Processes: Disease transmission within prey (( \sigma{is} us ui )), recovery (( \omegai u_i )), and potential cross-species transmission.
- Spatial Processes: Diffusion terms (( D{us}, D{ui}, D{vs}, D{vi} )) to model random movement of each population compartment [20].
3. Numerical Simulation and Analysis:
- Discretization: Use an explicit Euler method for time-stepping and a cell-centered finite-difference scheme to discretize the spatial domain (e.g., a 1D or 2D grid) [20].
- Parameter Scenarios: Run simulations across a wide range of parameters:
- Output Analysis:
- Temporal Stability: Analyze time series of population densities to identify stable equilibria, limit cycles, or chaotic behavior.
- Pattern Formation: Visualize the spatial distribution of populations at steady state to identify the emergence of Turing patterns (e.g., spots, stripes, labyrinths) resulting from differential diffusion rates [21].
Protocol 3: Modeling Optimal Escape Trajectories with Biomechanical Constraints
This protocol employs a geometric model to understand the factors determining a prey's initial escape direction, moving beyond simplistic models [24].
1. Research Question and Aim: To determine the optimal escape trajectory (ET) for a prey individual that maximizes its chance of evading a predator, accounting for turn time and limited predator attack distance.
2. Experimental Data Collection:
- Kinematic Data: Using high-speed video recordings of predator-prey interactions (e.g., fish preying on fish), collect data on:
- Prey's initial orientation relative to the predator's approach path.
- Prey's turning radius and angular velocity.
- Predator's attack speed and the typical distance over which an attack is sustained.
- Measured escape trajectories (ETs) from real encounters.
3. Model Application and Fitting:
- Model Construction: Develop a geometric model where the optimal ET is defined as the direction that maximizes the time difference between the prey and the predator arriving at the edge of a designated "safety zone."
- Key Innovations:
- Incorporate the time required for the prey to turn from its initial orientation to the escape heading.
- Model the predator as having a finite attack endpoint, rather than chasing indefinitely [24].
- Model Fitting: Fit the model to the empirical ET data by adjusting parameters like the prey's turn rate and the predator's attack range. A successful model will predict the observed multimodal distribution of ETs (e.g., escapes at 20-50° and 150-180°), explaining them as outcomes of a trade-off between dodging and outrunning the predator [24].
Visualization of Workflows and System Dynamics
Workflow for Spatiotemporal Eco-Epidemiological Analysis
The following diagram outlines the integrated computational and experimental protocol for studying disease in spatial predator-prey systems.
Dynamics of a Delayed Predator-Prey System with Fear Effect
This diagram illustrates the logical relationships and feedback loops within a complex model incorporating fear, delay, and spatial dynamics.
The Scientist's Toolkit: Research Reagent Solutions
This section details the essential computational and analytical "reagents" required for implementing the protocols described in this document.
Table 2: Essential Research Tools for Spatiotemporal Predator-Prey Modeling
| Tool/Resource | Type | Primary Function | Example Application |
|---|---|---|---|
| Camera Trap Array | Field Equipment | Continuous, non-invasive monitoring of wildlife activity patterns. | Collecting timestamped data for estimating prey activity curves (Protocol 1.1) [25]. |
| High-Speed Video System | Laboratory/Field Equipment | High-temporal-resolution recording of fast kinematic interactions. | Quantifying escape trajectories, turn rates, and attack dynamics (Protocol 1.3) [23] [24]. |
| PDE Solvers (e.g., Finite Difference, Finite Element) | Computational Software | Numerical solution of systems of partial differential equations. | Simulating reaction-diffusion models to study pattern formation (Protocol 1.2) [20] [21] [22]. |
| Statistical Software (R, Python with pandas) | Analytical Environment | Data cleaning, statistical analysis, and model fitting. | Fitting probability distributions to kinematic data for PAM; calculating activity curve overlaps [25] [23]. |
| Probability Density Functions (PDFs) | Analytical Tool | Representing natural variation in biological parameters. | Serving as parameters in Probabilistic Analytical Models (PAM) to predict interaction outcomes [23]. |
| SIS (Susceptible-Infected-Susceptible) Framework | Modeling Framework | Compartmental structure for modeling diseases with no permanent immunity. | Structuring the epidemiological component of eco-epidemiological models (Protocol 1.2) [20] [8]. |
Predator-prey models are foundational to theoretical ecology, yet their traditional formulations often fail to capture the complexity of real-world interactions. The Lotka-Volterra model, while pioneering, makes biologically unjustified assumptions, such as cause and effect coinciding precisely and prey populations growing indefinitely without predators [8]. Modern ecological research has moved beyond these limitations by incorporating emergent properties—system-level behaviors that cannot be predicted from individual components alone [26] [27]. This framework provides powerful insights into three critical phenomena influencing population dynamics: Allee effects, fear responses, and cannibalism. These non-linear processes create feedback mechanisms that profoundly alter system stability, coexistence patterns, and extinction probabilities, requiring advanced mathematical approaches for accurate representation and analysis.
Theoretical Framework: Emergence in Ecological Systems
The Concept of Ecological Emergence
Emergence describes how macro-level patterns and properties arise from interactions among micro-level components in complex systems [26]. In ecology, this manifests when population or community-level behaviors cannot be deduced solely by studying individual organisms. These emergent properties result from self-organization processes driven by multiple interacting factors, including the high variability of system components, non-linear interaction structures, and feedback loops across different organizational levels [28]. The transition from individual-level processes to ecosystem-level patterns represents a fundamental shift in analytical perspective, moving beyond both reductionist and purely holistic approaches to ecological modeling.
Modeling Emergent Properties
Individual-based models (IBMs) provide a powerful framework for studying emergence by simulating system dynamics resulting from individual interactions and properties [28]. This approach allows researchers to analyze complex causal networks and identify driving forces behind higher-level ecological patterns. For predator-prey systems, this means population oscillations, stability thresholds, and extinction events can be understood as emergent consequences of individual behaviors and interactions, rather than as predetermined outcomes.
Core Concepts and Mathematical Foundations
Allee Effects: Positive Density Dependence
The Allee effect describes a positive correlation between population density/size and individual fitness, representing a departure from standard logistic growth models [29] [30]. Named after Warder C. Allee, this phenomenon occurs when reduced population size leads to decreased cooperation in activities such as mating, defense, or resource exploitation [31].
Table 1: Allee Effect Classification and Properties
| Type | Critical Threshold | Per Capita Growth Rate | Extinction Risk |
|---|---|---|---|
| Strong Allee Effect | Present (M > 0) | Negative below critical threshold | High (below threshold) |
| Weak Allee Effect | Absent (M ≤ 0) | Positive but reduced at low densities | Moderate |
| Demographic Allee Effect | Varies | Overall population growth rate affected | Population-level risk |
| Component Allee Effect | Not applicable | Specific fitness component affected | Individual-level consequences |
Mathematically, the multiplicative Allee effect can be incorporated into population models using an additional term. In a modified predator-prey system with Holling Type-II response, this appears as:
$$\begin{aligned} \frac{dx}{dt} &= rx\left(1-\frac{x}{k}\right)\frac{x}{m+x} -\frac{\alpha (1-A) x y}{\eta +(1-A)x } \ \frac{dy}{dt} &= y \left(-\beta + \frac{\gamma (1-A) x}{\eta +(1-A)x } \right) \end{aligned}$$
where m represents the Allee threshold, and A accounts for prey refuge [29]. When m > 0, the system exhibits a strong Allee effect with critical population threshold below which extinction occurs.
Fear Responses: Non-Consumptive Effects
Fear of predators triggers defensive behaviors in prey species that extend beyond direct predation. These non-consumptive effects can significantly impact prey reproduction, foraging, and physiology [32] [33]. Laboratory studies quantify fear through paradigms like Pavlovian fear conditioning, where neutral stimuli paired with aversive events become conditioned fear signals [34]. In social species, Observational Fear Learning allows individuals to acquire fear responses by witnessing conspecific reactions to threats [33].
The neurobiological mechanisms underlying fear involve conserved neural pathways across mammalian species. Key components include:
- Amygdala: Central to acquisition, storage, and expression of fear memories [33]
- Thalamus: Rapid threat detection and signal relay [33]
- Anterior Cingulate Cortex (ACC): Particularly important for social fear learning [33]
- Superior Colliculus and Pulvinar: Subcortical visual pathway for rapid processing of fearful stimuli [33]
Mathematically, fear effects can be incorporated as a modifying factor on prey growth rates or reproduction. For example, fear cost f can reduce the prey's intrinsic growth rate r in a predator-prey model:
$$\frac{dx}{dt} = \frac{rx}{1+fy} - \text{predation terms}$$
where y represents predator density [32].
Cannibalism: Intraspecific Predation
While not extensively covered in the search results, cannibalism represents another emergent phenomenon in ecological systems with significant population-level consequences. Cannibalism typically increases under conditions of resource scarcity or high population density, creating a density-dependent regulatory mechanism. This intraspecific predation can stabilize population dynamics by providing an alternative food source while reducing intraspecific competition.
Experimental Protocols and Methodologies
Quantifying Allee Effects in Laboratory Populations
Protocol Title: Experimental Detection and Parameter Estimation of Strong Allee Effects
Purpose: To empirically determine the presence and strength of Allee effects in model organisms and estimate critical population parameters.
Materials:
- Model organism cultures (e.g., Tribolium beetles, Daphnia, microbial populations)
- Controlled environment chambers
- Population monitoring equipment
- Statistical analysis software
Procedure:
- Establish multiple replicate populations across a range of initial densities (from very low to carrying capacity)
- Monitor population size and individual fitness metrics (growth rate, reproduction, survival) over multiple generations
- Calculate per capita growth rates as a function of population density
- Fit data to population growth models with and without Allee terms
- Use model selection criteria (AIC, BIC) to determine best-fitting model
- If Allee model is superior, estimate critical threshold parameters through non-linear regression
Data Analysis:
- Plot per capita growth rate against population density
- Fit both logistic (𝑟(1−𝑁/𝐾)) and Allee-modified (𝑟(1−𝑁/𝐾)(𝑁−𝑀)/𝐾) growth models
- Compare model fits using maximum likelihood methods
- Calculate confidence intervals for critical threshold parameter M
Fear Response Assessment in Model Organisms
Protocol Title: Behavioral and Physiological Quantification of Predator-Induced Fear Responses
Purpose: To measure fear responses in prey species using standardized behavioral paradigms and physiological correlates.
Materials:
- Experimental subjects (e.g., laboratory rodents, fish species)
- Predator cues (odor, visual models, or predator sounds)
- Video tracking system for behavioral analysis
- Physiological monitoring equipment (for heart rate, cortisol/corticosterone)
- Controlled testing arenas
Procedure:
- Habituation: Acclimate subjects to testing environment over multiple sessions
- Baseline Measurement: Record baseline behavior and physiology without predator cues
- Stimulus Presentation: Introduce predator cues following standardized protocols:
- For olfactory cues: Use consistent source and concentration
- For visual cues: Use realistic predator models with controlled movement
- For auditory cues: Use standardized playback equipment and amplitude
- Response Recording:
- Video record sessions for later behavioral scoring
- Continuously monitor physiological parameters
- Note latency, frequency, and duration of defensive behaviors
- Data Extraction:
- Score freezing behavior (complete immobility except respiration)
- Measure flight responses (speed, distance)
- Quantify risk assessment behaviors (stretched approach, orientation)
- Analyze physiological data synchronized with behavioral events
Analysis:
- Compare pre- and post-stimulus behavioral and physiological measures
- Use multivariate approaches to characterize response profiles
- Establish dose-response relationships where possible
Figure 1: Fear Response Experimental Workflow. This flowchart illustrates the sequential steps for quantifying predator-induced fear responses in model organisms, from initial habituation to final data analysis.
Discrete-Time Model Implementation for Systems with Non-Overlapping Generations
Protocol Title: Numerical Analysis of Predator-Prey Systems with Allee Effects and Fear Responses
Purpose: To implement and analyze discrete-time predator-prey models incorporating emergent properties using bifurcation theory and numerical simulation.
Materials:
- Mathematical computing environment (MATLAB, Python with NumPy/SciPy, Mathematica)
- Bifurcation analysis software (XPP/AUTO, COCO)
- Numerical integration algorithms (Euler, Runge-Kutta methods)
Procedure:
- Model Formulation:
- Discretize continuous-time model using forward Euler or more advanced methods
- Incorporate Allee effect via multiplicative term
x/(m+x) - Include fear effects as reduced growth rate or reproduction
- Add refuge terms where appropriate
Stability Analysis:
- Calculate equilibrium points (trivial, predator-free, coexistence)
- Compute Jacobian matrix at each equilibrium
- Evaluate eigenvalues to determine local stability
- Identify potential bifurcation parameters
Bifurcation Analysis:
- Use numerical continuation methods to track equilibrium branches
- Detect bifurcation points (saddle-node, Hopf, period-doubling)
- Calculate normal forms at bifurcation points where possible
Numerical Simulation:
- Simulate system dynamics across parameter ranges
- Construct bifurcation diagrams using parameter sweeping
- Calculate maximal Lyapunov exponents to identify chaotic regimes
Chaos Control (if needed):
- Implement control methods (OGY, delayed feedback) when chaotic dynamics detected
- Verify stabilization through numerical simulation
Implementation Example (Discrete Euler Method):
where δ is the discretization step size [29].
Research Reagent Solutions and Computational Tools
Table 2: Essential Research Resources for Studying Emergent Ecological Phenomena
| Resource Category | Specific Examples | Research Application |
|---|---|---|
| Model Organisms | Laboratory rodents (Rattus norvegicus), Daphnia spp., Tribolium castaneum, microbial communities | Experimental quantification of Allee effects and fear responses under controlled conditions |
| Behavioral Tracking | EthoVision, DeepLabCut, BORIS | Automated quantification of fear-related behaviors (freezing, flight, risk assessment) |
| Physiological Monitoring | Telemetry systems, cortisol/corticosterone ELISA kits, heart rate monitors | Correlation of behavioral fear responses with physiological stress indicators |
| Mathematical Software | MATLAB, Python (NumPy, SciPy), Mathematica, R | Numerical analysis of models, bifurcation analysis, and simulation |
| Bifurcation Analysis Tools | XPP/AUTO, COCO, MatCont | Advanced numerical continuation and bifurcation detection in nonlinear systems |
| Model Databases | BioModels, JWS Online | Access to curated mathematical models for validation and comparison |
Integrated Dynamics and Ecological Implications
Interplay Between Emergent Phenomena
The combination of Allee effects, fear responses, and cannibalism creates complex feedback mechanisms that profoundly influence ecosystem stability. Fear effects can potentially stabilize predator-prey oscillations by reducing prey growth rates, while strong Allee effects can create critical thresholds leading to sudden population collapses [32] [30]. The interplay between these factors demonstrates true emergent properties, where the system dynamics cannot be predicted by studying each factor in isolation.
Figure 2: Interrelationships Among Emergent Ecological Phenomena. This diagram illustrates the complex connections between Allee effects, fear responses, and cannibalism, and their combined impact on population dynamics and stability.
Management and Conservation Applications
Understanding these emergent phenomena has practical implications for conservation biology and ecosystem management. Populations subject to strong Allee effects require different management strategies, with particular attention to maintaining densities above critical thresholds. Similarly, recognizing the ecosystem-wide impacts of fear responses highlights the importance of preserving predator-prey relationships even when direct predation rates are low. The emergent properties framework provides a powerful approach for predicting system responses to anthropogenic disturbances and designing effective conservation interventions.
Allee effects, fear responses, and cannibalism represent crucial emergent properties that significantly alter predator-prey dynamics beyond traditional model predictions. The complex, non-linear interactions between these phenomena create feedback mechanisms that can stabilize or destabilize ecological systems, often in counterintuitive ways. Mathematical models incorporating these factors, particularly through individual-based approaches and discrete-time formulations, provide essential tools for understanding population trajectories, extinction risks, and coexistence patterns. Experimental protocols for quantifying these effects continue to evolve, combining behavioral observation, physiological monitoring, and advanced numerical analysis. As ecological research increasingly recognizes the importance of these emergent properties, their integration into conservation planning and ecosystem management will be essential for addressing biodiversity challenges in rapidly changing environments.
Understanding the dynamics between native and invasive species is a central challenge in modern ecology. The introduction of an invasive predator into an established native predator-prey system can profoundly alter ecological equilibrium, leading to significant conservation implications [35]. Mathematical modeling provides an indispensable framework for simulating these complex interactions, forecasting long-term impacts, and evaluating potential management strategies beyond the limitations of geographical and temporal constraints of field studies [35]. This document outlines the key mathematical frameworks and experimental protocols for studying three-species systems comprising native prey, native predators, and invasive predators, with a focus on mechanisms that can lead to coexistence.
Theoretical Framework and Key Models
Core Three-Species Model for Post-Invasion Dynamics
A general model for a system with one native prey ((X1)), one native predator ((X2)), and one invasive predator ((X_3)) can be structured as follows [35]:
[ \begin{aligned} \frac{dX1}{dt} &= r X1 \left(1 - \frac{X1}{k}\right) - a(1-m)X1X2 - b X1X3 \ \frac{dX2}{dt} &= e2 a (1-m) X1 X2 - d2 X2 - c{12} X2 X3 + M \ \frac{dX3}{dt} &= e3 b X1 X3 - d3 X3 - c{21} X2 X_3 - H \end{aligned} ]
Table 1: Parameters for the core post-invasion dynamic model
| Parameter | Biological Meaning |
|---|---|
| (r) | Prey intrinsic growth rate |
| (k) | Prey carrying capacity |
| (a, b) | Attack rates of native and invasive predators |
| (m) | Fraction of prey using refuge vs. native predator |
| (e2, e3) | Conversion efficiencies for native and invasive predators |
| (d2, d3) | Mortality rates of native and invasive predators |
| (c{12}, c{21}) | Interspecific competition coefficients |
| (M) | Native predator reintroduction/migration rate |
| (H) | Harvesting rate of invasive predator |
This model incorporates critical ecological mechanisms:
- Prey Defenses: Prey use refuges (parameter (m)) as an anti-predator strategy against the native predator, but due to prey naivety, these defenses are assumed ineffective against the novel invasive predator [35].
- Inter-predator Competition: Direct competition between predators is modeled via the terms (c{12}X2X3) and (c{21}X2X3) [35].
- Management Interventions: The model includes active management through the harvesting of invasive predators ((H)) and the reintroduction or migration of native predators ((M)) to bolster their population [35].
- Invader Disadvantages: Invasive predators may face physiological challenges in a novel habitat, which can be represented by a lower conversion efficiency ((e_3)) [35].
Hyperpredation Model
An alternative model formulation focuses on the "hyperpredation" effect, where an invasive prey species leads to an increase in a shared predator population, intensifying predation pressure on a native prey species [36]. The following system models the dynamics between a fox population ( (V) ), an invasive cottontail population ( (S) ), and a native hare population ( (L) ):
[ \begin{aligned} \frac{dV}{dt} &= V \left( r - m - c{VV}V \right) + e (a S + b L)V \ \frac{dS}{dt} &= S \left( s - n - c{SS}S \right) - a V S \ \frac{dL}{dt} &= L \left( u - p - c_{LL}L \right) - b V L \end{aligned} ]
Table 2: Key differences between the Core and Hyperpredation Models
| Feature | Core Post-Invasion Model | Hyperpredation Model |
|---|---|---|
| System Focus | Established invasive predator | Invasive prey & shared predator |
| Key Mechanism | Direct competition between predators | Apparent competition via shared predator |
| Prey Naivety | Explicitly included | Not a primary focus |
| Management Levers | Harvesting ((H)), Reintroduction ((M)) | Not explicitly included |
The hyperpredation model highlights apparent competition, where the invasive prey (cottontail) and native prey (hare) do not compete directly but interact negatively through a shared enemy (fox) [36]. An increase in the invasive prey can sustain a larger predator population, thereby magnifying the predatory impact on the native prey.
Experimental and Field Protocols
Protocol for Parameterizing the Core Model from Field Data
Objective: To estimate parameters for the core three-species model to predict system trajectories and test management scenarios.
Workflow:
- Population Monitoring: Conduct longitudinal transect or camera trap surveys to collect time-series data on the densities of native prey, native predators, and invasive predators.
- Predation Rate Estimation:
- Functional Response Experiments: In controlled mesocosm settings, quantify the attack rates ((a, b)) and handling times of native and invasive predators on the native prey.
- Prey Preference: Determine if the invasive predator is a specialist or generalist.
- Competition Assay: Design experiments to measure the interference competition coefficients ((c{12}, c{21})) by observing direct interactions or resource exploitation overlap between native and invasive predators.
- Demographic Parameter Estimation: Use mark-recapture or telemetry studies to estimate natural mortality rates ((d2, d3)) and reproduction rates from field data.
- Model Fitting and Validation: Use numerical optimization techniques to fit the model equations to the time-series data, estimating unknown parameters. Validate the model by comparing its predictions to a withheld portion of the data.
Diagram 1: Workflow for parameterizing a three-species model from field and experimental data.
Protocol for Testing Coexistence Mechanisms
Objective: To empirically validate theoretical coexistence mechanisms, such as habitat facilitation and localized impact.
Workflow (Adapted from a Marine System Study [37]):
- Correlative Field Survey:
- Measure the abundance and spatial distribution of all three species (e.g., seagrass, pen shells, sea urchins).
- Statistically test for associations, such as whether a foundational species (pen shell) facilitates the presence of a key consumer (sea urchin).
- Manipulative Experiments:
- Exclusion: Use cages or other barriers to exclude the herbivore/predator from specific areas and quantify the impact on the prey/habitat-forming species.
- Translocation: Conduct behavioral assays to test the consumer's reluctance to move away from its facilitator.
- Mechanism Integration:
- Synthesize results to confirm the coexistence mechanism. In the studied system, persistence was attributed to: (i) the sea urchin's behavioral reluctance to move far from pen shells, localizing its grazing impact; (ii) the sparse distribution of the facilitator (pen shells); and (iii) the resistance and regrowth capacity of the seagrass [37].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential "Reagents" for Three-Species Systems Research
| Category / Tool | Specific Examples & Functions |
|---|---|
| Mathematical Frameworks | Lotka-Volterra Base: Provides the foundational structure for modeling consumer-resource interactions [35] [36]. Bifurcation Analysis: Used to determine critical parameter thresholds where system stability changes (e.g., from coexistence to extinction) [35]. |
| Computational & Analytical Tools | Numerical Simulation Software (MATLAB, Mathematica): Solves systems of differential equations and performs time-series simulations [35]. Spatially-Explicit Agent-Based Models: Captures the effects of individual movement and local interactions on population patterns [38]. |
| Field & Experimental Techniques | Camera Trapping & GPS Telemetry: Non-invasively monitors animal behavior, distribution, and predation events. Stable Isotope Analysis: Trophic position and diet composition of predators. Mesocosm Experiments: Controlled, replicated experiments to test specific interactions (e.g., functional responses) [36]. |
| Emerging Paradigms | Reinforcement Learning (RL) Models: Models where individuals adaptively learn optimal behaviors (e.g., movement), promoting stable coexistence even under conditions where classic models predict extinction [38]. |
Advanced Modeling: The Reinforcement Learning Approach
A frontier in ecological modeling involves combining game theory with reinforcement learning (RL). In this paradigm, individuals are not pre-programmed with fixed behaviors but learn optimal strategies, such as when and where to move, based on their local environment to maximize long-term rewards [38].
In a spatial Rock-Paper-Scissors (RPS) model, a metaphor for cyclic competition, individuals' mobility is adaptively regulated via a Q-learning algorithm. The "state" ( (s) ) for an individual is defined by its local environment (e.g., the number of prey and predators in its neighborhood). The available "actions" ( (a) ) typically include moving to an adjacent site or staying. The Q-table, shared by individuals of the same species, is updated iteratively to learn the value of each action in each state [38].
Key Finding: RL-powered individuals can achieve stable coexistence with low extinction probabilities even under high baseline mobility rates, a condition that leads to extinction in classical models with fixed mobility. Mechanistic analysis reveals that individuals develop two key behavioral tendencies: survival-priority (escaping from predators) and predation-priority (remaining near prey). Coexistence emerges from a balance between these two tendencies [38].
Diagram 2: The Q-learning loop for adaptive behavior in an ecological agent.
Computational Methods and Cross-Disciplinary Applications
Predator-prey interactions represent a fundamental ecological motif, the understanding of which is critical for insights into population dynamics, ecosystem stability, and evolutionary adaptation [39]. Mathematical modeling provides the essential toolkit for quantifying these complex interactions, transforming conceptual understanding into a formal, testable framework [40]. The progression from conceptual to mathematical models marks a critical step in systems biology, enabling researchers to move from qualitative descriptions to quantitative predictions and a deeper understanding of system-level function and organization [40].
This application note details the primary mathematical frameworks—Ordinary Differential Equations (ODEs), Discrete-Time models, and Stochastic Differential Equations (SDEs)—used in the study of predator-prey dynamics. We provide a structured comparison, detailed experimental protocols for model implementation and analysis, and a scientific toolkit to guide researchers in selecting and applying the appropriate modeling paradigm for their specific research context.
The choice of modeling framework dictates the nature of the questions one can answer. The three primary frameworks differ in their treatment of time, state variables, and inherent uncertainty.
Table 1: Comparison of Primary Predator-Prey Modeling Frameworks
| Framework | Temporal Domain | State Variable Nature | Key Strengths | Ideal Application Context |
|---|---|---|---|---|
| Ordinary Differential Equations (ODEs) | Continuous | Deterministic, Continuous | + Captures smooth, continuous dynamics+ Mature analytical stability theory+ Computationally efficient for large systems | Modeling well-mixed populations with large sizes and predictable dynamics [41] [42] |
| Discrete-Time Models | Discrete | Deterministic or Stochastic | + Naturally fits discrete data (e.g., annual censuses)+ Can exhibit rich dynamics (chaos)+ Computationally straightforward to simulate | Systems with non-overlapping generations or data collected at fixed intervals [42] |
| Stochastic Differential Equations (SDEs) | Continuous | Stochastic, Continuous | + Incorporates environmental stochasticity+ More realistic for finite populations+ Can model noise-driven transitions | Systems where random environmental fluctuations significantly impact dynamics [39] [41] [42] |
Advanced and Hybrid Modeling Approaches
Beyond the foundational frameworks, modern research often employs more sophisticated techniques to capture specific biological phenomena.
Fractional-Order Differential Equations extend classical ODEs by incorporating memory effects, where the rate of change depends on the entire history of the system rather than just the current state. This is particularly relevant for modeling predator-prey interactions with genetic or long-term temporal dependencies [43]. For example, a fractional-order model incorporating a double Allee effect (where multiple mechanisms suppress growth at low population densities) and a Holling Type-I functional response can be expressed using the Caputo derivative, revealing complex stability landscapes and bifurcation behaviors not seen in classical models [43].
Agent-Based Models (ABMs) and Particle-Level SDEs take a bottom-up approach by defining rules for individual agents (e.g., individual fish in a school). Macro-scale patterns like schooling, dispersal, and collective hunting emerge from simple local interaction rules such as attraction, repulsion, and alignment, combined with environmental noise [39]. This framework is powerful for probing the individual-level mechanisms that underpin population-level phenomena.
Quantitative Analysis of Model Behaviors and Parameters
The predictive power of a model lies in its parameters, which must be carefully estimated and analyzed.
Table 2: Key Parameters and Stability Conditions in Generalized Predator-Prey Models
| Parameter/Sensitivity | Mathematical Expression | Impact on Equilibrium Stability | Biological Interpretation |
|---|---|---|---|
| Prey Growth Rate (r) | dx/dt = r x - f(x,y) y | Higher values can destabilize equilibrium, leading to limit cycles [41]. | Intrinsic capacity of the prey population to increase in the absence of predators. |
| Attack Rate Log Sensitivity to Prey (fₕ) | fₕ = (∂f/∂h)(h/f) | Positive values (fₕ > 0) stabilize the equilibrium. A Type III functional response provides this [41]. | Measures how the predator's attack rate changes with prey density. |
| Attack Rate Log Sensitivity to Predator (fₚ) | fₚ = (∂f/∂p)(p/f) | Negative values (-1 < fₚ < 0) stabilize the equilibrium. This represents mutual interference [41]. | Measures how the predator's attack rate changes with its own density. |
| Stability Criterion | -1 < fₚ < r fₕ | Defines the parameter region for a stable equilibrium [41]. | Combines the effects of prey and predator-dependent attack rates. |
Experimental Protocols for Model Implementation
Protocol 1: Implementing and Analyzing a Stochastic Particle-Based Model
Objective: To simulate the emergence of collective predator-prey dynamics from individual-based movement rules using an SDE framework [39].
Workflow: The following diagram outlines the sequential steps for implementing a stochastic particle-based model.
Materials:
- Software: Programming environment with SDE solvers (e.g.,
DifferentialEquations.jlin Julia [44]). - Computational Resources: Standard desktop or high-performance computing cluster for large-scale simulations.
Procedure:
- System Definition:
- Define the spatial domain and the number of individual predators ((Np)) and prey ((Nv)).
- Set initial conditions (positions, velocities).
- Parameterization:
- For prey agents, define parameters for intra-species interactions: attraction (( \alpha )), repulsion (( \beta )), and alignment (( \gamma )) forces [39].
- For predator agents, define a predation strategy (e.g., center attack targeting the prey school centroid, or nearest attack targeting the closest prey).
- Set the intensity of environmental noise.
- SDE Formulation: For each agent (i), formulate its motion as an SDE of the form: ( dXi = \mui(\mathbf{X}) dt + \sigmai dWt ) where ( \mui ) is the deterministic drift term from interaction rules, and ( \sigmai dW_t ) is the stochastic Wiener process representing noise [39].
- Numerical Solution: Implement a numerical scheme (e.g., Euler-Maruyama) to solve the coupled SDE system over a defined time span.
- Simulation & Analysis:
- Execute multiple stochastic realizations.
- Quantify emergent metrics such as prey survival rate, predator hunting efficiency, and spatial group structure (e.g., polarization, swarm cohesion).
Protocol 2: Parameter Estimation for Stochastic Models with Multi-Type Data
Objective: To accurately estimate parameters of a stochastic predator-prey model by combining time-series data of population densities with direct kill rate observations [42].
Workflow: The following diagram illustrates the integrated data approach for robust parameter estimation.
Materials:
- Data: Time-series data of predator and prey population densities/densities, coupled with periodic direct measurements of per-capita kill rates.
- Software: Statistical software with optimization and MCMC capabilities (e.g.,
Optimization.jl[44], Stan, or custom scripts in R/Python).
Procedure:
- Model Specification: Define a discrete-time stochastic predator-prey model. For example, a model with a stochastic functional response ( Ft ) [42]: ( N{t+1} = Nt \exp\left(r (1 - Nt/K) - a Pt + \epsilont^{(1)}\right) ) ( P{t+1} = Pt \exp\left(c Ft(Nt, Pt) - d + \epsilont^{(2)}\right) ) ( Ft = \frac{\alpha Nt}{1 + \alpha h Nt} \exp(\etat) ) where ( \epsilont ) and ( \etat ) are noise terms.
- Objective Function: Construct a likelihood function that incorporates both the density data and the kill rate data. This combines a state-space model likelihood for the densities with a direct likelihood for the observed kill rates given the model's ( F_t ).
- Parameter Estimation:
- Frequentist Approach: Use maximum likelihood estimation (MLE) via iterative optimization algorithms to find the parameter set that maximizes the joint likelihood.
- Bayesian Approach: Use Markov Chain Monte Carlo (MCMC) sampling to obtain the posterior distribution of the parameters, given the data and prior distributions.
- Identifiability Analysis:
- Frequentist: Calculate the Fisher Information Matrix (FIM) from the likelihood. A high condition number of the FIM indicates potential practical non-identifiability [42].
- Bayesian: Assess the posterior-prior overlap (PPO); high overlap for a parameter suggests it is not well informed by the data [42].
- Model Selection: Use information criteria (e.g., AIC, BIC) or Bayesian model comparison to select between different model structures (e.g., with vs. without predator-dependence in the attack rate).
Model Validation and Invalidation
In the context of a scientific thesis, it is crucial to understand that models are not "validated" in the sense of being proven correct. Instead, the process involves attempting to invalidate models by demonstrating their incompatibility with experimental data [45]. A model that withstands repeated, rigorous invalidation attempts may be considered provisionally adequate for its intended purpose.
Methodology for Model Invalidation: For a model described by ODEs ( \dot{x} = f(x, p) ) and a set of experimental data points ( (ti, \hat{x}i) ) with uncertainty bounds, the model can be invalidated if one can prove that no admissible parameter set ( p ) can produce a model trajectory that fits all the data points within their experimental error bounds [45]. This can be framed as a feasibility problem and addressed using computational tools from convex optimization, such Semidefinite Programming and Sum-of-Squares (SOS) optimization, which can provide a certificate of invalidation without requiring exhaustive parameter sampling [45].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Computational Tools for Predator-Prey Modeling
| Tool Category | Specific Tool / Software | Primary Function | Application Note |
|---|---|---|---|
| Equation Solvers & Modeling | DifferentialEquations.jl (Julia) [44] |
Solves ODEs, SDEs, DDEs, and other differential equations. | The cornerstone of the SciML ecosystem; offers high performance and a unified interface for diverse problem types [44]. |
| Modeling & Symbolics | ModelingToolkit.jl (Julia) [44] |
A symbolic system for acausal modeling and automated equation transformations. | Automatically parallelizes code and simplifies the handling of large, complex models through structural simplification [44]. |
| Optimization & Parameter Estimation | Optimization.jl (Julia) [44] |
Provides a unified interface for local, global, gradient-based, and derivative-free optimization. | Essential for parameter fitting and model calibration; integrates with differential equation solvers for inverse problems [44]. |
| Model Invalidation | SOSTOOLS (MATLAB) [45] | A toolbox for formulating and solving Sum-of-Squares optimization problems. | Can be used to generate certificates of model invalidation for polynomial ODE models, providing a rigorous mathematical proof [45]. |
| Bayesian Inference | DiffEqBayes.jl (Julia) [44] / Stan |
Provides Bayesian parameter estimation for differential equations using MCMC and other sampling techniques. | Ideal for quantifying uncertainty in parameter estimates and for working with complex models where likelihoods are intractable [44]. |
Discretization, the process of converting continuous-time models into discrete-time formulations, is fundamental for computational analysis and simulation of dynamical systems. Within mathematical ecology, specifically predator-prey research, this process enables numerical investigation of population dynamics and the implementation of digital control strategies. However, incorporating time delays—which represent biologically critical processes like gestation, maturation, or resource regeneration—introduces significant theoretical and practical challenges. The core issue is consistency: ensuring the discrete model accurately preserves the dynamical properties of the original continuous system, particularly when delay parameters vanish or approach zero [46].
This article details the specific consistency challenges that arise when discretizing delayed predator-prey systems and provides structured application notes and experimental protocols to address them. We frame these methodologies within a broader thesis on mathematical modeling of ecological interactions, emphasizing techniques that maintain biological realism and mathematical integrity during the discretization process.
Fundamental Consistency Challenges in Delayed Systems
The primary challenge in discretizing delayed differential equations (DDEs) is the failure of many standard techniques to reduce correctly to their non-delay counterparts. This inconsistency manifests in two key areas:
- Characteristic Equation Mismatch: When the delay parameter ( \tau ) is set to zero in the characteristic equation of a discretized delayed system, it often does not yield the characteristic equation of the discretized non-delay model. This indicates a fundamental structural discrepancy [46].
- Dimensionality and Discretization Method: Continuous-time DDEs are inherently infinite-dimensional. Discretization must produce a high-dimensional discrete system that faithfully represents this complexity. The choice of discretization scheme—such as Euler method, nonstandard finite difference methods, or the Nearly Exact Discretization Scheme (NEDS)—critically impacts this consistency [46].
Table 1: Common Discretization Techniques and Their Properties in Delayed Systems
| Technique | Key Principle | Advantages | Consistency Challenges |
|---|---|---|---|
| Euler Method | Forward difference approximation of derivatives. | Simple implementation. | Often fails to preserve stability; prone to inconsistencies as ( \tau \to 0 ) [46]. |
| Nonstandard Finite Difference (NSFD) | Non-local representation of nonlinear terms; denominator functions. | Can preserve positivity and boundedness of solutions [47]. | Consistency is not guaranteed; depends on careful choice of denominator functions [46]. |
| Nearly Exact Discretization Scheme (NEDS) | Aims to match the solution of the discrete system to the continuous system at discrete time points. | High accuracy; can be designed for consistency as ( \tau \to 0 ) [46]. | Requires a novel transformation of the original system; more complex implementation. |
| Functional Continuous Runge-Kutta (FCRK) | Uses continuous interpolants within Runge-Kutta steps for handling past states. | Suitable for systems with distributed delays; formal convergence theory exists [48]. | Computational intensity increases with the number of discrete delays used to approximate a distributed delay. |
Diagram 1: Workflow highlighting the divergent outcomes of different discretization paths for delayed systems. The choice of technique directly determines whether the resulting discrete model is consistent.
Application Note: Discretizing a Ratio-Dependent Predator-Prey Model with Delay
This section provides a detailed protocol for applying the Nearly Exact Discretization Scheme (NEDS) to a specific ecological model, overcoming the consistency challenges outlined above.
Model Formulation and Objective
Consider a continuous-time, ratio-dependent predator-prey model with a single discrete delay ( \tau ) [46]: [ \begin{aligned} \frac{dN(t)}{dt} &= r1 N(t) - \epsilon P(t) N(t), \ \frac{dP(t)}{dt} &= P(t)\left(r2 - \theta \left(\frac{P(t-\tau)}{N(t)}\right)\right), \end{aligned} ] where ( N(t) ) and ( P(t) ) are the prey and predator population densities, respectively. The parameters ( r1, r2, \epsilon, \theta ) are positive constants representing intrinsic growth rates, predation rate, and competition intensity. The objective is to obtain a discrete system that reduces to the correct non-delay discrete model when ( \tau = 0 ).
Experimental Protocol: Consistent Discretization via NEDS
Protocol 1: Consistent Discretization of a Delayed Ratio-Dependent Model
Objective: To discretize the delayed ratio-dependent predator-prey model into a consistent high-dimensional discrete system using the Nearly Exact Discretization Scheme (NEDS).
Reagents and Computational Tools:
- Software: MATLAB, MATHEMATICA, or Python (with SciPy, NumPy libraries).
- Numerical Solver: For cross-validating continuous model trajectories (e.g.,
ddesdin MATLAB). - Bifurcation Analysis Tool: MATCONT or a custom implementation for analyzing the discrete map.
Procedure:
- System Transformation:
- Introduce a new state variable to incorporate the delay term. Define ( Q(t) = P(t - \tau) ). The original second-order DDE is now part of a larger, non-delayed system.
- This transformation is a critical step to avoid the direct discretization of the delayed argument, which often leads to inconsistency [46].
Apply the Nearly Exact Discretization Scheme (NEDS):
- Discretize the transformed system using the NEDS methodology. This scheme is designed to match the solutions of the discrete and continuous systems at the discretization time points.
- The resulting discrete system will be high-dimensional. For a delay ( \tau ) and step size ( \delta ), the dimension is approximately ( l+2 ), where ( l = \tau / \delta ) [46].
Consistency Verification:
- Theoretical Check: In the characteristic equation of the discretized system, analytically set the delay parameter ( \tau = 0 ). Verify that the resulting equation is identical to the characteristic equation of the discretized version of the original model without any delay.
- Numerical Check: Simulate the discrete model with ( \tau = 0 ) and compare its equilibrium points and local stability properties with the discretized non-delay model. They should be identical.
Dynamical Analysis (Post-Discretization):
- Fixed Point Analysis: Compute the fixed points of the high-dimensional discrete map.
- Stability and Bifurcation: Evaluate the Jacobian matrix at the fixed points. Vary the delay parameter ( \tau ) to identify parameter regions where a complex conjugate pair of eigenvalues crosses the unit circle, indicating a Neimark-Sacker bifurcation (the discrete analogue of a Hopf bifurcation) [46].
Troubleshooting:
- Failure in Consistency Check: If the consistency verification fails, review the initial transformation and the application of the NEDS integrator. Ensure the discretization of the non-delay terms is exact for linear systems.
- Numerical Instability: If the discrete system exhibits unbounded growth not present in the continuous model, reduce the step size ( \delta ) or check the implementation of the NEDS formulas.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Computational Tools for Discretizing and Analyzing Delayed Predator-Prey Models
| Tool / Reagent | Function/Description | Application Example |
|---|---|---|
| NEDS Framework | Provides a discretization methodology that minimizes consistency error between continuous and discrete models. | Achieving correct reduction to non-delay case in ratio-dependent models [46]. |
| Functional Continuous Runge-Kutta (FCRK) Methods | A class of numerical integrators for DDEs that use continuous interpolants to handle past states accurately. | Simulating models with distributed delays by discretizing the convolution integral [48]. |
| Linear Chain Technique | Converts a distributed delay with specific kernels (e.g., Gamma) into a system of ODEs without delay. | Modeling physiological processes like gestation where the delay is not fixed but distributed [48]. |
| Hybrid Control Methods | Feedback control algorithms designed to suppress bifurcations and chaos in discrete-time systems. | Stabilizing Neimark-Sacker bifurcations in a discretized model to prevent population oscillations [46] [49]. |
| dSPACE Real-Time Interface | Hardware-in-the-loop (HIL) simulation platform for validating digital control algorithms. | Experimental validation of discretization-based controllers for biological systems [50]. |
Advanced Application: Handling Distributed Delays
Many biological processes are better described by distributed delays, which account for a continuum of past states rather than a single fixed delay. The model in Eq. (1.1) incorporates a convolution integral with a kernel ( k(s) ) [48].
Protocol 2: Discretization of Models with Distributed Delays
Objective: To accurately simulate a predator-prey model with a compactly supported distributed delay by discretizing it into a multi-delay discrete DDE.
Procedure:
- Kernel Selection: Choose a probability distribution kernel ( k(s) ) (e.g., uniform, gamma) defined on the interval ( [\tau{\text{min}}, \tau{\text{max}}] ).
- Quadrature Discretization: Approximate the convolution integral ( \int{\tau{\text{min}}}^{\tau{\text{max}}} x(t-s)k(s)ds ) using a numerical quadrature rule (e.g., trapezoidal rule). This yields a weighted sum ( \sum{i=1}^{m} wi x(t - \taui) ), effectively converting the distributed delay into ( m ) discrete delays.
- Simulate Multi-Delay DDE: Use a specialized solver for discrete DDEs (like
ddesdin MATLAB) to simulate the resulting system with multiple delays ( \tau1, \tau2, ..., \tau_m ). - Error Management: The overall simulation error is governed by the least accurate component. Choose the quadrature method's order and the DDE solver's step size such that their error bounds are comparable to preserve the convergence order of the overall numerical method [48].
Diagram 2: The pathway for simulating distributed delay differential equations by converting them into multi-delay discrete DDEs via quadrature, allowing the use of standard solvers.
The discretization of delayed systems in predator-prey modeling presents a significant challenge where mathematical rigor is essential for ecological validity. Standard techniques like the Euler method are often insufficient, leading to models that fail fundamental consistency tests. As detailed in these application notes, advanced methods such as the Nearly Exact Discretization Scheme (NEDS) and Functional Continuous Runge-Kutta (FCRK) methods, when applied via structured protocols, provide a robust pathway to consistent and accurate discrete-time models. Adhering to these protocols ensures that computational investigations of complex ecological dynamics, such as bifurcations and chaos, are built upon a reliable mathematical foundation, thereby enhancing the predictive power and relevance of mathematical ecology in conservation and management.
Application Notes
Agent-based modeling (ABM) is a powerful computational approach for simulating the emergent collective dynamics of predator and prey populations by modeling individual agents and their interactions. Within the broader context of mathematical models for predator-prey research, ABMs provide a unique bottom-up perspective that complements traditional differential equation models, such as those by Lotka and Volterra, by capturing individual heterogeneity, spatial explicitity, and complex adaptive behaviors [51] [52] [53]. These notes detail the application of ABM to study the collective hunting strategies of predators and the evasive schooling behaviors of prey.
Key Behavioral Mechanisms and Their Mathematical Representation
The dynamics of collective movement in agent-based models are governed by a set of core behavioral stimuli. For prey species, forming schools is an evolutionary adaptation that confers benefits like more efficient predator avoidance [53]. For predators, collective hunting can increase hunting success rates. The following rules are typically encoded for each agent:
- Repulsion: A short-range force that prevents collisions between nearby individuals. It is often modeled using a Morse or Lennard-Jones-type potential to create a zone of repulsion around each agent [53].
- Attraction: A long-range force that promotes group cohesion, ensuring individuals do not become isolated. This is often directed towards the perceived center of mass of nearby groupmates [53] [51].
- Alignment: A medium-range force that prompts individuals to match the velocity and heading of their neighbors, leading to synchronized movement [53].
- Predator Avoidance (for prey): A stimulus that causes prey agents to move directly away from a detected predator. The strength of this repulsion can be modulated by factors like distance to the predator [53] [54].
- Predator Pursuit (for predators): A stimulus that directs predator agents towards prey. Hunting strategies can vary from targeting the nearest prey to a "confused" strategy where the predator is attracted to the center of mass of the prey school [53].
In mathematical terms, the resultant direction of motion for an agent is often calculated as a weighted sum of the unit vectors representing each active stimulus [53]. A critical modeling constraint is that the sum of these weights is often fixed (e.g., to 1) to avoid the unrealistic simultaneous maximization of all movement traits [53]. The speed of an agent may be set as a constant [53] [51] or determined by physiological limits and the purpose of movement.
Quantitative Insights from ABM Studies
ABM simulations generate quantitative data on group-level patterns emerging from individual interactions. The following table summarizes key metrics and findings from relevant studies.
Table 1: Quantitative Metrics and Outcomes from Agent-Based Models of Predator-Prey Interactions
| Metric Category | Specific Metric | Exemplary Finding / Value | Source Context |
|---|---|---|---|
| Spatial Group Metrics | Equilibrium Inter-Particle Spacing | Can be derived analytically from model coefficients in systems with only attraction and repulsion. | [53] |
| Group Polarization | Degree of alignment in group heading; high values indicate coordinated motion. | Implied from [53] | |
| Interaction Outcomes | Hunter Success Rate | Varies with predator strategy (e.g., confused vs. target nearest) and noise levels in control. | [53] [55] |
| Prey Survival Rate | Influenced by stochasticity in predator-prey interactions; varying noise levels can selectively favor prey or predator. | [55] | |
| Behavioral Metrics | Probability of Becoming a "Conflict" Animal | In human-wildlife models, reduced by managing anthropogenic food sources more than by deterrence. | [54] |
| Foraging Efficiency | Measured as energy intake per unit time; validated against real animal movement data. | [54] |
Advantages over Alternative Modeling Frameworks
Compared to the classical Lotka-Volterra or Rosenzweig-MacArthur models based on ordinary differential equations (ODEs), ABMs offer distinct advantages for studying collective behavior [51] [52]:
- Individual Heterogeneity: ABMs can assign unique traits (e.g., size, personality, experience) to each agent, which is difficult to capture in population-level ODEs.
- Local Interactions and Emergence: Global patterns like coordinated schooling and hunting emerge from simple, localized rules of interaction, without being pre-programmed.
- Spatial Explicity: Agents operate in a explicit (often 2D or 3D) space, allowing for the study of spatial structure, terrain effects, and territory.
- Adaptation and Learning: Agents can be endowed with memory and learning capabilities, allowing them to adapt their behavior based on past experiences, such as a dolphin learning to hunt more effectively [55].
Experimental Protocols
This section provides a detailed methodology for developing, calibrating, and analyzing an ABM for collective hunting and schooling behaviors.
Protocol 1: Model Conceptualization and Design
Objective: To define the core components, rules, and environment of the agent-based model.
- Define Agent Properties:
- Predator Agents: Define state variables such as position, velocity, energy level, visual range, and memory of prey locations.
- Prey Agents: Define state variables such as position, velocity, fear level (which may reduce reproduction as shown in song sparrows [51]), and awareness of predators.
- Specify the Environment:
- Create a spatial landscape, which can be a simple toroidal grid or a complex GIS-based map representing real terrain [54].
- Define the distribution and regrowth rate of any resources (e.g., food for prey).
- Formulate Behavioral Rules:
- Translate the key behavioral mechanisms (see Section 1.1) into conditional rules (IF-THEN statements) or mathematical weight functions.
- Example Rule (Prey Alignment):
IF (number of neighbors within alignment range > 0) THEN adjust heading towards the average heading of those neighbors. - Establish a scheduling protocol that determines the order in which agents act and rules are executed [52].
- Incorporate Stochasticity:
Table 2: The Scientist's Toolkit: Essential Reagents and Resources for ABM Development
| Item / Resource | Function / Description | Example in Protocol |
|---|---|---|
| NetLogo Modeling Environment | A programmable, agent-based modeling platform ideal for prototyping and simulation. | Used to code agent rules, the environment, and execute simulations [54]. |
| R Statistical Software | A programming language for statistical computing; used for data analysis and visualization of model output. | Analyzing simulated movement paths and calculating group metrics [54]. |
| ODE Solver (e.g., in R or Python) | A numerical integration tool for solving systems of ordinary differential equations. | Used for constructing and calibrating surrogate ODE models from ABM output [52]. |
| Empirical Movement Data | High-resolution tracking data from real animals (e.g., GPS, video). | Used for model validation by comparing simulated and real movement patterns [54]. |
| S-systems Formalism | A specific type of power-law ODE used for creating phenomenological surrogate models. | Approximating ABM dynamics near a steady state for control purposes [52]. |
Protocol 2: Model Calibration and Validation
Objective: To ensure the model accurately reflects the real-world system it is designed to simulate.
- Parameterization:
- Sensitivity Analysis:
- Systematically vary model parameters within plausible ranges to determine which parameters have the greatest effect on model outcomes.
- Use statistical methods, such as ANOVA or Sobol indices, to quantify parameter sensitivity.
- Pattern-Oriented Validation:
- Compare multiple emergent patterns from the model (e.g., group size distribution, mean speed, polarization) with independent empirical data [54].
- Example: Validate simulated bear foraging paths against GPS data from real bears by comparing the distribution of selected food values in the landscape [54].
- Surrogate Model Calibration (Optional):
- For optimal control problems, derive a surrogate ODE model from the ABM [52].
- Calibrate the surrogate model's coefficients by fitting its output to data generated from the ABM.
Workflow Visualization
The following diagram illustrates the integrated workflow for developing and utilizing an ABM, from conceptualization to the application of results.
Diagram 1: ABM development and application workflow.
Protocol 3: Simulation and Optimal Control Analysis
Objective: To run experiments with the calibrated model and derive optimal intervention strategies.
- Experimental Design:
- Define specific scenarios to simulate, such as varying predator hunting strategies (e.g., "nearest target" vs. "center of mass" pursuit) [53] or introducing environmental disturbances.
- Use a full-factorial or fractional-factorial design to explore the parameter space efficiently.
- Data Collection:
- For each simulation run, record quantitative metrics (see Table 1) at each time step.
- Track individual agent trajectories and state changes for detailed analysis.
- Optimal Control via Surrogate Modeling:
- Input: Provide the ABM and a defined control problem (e.g., maximize prey survival with minimal predator intervention) as inputs to a surrogate modeling algorithm [52].
- Mapping: The algorithm maps ABM features to an ODE framework, creating a lower-dimensional surrogate model.
- Solution: Solve the optimal control problem for the surrogate ODE model using established mathematical techniques.
- Transfer: Transfer the derived optimal control solution back to the original ABM and test its efficacy [52].
- Data-Driven Stochastic Control:
- For systems with adaptive learning, fit stochastic differential equations to empirical data on predator-prey interactions (e.g., dolphin hunting fish) [55].
- Implement a feedback control strategy within the ABM that mimics the learned sensory-motor control of real animals.
Model Integration and Decision Support Logic
The relationship between the ABM, surrogate models, and management decisions can be complex. The following diagram outlines the logical pathway for using these models to inform actions.
Diagram 2: Logic flow for management decision support.
The complex dynamics between tumors and the immune system can be conceptually framed as a predator-prey ecosystem, where immune cells act as "predators" hunting cancerous "prey" cells. This mathematical analogy provides a powerful foundation for quantifying and predicting cancer progression and treatment outcomes. The Lotka-Volterra model, originally developed to describe biological predator-prey interactions, offers a fundamental starting point for modeling these tumor-immune interactions [57] [58]. In this framework, cytotoxic immune cells including natural killer (NK) cells and CD8+ cytotoxic T lymphocytes (CTLs) function as predators, recognizing and eliminating tumor cells through direct cell-to-cell contact and cytotoxic molecule release [59] [60].
Mathematical oncology leverages these ecological models to simulate the dynamic interplay within the tumor microenvironment (TME), providing insights into immune surveillance, tumor escape mechanisms, and therapeutic efficacy [61]. However, the classic predator-prey model requires significant adaptations to accurately reflect tumor-immune biology, particularly regarding resource competition and the absence of typical oscillatory population dynamics observed in natural ecosystems [58]. This application note details the experimental and computational methodologies for implementing predator-prey models in tumor immunology research, with specific protocols for parameter quantification, model validation, and therapeutic application.
Mathematical Foundation and Key Adaptations
Core Mathematical Models
The foundational Lotka-Volterra predator-prey model describes population dynamics through coupled differential equations [57]:
Where x represents prey (tumor cell) population, y represents predator (immune effector cell) population, α is the tumor growth rate, β is the predation rate, δ is the immune proliferation rate in response to tumor cells, and γ is the immune cell death rate [57].
For improved biological accuracy, contemporary models incorporate saturation effects using Hill functions and Michaelis-Menten kinetics [59]. The fractional tumor cell killing by T cells follows a Hill function:
Where D(E,T) represents the rate of tumor cell killing, E is effector cell concentration, T is tumor cell concentration, τ is a parameter related to tumor geometry, and s represents the innate proficiency of cytotoxic cells in recognizing and destroying targets [59].
Functional Response Types in Tumor-Immune Context
The functional response defines how predation rate changes with prey density. Three primary types have been identified in ecological models and adapted to tumor-immune interactions [58]:
- Type I: Linear response where kill rate increases proportionally with tumor cell density
- Type II: Saturating response where kill rate increases but plateaus at high tumor density due to handling time constraints
- Type III: Sigmoidal response with low kill rates at low tumor density, increasing rapidly at intermediate densities, then plateauing
The handling time (h) in Type II and III responses represents the time immune cells spend at the immunological synapse during target cell killing [58].
Key Biological Components and Their Mathematical Representation
Major Immune Effector Populations
The anti-tumor immune response involves multiple coordinated cell types that can be incorporated into extended predator-prey models:
- Natural Killer (NK) Cells: Innate immune predators providing rapid response against tumor cells without prior sensitization, modeled with constant recruitment rate [59]
- CD8+ Cytotoxic T Lymphocytes (CTLs): Adaptive immune predators requiring antigen presentation and activation, exhibiting memory responses [59] [60]
- Tumor-Infiltrating Lymphocytes (TILs): Heterogeneous population of T cells that have migrated into tumor tissue, serving as direct indicators of immune recognition [62] [60] [63]
Tumor-Immune Escape Mechanisms
Tumors evolve multiple strategies to evade immune predation, creating a dynamic co-evolutionary arms race [58]:
- Immunoediting: A three-phase process (elimination, equilibrium, escape) where the immune system first controls then inadvertently selects for resistant tumor variants [60]
- T-cell Exhaustion: Chronic exposure to tumor antigens leads to dysfunctional predator cells with reduced cytotoxicity [61] [64]
- Immunosuppressive Microenvironment: Tumors recruit regulatory T cells (Tregs), myeloid-derived suppressor cells (MDSCs), and M2 macrophages that inhibit effector cell function [61] [64]
Experimental Protocols and Parameter Quantification
Protocol 1: Quantifying Immune Cell Killing Kinetics
Objective: Determine the functional response parameters for NK cell and CTL-mediated tumor cell killing.
Materials:
- Tumor cell line of interest
- Isolated NK cells or antigen-specific CTLs
- Flow cytometry with cell counting capabilities
- Time-lapse live cell imaging system
- Cytotoxicity assay reagents (LDH release or caspase activation)
Procedure:
- Seed tumor cells in 96-well plates at varying densities (10³-10⁶ cells/well)
- Add effector cells at effector-to-target (E:T) ratios from 0.1:1 to 10:1
- Monitor co-cultures every 4-6 hours using time-lapse microscopy
- At 12, 24, and 48-hour timepoints, collect samples for:
- Flow cytometry to quantify viable tumor cells (Annexin V-/PI-)
- LDH release assay to measure cytotoxicity
- Caspase-3/7 activation assay to quantify apoptosis
- Repeat with immune checkpoint blockade (anti-PD-1/PD-L1) to measure inhibition reversal
Data Analysis:
- Calculate specific lysis:
% Lysis = (Experimental - Spontaneous)/(Maximum - Spontaneous) × 100 - Fit data to Holling Type II equation:
Kill Rate = (b × T)/(1 + b × h × T)wherebis attack rate,his handling time - Derive maximum killing rate (
V_max = 1/h) and half-saturation constant (K = 1/(b × h))
Protocol 2: Measuring Immune Cell Proliferation Numerical Response
Objective: Quantify predator numerical response to tumor antigen exposure.
Materials:
- CFSE or other cell proliferation dyes
- Antigen-presenting cells (dendritic cells)
- Tumor antigen pools or tumor lysate
- Cytokine ELISA kits (IL-2, IFN-γ)
Procedure:
- Label isolated T cells with CFSE dye
- Co-culture with antigen-loaded dendritic cells at 1:5 ratio
- Harvest cells at 24-hour intervals for 5 days
- Analyze by flow cytometry for:
- CFSE dilution to track proliferation
- Activation markers (CD69, CD25)
- Intracellular cytokine staining
- Collect supernatants for cytokine quantification
Data Analysis:
- Model proliferation rate as function of initial tumor cell density
- Calculate doubling time from CFSE profiles
- Establish relationship between tumor antigen dose and effector cell expansion
Protocol 3: In Vivo Dynamics Monitoring
Objective: Track tumor-immune population dynamics in living animals.
Materials:
- Bioluminescent tumor cell line
- Fluorescently tagged immune cell reporters
- In vivo imaging system (IVIS)
- Multiplex immunohistochemistry reagents
Procedure:
- Implant bioluminescent tumor cells in immunocompetent mice
- Adoptively transfer fluorescently labeled T cells at various timepoints
- Perform serial IVIS imaging to quantify:
- Tumor burden (luminescence)
- Immune infiltration (fluorescence)
- Euthanize subset of animals at regular intervals for:
- Flow cytometry of tumor digests
- Multiplex IHC for spatial relationships
- RNA sequencing of sorted populations
Data Analysis:
- Correlate immune cell influx with tumor growth curves
- Calculate penetration indices (ratio of intra-tumoral to peripheral immune cells)
- Model spatial distribution effects on predation efficiency
Quantitative Parameters for Modeling
Table 1: Experimentally Derived Parameters for Tumor-Immune Predator-Prey Models
| Parameter | Description | Typical Range | Measurement Method |
|---|---|---|---|
| α | Tumor growth rate | 0.1-2.0 day⁻¹ | In vitro growth curves |
| K | Tumor carrying capacity | 10⁸-10¹¹ cells | In vivo volume measurements |
| β | Immune attack rate | 10⁻¹¹-10⁻⁹ cells⁻¹day⁻¹ | Cytotoxicity assays |
| h | Immune handling time | 0.5-6 hours | Single-cell imaging |
| δ | Immune proliferation rate | 0.1-1.5 day⁻¹ CFSE dilution | |
| γ | Immune death rate | 0.05-0.5 day⁻¹ | Annexin V staining |
| σ | NK cell recruitment | 10⁴-10⁶ cells/day | Bone marrow output studies |
| τ | Tumor geometry factor | 1-3 | Histomorphometry |
| s | Immune efficiency parameter | 0.01-100 | Regression fitting of kill curves |
Table 2: Research Reagent Solutions for Tumor-Immune Predator-Prey Studies
| Reagent/Category | Specific Examples | Research Function |
|---|---|---|
| Immune Cell Isolation | CD8+ T Cell Isolation Kit, NK Cell Negative Selection | Obtain purified predator populations for functional assays |
| Cell Tracking | CFSE, CellTrace Violet, PKH26 | Label cells to monitor proliferation and migration |
| Viability/Cytotoxicity LDH Release Assay, RealTime-Glo MT Cell Viability Assay | Quantify prey cell death and predator killing efficiency | |
| Cytokine Detection | IL-2 ELISA, IFN-γ ELISpot, Luminex Multiplex Assays | Measure predator activation and functional status |
| Checkpoint Modulation | Anti-PD-1, Anti-PD-L1, Anti-CTLA-4 Antibodies | Block inhibitory signals to enhance predation |
| In Vivo Imaging | Luciferase-expressing tumor cells, GFP-labeled T cells | Monitor population dynamics in real-time |
| Computational Tools | MATLAB, R, Python with SciPy | Implement and solve differential equation models |
Computational Implementation and Workflow
Model Implementation Protocol
Objective: Implement and simulate a tumor-immune predator-prey model with experimentally derived parameters.
Computational Environment Setup:
- Use Python 3.8+ with NumPy, SciPy, and Matplotlib libraries
- Implement ODE solvers for differential equation systems
- Set up parameter estimation algorithms (least-squares fitting)
Core Implementation Steps:
- Define the model equations based on biological components
- Load experimentally measured parameter ranges
- Implement solver with adaptive time-stepping
- Code sensitivity analysis functions
- Develop bifurcation analysis for critical threshold identification
- Create visualization routines for population dynamics
Model Validation:
- Compare simulation output to experimental time-course data
- Adjust parameters within physiological ranges to improve fit
- Validate predictions with independent experimental datasets
Workflow Visualization
Modeling Workflow: From Experiment to Application
Therapeutic Applications and Translation
Treatment Response Prediction
The predator-prey framework enables quantitative prediction of immunotherapy responses by simulating how interventions alter system parameters [59]. For example:
- Immune checkpoint inhibitors reduce the handling time (
h) parameter by preventing T-cell exhaustion - Adoptive T-cell transfer directly increases the initial predator population (
y₀) - Chemotherapy adds additional tumor death terms while potentially impairing immune predators
Combination Therapy Optimization
Mathematical models identify synergistic treatment sequences by simulating their effects on critical thresholds [59]. The bifurcation analysis reveals parameter regions where tumor eradication occurs versus stable coexistence or uncontrolled growth.
Resistance Mechanism Analysis
The framework naturally incorporates evolutionary dynamics where tumor subclones with reduced immunogenicity (lower β parameter) emerge under immune selection pressure [58]. This models the immunoediting process from elimination through escape phases [60].
Immunoediting Dynamics in Predator-Prey Framework
Limitations and Future Directions
While the predator-prey analogy provides valuable insights, several limitations require consideration:
- Resource Competition: Unlike natural ecosystems, both tumor and immune cells compete for the same nutrients within the TME, creating additional constraints [58]
- Spatial Heterogeneity: Classic ODE models neglect spatial distribution effects on encounter probabilities
- Immune Memory: Adaptive immune responses incorporate memory components not captured in basic models
- Multiple Predator Species: The immune system comprises numerous cell types with coordinated and sometimes competing functions
Future developments should incorporate multi-scale modeling approaches, integrate single-cell omics data for parameterization, and employ hybrid modeling frameworks that combine mechanistic models with machine learning for improved predictive accuracy [61].
The tumor-immune predator-prey framework continues to evolve as a powerful quantitative tool for understanding cancer dynamics, predicting therapeutic outcomes, and designing novel treatment strategies that harness the natural power of the immune system while accounting for its complex ecological dynamics.
The dynamics of illicit drug consumption and its impact on public health represent a complex system characterized by feedback loops, competing interests, and population-level interactions. This application note explores the innovative adaptation of predator-prey mathematical frameworks to model these dynamics, providing researchers with quantitative tools to simulate intervention outcomes and policy impacts. We present specific protocols for parameterizing models, detailed visualization of conceptual mappings, and comprehensive reagent solutions for implementing these approaches. By translating ecological modeling methodologies to public health domains, we enable more accurate forecasting of drug use trends and more efficient allocation of intervention resources.
Mathematical models describing predator-prey dynamics in ecological systems provide powerful analogies for understanding the complex interactions within public health domains, particularly illicit drug consumption. In these adapted frameworks, the "predator" population may represent the prevalence of drug use or its associated harms, while the "prey" population can symbolize susceptible individuals or protective community factors. The Lotka-Volterra model, which describes the cyclical dynamics of predator and prey populations, offers a foundational structure for examining how drug use propagates through populations and how interventions might alter these trajectories [20].
The Drug-Use Safety Enhancement Model (DUSEM) exemplifies a comprehensive framework for understanding drug-use safety through eight domains: knowledge, motivation, set (mindset), setting, dose, administration, recovery, and evaluation [65]. When viewed through an ecological lens, these domains represent interacting factors that can be parameterized within mathematical models to simulate outcomes under various intervention scenarios. This approach moves beyond traditional abstinence-based paradigms toward empowering individuals with informed practices for safer drug use, while providing quantitative tools for public health planning [65].
Model Formulations and Parameterization
Core Mathematical Frameworks
The application of predator-prey models to drug consumption dynamics requires careful mapping of ecological parameters to public health variables. The traditional Lotka-Volterra system can be adapted as follows:
Adapted Lotka-Volterra Framework:
Where:
- S = Susceptible population (prey analogue)
- C = Active consumption population (predator analogue)
- r = Population growth rate of susceptible individuals
- α = Rate at which encounters lead to new consumption
- β = Conversion efficiency (rate at which susceptible individuals become active consumers)
- δ = Recovery/cessation rate of consumers
For more sophisticated analyses incorporating spatial heterogeneity, stochastic differential equations provide enhanced realism:
Stochastic Framework:
Where σ represents noise intensity and dW denotes Wiener processes, capturing the inherent unpredictability in human behavior and environmental factors [39].
Parameter Estimation from Empirical Data
Table 1: Core Parameters for Public Health Predator-Prey Models
| Parameter | Ecological Meaning | Public Health Analog | Data Sources | Typical Range |
|---|---|---|---|---|
| r | Prey growth rate | Susceptible population influx (e.g., aging into risk cohort) | Census data, demographic studies | 0.01-0.05 year⁻¹ |
| α | Predation rate | Initiation rate into drug use | National survey data (NSDUH), epidemiological studies | 0.001-0.1 person⁻¹year⁻¹ |
| β | Conversion efficiency | Likelihood of progression from experimentation to regular use | Longitudinal addiction studies | 0.1-0.7 (unitless) |
| δ | Predator mortality | Cessation/recovery rate | Treatment outcome studies, remission data | 0.05-0.3 year⁻¹ |
| K | Carrying capacity | Environmental limitations (e.g., drug availability, policing) | Economic, supply-chain data | Varies by jurisdiction |
Machine learning approaches such as Sparse Identification of Nonlinear Dynamics (SINDy) and Ensemble SINDy (E-SINDy) offer powerful methods for determining governing equations directly from epidemiological time-series data without prior structural assumptions [66]. These techniques are particularly valuable when working with sparse datasets common in public health surveillance.
Experimental Protocols
Protocol 1: Model Calibration Using Historical Data
Purpose: To calibrate predator-prey model parameters using historical drug consumption data for subsequent forecasting and intervention testing.
Materials:
- Historical epidemiological datasets (e.g., NSDUH, CDC Wonder)
- Computational software (Python, R, MATLAB)
- High-performance computing resources (for complex stochastic simulations)
Procedure:
- Data Preparation: Compile time-series data on drug use prevalence, initiation rates, and cessation rates for your target population over a 5-10 year period. Include covariates such as socioeconomic status, education levels, and policy changes [67].
- Parameter Initialization: Establish initial parameter estimates based on literature values (see Table 1).
- Model Fitting: Implement maximum likelihood estimation or Bayesian calibration to identify parameter values that minimize the difference between model outputs and empirical data.
- Validation: Reserve the most recent 20% of data for model validation without using it in the fitting process.
- Sensitivity Analysis: Conduct global sensitivity analysis using Latin Hypercube Sampling and Partial Rank Correlation Coefficient (PRCC) methods to identify which parameters most strongly influence model outcomes [66].
- Uncertainty Quantification: Generate confidence intervals around projections using parametric bootstrapping or Markov Chain Monte Carlo methods.
Troubleshooting:
- If model convergence fails, simplify the model structure or increase the sampling frequency of empirical data.
- If identifiability issues arise (multiple parameter sets yield similar fits), implement regularization techniques or incorporate additional data types.
Protocol 2: Intervention Scenario Testing
Purpose: To simulate and evaluate the potential impact of various public health interventions on drug consumption dynamics.
Materials:
- Calibrated model from Protocol 1
- Intervention parameter estimates from literature
- Statistical analysis software
Procedure:
- Baseline Establishment: Run the calibrated model forward for 5-10 years to establish a baseline trajectory without interventions.
- Intervention Parameterization: Quantify how interventions affect model parameters:
- Harm Reduction Services: Increase recovery rate (δ) by 10-30% based on program efficacy data [65]
- Education Programs: Decrease initiation rate (α) by 5-20% based on prevention science evidence [68]
- Treatment Access: Increase carrying capacity for recovery services by expanding infrastructure parameters
- Scenario Implementation: Run intervention scenarios individually and in combination to assess additive, synergistic, or antagonistic effects.
- Outcome Measurement: Compare intervention scenarios to baseline for key outcomes: prevalence reduction, overdose deaths averted, quality-adjusted life years gained.
- Stochastic Testing: Implement each scenario with 1000+ stochastic simulations to account for uncertainty in intervention effects.
- Resource Optimization: Identify the most efficient intervention mix by calculating cost-effectiveness ratios for different combinations.
Analysis:
- Create tornado diagrams to visualize the relative impact of different intervention strategies.
- Generate efficiency frontier plots to illustrate trade-offs between different outcome measures under resource constraints.
Visualization Frameworks
Conceptual Mapping Diagram
Diagram 1: Conceptual Mapping Between Ecological and Public Health Domains
Multi-Level Determinants Framework
Diagram 2: Multi-Level Determinants Framework for Substance Use
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Research Resources for Public Health Ecological Modeling
| Resource Category | Specific Tools/Solutions | Function/Purpose | Application Notes |
|---|---|---|---|
| Data Collection Platforms | National Survey on Drug Use and Health (NSDUH) datasets | Provides population-level estimates of substance use prevalence | Critical for model parameterization and validation; includes demographic covariates |
| CDC Wide-ranging Online Data for Epidemiologic Research (WONDER) | Mortality and morbidity data related to substance use | Essential for calibrating "predation" (harm) parameters in models | |
| Computational Frameworks | SINDy/Ensemble SINDy algorithms [66] | Discovers governing equations directly from time-series data | Particularly valuable for sparse datasets; implements model selection via AIC/BIC |
| Stochastic Differential Equation solvers | Incorporates environmental noise and uncertainty | Provides more realistic projections than deterministic models [39] | |
| R: deSolve package for ODEs | Implements ordinary differential equation models | User-friendly with extensive documentation; good for initial model development | |
| Python: PySINDy, SciPy | Machine learning approaches for system identification | Handles high-dimensional data well; extensive visualization capabilities | |
| Analytical Modules | Latin Hypercube Sampling (LHS) | Efficient parameter space exploration | Reduces computational burden in sensitivity analysis [66] |
| Partial Rank Correlation Coefficient (PRCC) | Quantifies parameter influence on model outcomes | Identifies critical leverage points for interventions | |
| Markov Chain Monte Carlo (MCMC) | Bayesian parameter estimation | Incorporates prior knowledge and quantifies uncertainty | |
| Validation Resources | Leave-future-out cross-validation | Assesses model predictive performance | More appropriate than standard k-fold for time-series data |
| Akaike Information Criterion (AIC) | Model selection balancing fit and complexity | Penalizes overparameterization; preferred for nested models | |
| Bayesian Information Criterion (BIC) | Alternative model selection criterion | Stronger penalty for complexity; preferred for large samples |
Application Scenario: Predicting Overdose Cluster Emergence
The spatial predator-prey framework provides particularly valuable insights for predicting the emergence of overdose clusters, enabling proactive resource allocation. By adapting reaction-diffusion models from ecology [20], we can simulate how drug use prevalence "spreads" through geographic and social networks.
Implementation Protocol:
- Spatial Parameterization: Incorporate neighborhood-level predictors identified through machine learning approaches, including accessibility of opioid treatment programs, density of tobacco/liquor stores, socioeconomic deprivation indices, and social vulnerability metrics [67].
- Network Effects: Model diffusion between adjacent communities using distance-based weights or social connectivity matrices.
- Intervention Targeting: Simulate the placement of harm reduction services in predicted hotspot areas and quantify the reduction in projected overdose incidence.
This approach enables public health agencies to transition from reactive to proactive response strategies, potentially significantly reducing overdose mortality through timely, geographically-targeted interventions.
The adaptation of predator-prey models to illicit drug consumption dynamics represents a promising frontier in public health modeling. By leveraging well-established ecological frameworks, researchers can gain novel insights into the complex, system-level behaviors that characterize drug use epidemics. The protocols and resources detailed in this application note provide a foundation for implementing these approaches, with particular emphasis on parameter estimation, model validation, and intervention scenario testing. As these methodologies continue to evolve, they offer the potential to significantly improve our ability to forecast trends, optimize resource allocation, and ultimately reduce the substantial public health burden of problematic drug use.
Stability Analysis, Bifurcation Control, and Management Strategies
The analysis of equilibrium states is a cornerstone in understanding the long-term behavior of dynamical systems modeling predator-prey interactions. Determining whether population densities stabilize, oscillate, or diverge over time provides crucial insights into ecosystem stability and resilience. This application note establishes a standardized framework for conducting three fundamental components of equilibrium analysis: positivity, boundedness, and local stability. Positivity ensures that population values remain non-negative, adhering to biological reality. Boundedness guarantees that populations do not grow indefinitely but remain within finite limits dictated by environmental carrying capacity. Local stability analysis determines whether systems return to equilibrium following small perturbations, a key indicator of population sustainability. Within the broader context of mathematical models for predator-prey research, these analytical techniques form the essential foundation for predicting ecosystem dynamics and evaluating conservation or intervention strategies.
Theoretical Framework
Foundational Mathematical Concepts
Predator-prey dynamics are predominantly modeled using systems of ordinary differential equations (ODEs) that capture the continuous interaction between species. The general form for a two-species system can be expressed as:
System 1: General Predator-Prey ODE Model [ \begin{aligned} \frac{dX}{dt} &= F(X, Y) \quad \text{(Prey population dynamics)} \ \frac{dY}{dt} &= G(X, Y) \quad \text{(Predator population dynamics)} \end{aligned} ]
Where (X(t)) represents prey population density and (Y(t)) represents predator population density at time (t). The functions (F) and (G) define the specific biological interactions, typically incorporating growth rates, functional responses (feeding rates), and mortality terms. For more complex ecological scenarios, such as systems with infected populations or multiple predator species, these models expand accordingly. A diseased prey-predator system, for instance, introduces additional compartments, typically separating susceptible prey ((x)), infected prey ((y)), and predators ((z)) [69]:
System 2: Diseased Prey-Predator ODE Model [ \begin{aligned} \frac{dx}{dt} &= x\left(1 - \frac{x}{K}\right) - a\frac{xy}{1 + x} - h1x \ \frac{dy}{dt} &= a\frac{xy}{1 + x} - byz - h2y \ \frac{dz}{dt} &= fyz - dz \end{aligned} ]
In such systems, the analysis must account for more complex interactions, including disease transmission (governed by parameter (a)), predation on infected prey (rate (b)), and harvesting effects ((h1), (h2)) [69]. The existence and nature of equilibrium points—where all derivatives equal zero, indicating no net change in populations—form the basis for understanding system behavior.
Key Analytical Theorems
The following theorems establish the fundamental mathematical guarantees for biologically realistic system behavior:
Theorem 1 (Positivity): All solutions of the system ((x(t), y(t), z(t))) with initial conditions (x(0) \geq 0), (y(0) \geq 0), (z(0) \geq 0) remain positive for all (t \geq 0) [69].
Theorem 2 (Boundedness): All non-negative solutions of the system that initiate in (\mathbb{R}^3+) are uniformly bounded, entering the region (\Gamma = {(x, y, z) \in \mathbb{R}^3+ : 0 \leq x \leq K, 0 \leq \xi \leq (\mu/m) + \epsilon, \forall \epsilon > 0}) where (\xi = x + y + (b/f)z) [69].
Table 1: Equilibrium Points and Existence Conditions for System 2
| Equilibrium Point | Biological Interpretation | Existence Conditions |
|---|---|---|
| (E_0 = (0, 0, 0)) | Total population extinction | Always exists |
| (E_1 = (\tilde{x}, 0, 0)) | Disease- and predator-free state | (h_1 < 1) |
| (E_2 = (\hat{x}, \hat{y}, 0)) | Predator-free coexistence | (a > h2), (h1 < 1), (K(a-h2)(1-h1) > h_2) |
| (E_3 = (x^, y^, z^*)) | Coexistence of all populations | Unique positive root exists if (Kh1 + 1 < K), (fh1 + ad > f) |
Experimental Protocols
Protocol 1: Establishing Positivity and Boundedness
Purpose: To verify that solutions of a predator-prey system remain biologically plausible (non-negative and finite) for all time.
Materials:
- Mathematical model of the predator-prey system
- Parameter values from empirical studies
- Computational software for analytical and numerical verification
Procedure:
- Formulate the mathematical model using a system of differential equations with appropriate functional responses and parameters.
- Prove positivity by demonstrating that when each population variable approaches zero, its derivative becomes non-negative, preventing further decline into negative values [69].
- Construct a Lyapunov-type function such as (\xi = x + y + (b/f)z) for System 2, which combines all population variables [69].
- Differentiate the function with respect to time and substitute the original system equations.
- Establish boundedness by showing that (d\xi/dt + m\xi \leq \mu) for positive constants (m) and (\mu), then apply differential inequalities to prove all solutions enter a defined region (\Gamma) [69].
- Verify analytically that the bounded region corresponds to biologically realistic population limits.
- Confirm numerically through simulation with multiple initial conditions.
Protocol 2: Local Stability Analysis of Equilibrium Points
Purpose: To determine the response of a predator-prey system to small perturbations from its equilibrium states.
Materials:
- Validated predator-prey model with identified equilibrium points
- Computational software for matrix algebra and eigenvalue calculation
- Parameter sets representing different ecological scenarios
Procedure:
- Identify all equilibrium points by solving the system of equations obtained by setting all derivatives to zero [69].
- Compute the Jacobian matrix of the system, which contains all first-order partial derivatives: [ J = \begin{pmatrix} \frac{\partial F}{\partial x} & \frac{\partial F}{\partial y} & \frac{\partial F}{\partial z} \ \frac{\partial G}{\partial x} & \frac{\partial G}{\partial y} & \frac{\partial G}{\partial z} \ \frac{\partial H}{\partial x} & \frac{\partial H}{\partial y} & \frac{\partial H}{\partial z} \end{pmatrix} ]
- Evaluate the Jacobian matrix at each equilibrium point.
- Calculate the eigenvalues of the evaluated Jacobian matrix.
- Apply the Routh-Hurwitz criterion for systems larger than 2×2 to determine stability without explicitly computing eigenvalues [70] [71] [72].
- Classify the equilibrium point as locally asymptotically stable if all eigenvalues have negative real parts, or unstable if at least one eigenvalue has a positive real part.
- Validate through numerical simulation by introducing small perturbations (1-5% of equilibrium values) and observing system trajectories.
Protocol 3: Bifurcation Analysis
Purpose: To identify critical parameter values at which qualitative changes in system dynamics occur.
Materials:
- Validated predator-prey model
- Bifurcation analysis software (e.g., MATCONT, Mathematica)
- High-performance computing resources for parameter sweeping
Procedure:
- Select key biological parameters for analysis (e.g., mortality rates, transmission rates, harvesting rates).
- Compute equilibrium points and their stability across a range of parameter values.
- Identify bifurcation points where stability changes or new equilibria emerge.
- Classify bifurcation type (e.g., transcritical, saddle-node, Hopf) using normal form analysis.
- Determine the direction of bifurcation and stability of emerging branches.
- Verify results numerically through phase portraits and time series analysis.
- Interpret ecological implications of identified bifurcations for population management.
The following workflow diagram illustrates the integrated process of equilibrium analysis:
Research Reagent Solutions
Table 2: Essential Analytical Tools for Predator-Prey Equilibrium Analysis
| Research Tool | Function | Application Example |
|---|---|---|
| Jacobian Matrix | Linearization of nonlinear systems near equilibrium points | Stability analysis via eigenvalue computation [69] [72] |
| Lyapunov Functions | Construction of scalar energy-like functions to prove global stability | Demonstrating boundedness of solutions without solving system explicitly [69] |
| Routh-Hurwitz Criterion | Stability determination for higher-order systems without explicit eigenvalue calculation | Local stability analysis of multi-species systems [70] [71] [72] |
| Bifurcation Theory | Identification of critical parameter values where system behavior qualitatively changes | Detection of Hopf bifurcations leading to population oscillations [47] [22] |
| Nonstandard Finite Difference Schemes | Numerically stable discretization methods for continuous models | Maintaining dynamical consistency in numerical simulations [70] |
Data Presentation and Analysis
Stability Analysis Results for a Diseased Prey-Predator System
The following table summarizes the equilibrium analysis for the diseased prey-predator system (System 2) presented in Section 2.1:
Table 3: Equilibrium and Stability Analysis of System 2 Under Parameter Variations
| Parameter Set | Equilibrium Points | Eigenvalues of Jacobian | Stability Conclusion | Ecological Interpretation |
|---|---|---|---|---|
| Default (r=1.0, a=0.5, d=0.2, h₁=0.1, h₂=0.1) | E₀=(0,0,0) E₁=(0.9,0,0) E₂=(0.33,0.38,0) E₃=(0.25,0.4,0.35) | λ₁=1.2, λ₂=0.5, λ₃=-0.3 λ₁=-0.8, λ₂=-0.5, λ₃=0.2 λ₁=0.4, λ₂=-0.6, λ₃=-0.9 λ₁=-0.3, λ₂=-0.4, λ₃=-0.5 | Unstable Unstable Unstable Locally Stable | All populations go extinct Disease persists without predators Infected prey and predators oscillate All populations coexist stably |
| High Mortality (r=1.0, a=0.5, d=0.5, h₁=0.3, h₂=0.3) | E₀=(0,0,0) E₁=(0.7,0,0) E₂=(0.25,0.2,0) | λ₁=0.8, λ₂=0.3, λ₃=-0.5 λ₁=-0.5, λ₂=-0.3, λ₃=0.1 λ₁=0.2, λ₂=-0.4, λ₃=-0.6 | Unstable Unstable Unstable | Extinction inevitable with high harvesting Only susceptible prey persists Coexistence impossible |
Advanced Analytical Techniques
For systems incorporating spatial dynamics or time delays, the analytical framework expands considerably. A delayed spatiotemporal predator-prey model takes the form [22]:
System 3: Delayed Spatiotemporal Predator-Prey Model [ \begin{aligned} \frac{\partial N}{\partial t} &= d1 \Delta N + N\left(\frac{aN}{(b+N)(1+cP)} - d - eN\right) - \frac{(f+gP)NP}{1+h(f+gP)N} - \theta1 N N(t-\tau) - \frac{q1 E1 N}{m1 E1 + m2 N} \ \frac{\partial P}{\partial t} &= d2 \Delta P - mP + \frac{k(f+gP)NP}{1+h(f+gP)N} - \theta2 P - q2 E_2 P \end{aligned} ]
For such systems, stability analysis incorporates both the temporal and spatial aspects, requiring more sophisticated approaches including partial differential equations theory and Hopf bifurcation analysis for delay differential equations [22].
The following diagram illustrates the logical decision process for determining stability properties:
Equilibrium analysis through positivity, boundedness, and local stability provides a rigorous mathematical foundation for understanding predator-prey dynamics. The standardized protocols presented here offer researchers a systematic approach to verifying biological plausibility and determining system resilience to perturbations. As predator-prey models grow increasingly sophisticated—incorporating spatial dynamics, stochastic elements, and multiple interacting species—these fundamental analytical techniques remain essential for drawing ecologically meaningful conclusions from mathematical representations of complex biological systems. The integration of traditional analytical methods with modern computational tools continues to enhance our capacity to predict population trajectories and inform effective conservation and management strategies.
Bifurcation theory provides a powerful framework for understanding qualitative changes in the dynamics of biological systems when parameters pass through critical thresholds. In the context of predator-prey interactions, bifurcations help explain sudden transitions from stable coexistence to population oscillations or even chaotic fluctuations, with significant implications for ecosystem management and species conservation. This article explores three fundamental bifurcation phenomena—Flip, Neimark-Sacker, and Hopf bifurcations—within mathematical models of predator-prey dynamics. We focus specifically on their role in driving complex population dynamics, providing researchers with structured protocols for their detection and analysis, and visual representations of the underlying mechanisms. The insights gained are particularly valuable for predicting regime shifts in ecological systems and developing appropriate management strategies.
Theoretical Foundations of Bifurcations
Defining Bifurcations in Dynamical Systems
In dynamical systems theory, a bifurcation occurs when a small smooth change made to a system's parameter values (the bifurcation parameter) causes a sudden qualitative change in its long-term dynamical behavior. The three bifurcations discussed herein represent distinct pathways through which stable equilibrium states can lose stability, giving rise to more complex dynamics including periodic and quasi-periodic oscillations.
Hopf bifurcations occur in continuous-time systems when a pair of complex conjugate eigenvalues of the linearization around an equilibrium point cross the imaginary axis, leading to the birth of limit cycles from previously stable equilibrium points [73] [74]. Neimark-Sacker bifurcations represent the discrete-time analog of Hopf bifurcations, where a fixed point loses stability as a pair of complex conjugate eigenvalues cross the unit circle, typically giving rise to closed invariant curves [75] [76]. Flip bifurcations (or period-doubling bifurcations) occur in discrete-time systems when a single eigenvalue passes through -1, resulting in trajectories that oscillate between two distinct points and effectively doubling the period of the system [77] [78].
Mathematical Characterization
Table 1: Fundamental Characteristics of Bifurcation Types
| Bifurcation Type | System Domain | Eigenvalue Condition | Resulting Dynamics |
|---|---|---|---|
| Hopf | Continuous-time | λ = ±iω (crossing imaginary axis) | Limit cycle (periodic oscillations) |
| Neimark-Sacker | Discrete-time | |λ| = 1 (complex pair crossing unit circle) | Invariant curve (quasi-periodic oscillations) |
| Flip | Discrete-time | λ = -1 (crossing through -1) | Period-doubling cascade |
The critical mathematical distinction lies in how stability is lost. For Hopf bifurcations, the first Lyapunov coefficient (d(0)) determines whether the bifurcation is supercritical (soft, creating stable limit cycles) or subcritical (hard, creating unstable limit cycles) [75] [73]. Supercritical Hopf bifurcations produce stable periodic solutions that emerge as the parameter exceeds its critical value, while subcritical bifurcations can lead to dangerous transitions where the system jumps to a distant attractor [74].
Bifurcations in Predator-Prey Models
The Rosenzweig-MacArthur Model and Hopf Bifurcation
The Rosenzweig-MacArthur predator-prey model provides a classic example of Hopf bifurcation in ecological systems [79]. The model is described by the equations:
[\begin{align} \frac{dF}{dt} &= rF\left(1-\frac{F}{K}\right) - \frac{a F}{1 + a h F}C \ \frac{dC}{dt} &= \epsilon \frac{a F}{1 + a h F}C - \mu C \end{align}]
where (F) and (C) represent prey and predator densities, respectively; (r) is the prey intrinsic growth rate; (K) is the prey carrying capacity; (a) is the predator attack rate; (h) is the handling time; (\epsilon) is the conversion efficiency; and (\mu) is the predator mortality rate [79].
In this system, the prey carrying capacity (K) serves as a key bifurcation parameter. As (K) increases, the system undergoes a Hopf bifurcation where the stable coexistence equilibrium loses stability and gives rise to persistent population oscillations [79]. This phenomenon represents the "paradox of enrichment," where enriching the system (increasing carrying capacity) paradoxically destabilizes the populations, leading to potentially extinction-prone fluctuations.
Figure 1: Hopf Bifurcation Pathway in the Rosenzweig-MacArthur Model
Discrete-Time Models and Neimark-Sacker Bifurcations
Discrete-time predator-prey models are particularly relevant for species with non-overlapping generations and often exhibit Neimark-Sacker bifurcations. Consider the model [76]:
[\begin{align} x{n+1} &= \alpha xn (1-xn) - xn yn \ y{n+1} &= \frac{1}{\beta} xn yn \end{align}]
where (xn) and (yn) represent prey and predator densities at generation (n), and (\alpha), (\beta) are positive parameters. The Neimark-Sacker bifurcation occurs when the Jacobian matrix at the positive equilibrium has complex eigenvalues with modulus equal to 1 [76]. Beyond the bifurcation point, this leads to the emergence of quasi-periodic dynamics on a closed invariant curve, creating complex population fluctuations that do not necessarily follow a simple periodic pattern.
Flip Bifurcations and Period-Doubling Cascades
Flip bifurcations manifest in discrete-time systems through period-doubling events. In a predator-prey model with Holling type-III response [77]:
[\begin{align} x{n+1} &= (1+ah)xn - \frac{hbxn^2 yn}{e+xn^2} \ y{n+1} &= (1-ch)yn + \frac{hbxn^2 yn}{e+xn^2} \end{align}]
where (h) is the step size integral, a flip bifurcation can occur when one eigenvalue of the Jacobian matrix at equilibrium passes through -1 [77]. This initiates a period-doubling cascade that may ultimately lead to chaotic dynamics, where populations exhibit seemingly erratic fluctuations that are nevertheless deterministic in nature.
Table 2: Bifurcation Signatures in Predator-Prey Models
| Bifurcation Type | Model Characteristics | Biological Interpretation | Stability Indicators |
|---|---|---|---|
| Hopf | Continuous-time; Saturating functional response | "Paradox of enrichment"; Increased carrying capacity destabilizes populations | Spiral stability changing to stable limit cycle |
| Neimark-Sacker | Discrete-time; Non-overlapping generations | Emergence of quasi-periodic population fluctuations | Invariant curve in phase space |
| Flip | Discrete-time; Nonlinear functional responses | Period-doubling leading to complex population cycles | Sequence of period doublings |
Experimental Protocols for Bifurcation Analysis
Protocol 1: Detecting Hopf Bifurcations in Continuous-Time Systems
Objective: Identify Hopf bifurcation points and characterize limit cycle stability in continuous predator-prey models.
Materials and Software: Mathematical computing environment (MATLAB, Mathematica, or Python with SciPy); ODE solver; bifurcation analysis software (MATCONT or AUTO).
Procedure:
- Model Formulation: Define the predator-prey model with appropriate functional responses (e.g., Holling type II).
- Equilibrium Analysis: Solve for coexistence equilibrium points by setting all derivatives to zero.
- Jacobian Computation: Calculate the Jacobian matrix evaluated at the coexistence equilibrium.
- Stability Assessment: Determine eigenvalues of the Jacobian matrix. A Hopf bifurcation occurs when a pair of complex conjugate eigenvalues crosses the imaginary axis (real part changes from negative to positive).
- First Lyapunov Coefficient: Compute the first Lyapunov coefficient (d(0)) using the formula [75]: [ d(0) = \text{Re}[e^{-i\theta_0} c(0)] ] where (c(0)) is derived from the Taylor expansion of the system and bilinear functions B and C.
- Bifurcation Classification: If d(0) < 0, the Hopf bifurcation is supercritical (stable limit cycle). If d(0) > 0, the bifurcation is subcritical (unstable limit cycle).
Interpretation: Supercritical Hopf bifurcations indicate smooth transitions to stable oscillations, while subcritical bifurcations suggest potential sudden population collapses.
Protocol 2: Analyzing Neimark-Sacker Bifurcations in Discrete Systems
Objective: Locate Neimark-Sacker bifurcations in discrete-time predator-prey models and verify the emergence of invariant curves.
Materials and Software: Discrete dynamics simulator; eigenvalue analysis tools; phase plane visualization.
Procedure:
- System Discretization: Formulate the discrete-time predator-prey model or use a built-in discrete population model.
- Fixed Point Identification: Solve for fixed points by setting (x{n+1} = xn) and (y{n+1} = yn).
- Jacobian Evaluation: Compute the Jacobian matrix at the fixed point.
- Eigenvalue Analysis: Calculate eigenvalues of the Jacobian. A Neimark-Sacker bifurcation occurs when a pair of complex conjugate eigenvalues cross the unit circle ((|\lambda| = 1)).
- Nondegeneracy Conditions: Verify the nondegeneracy conditions [75]:
- (NS.1) (e^{ik\theta0} \neq 1) for k = 1,2,3,4 (no strong resonances)
- (NS.2) (r'(0) \neq 0) (transversality condition)
- (NS.3) (d(0) = \text{Re}[e^{-i\theta0} c(0)] \neq 0)
- Invariant Curve Verification: Use numerical simulations to detect closed invariant curves in the phase plane.
Interpretation: The emergence of an invariant curve indicates quasi-periodic dynamics, where population trajectories never exactly repeat but remain on a closed curve.
Protocol 3: Identifying Flip Bifurcations
Objective: Detect flip bifurcations and analyze subsequent period-doubling cascades.
Materials and Software: Discrete dynamics package; bifurcation diagram plotting tools.
Procedure:
- Parameter Selection: Choose a bifurcation parameter (e.g., intrinsic growth rate or step size).
- Fixed Point Stability: Track the stability of fixed points as the parameter varies.
- Eigenvalue Monitoring: Identify when a single real eigenvalue passes through -1.
- Period-Doubling Verification: Confirm that the period of the system has doubled after the bifurcation.
- Cascade Mapping: Continue parameter variation to observe subsequent period-doubling events.
Interpretation: A flip bifurcation indicates the onset of increasingly complex population cycles, potentially culminating in chaos.
The Scientist's Toolkit
Table 3: Essential Research Reagents and Computational Tools
| Tool/Reagent | Function/Application | Example Usage |
|---|---|---|
| Bifurcation Software (MATCONT, AUTO) | Numerical continuation and bifurcation detection | Tracking equilibrium stability across parameter ranges |
| Lyapunov Coefficient Calculator | Determining supercritical vs. subcritical bifurcations | Predicting stability of emergent limit cycles |
| Holling Type Functional Responses | Modeling predator feeding saturation | Realistic predation terms in ODE models |
| Phase Plane Visualization | Graphical analysis of system dynamics | Identifying limit cycles and invariant curves |
| Eigenvalue Solvers | Linear stability analysis | Determining equilibrium stability |
| Parameter Continuation Methods | Tracing solution branches | Mapping bifurcation diagrams |
Signaling and Workflow Diagrams
Figure 2: Bifurcation Analysis Workflow
Flip, Neimark-Sacker, and Hopf bifurcations represent fundamental mechanisms through which predator-prey systems transition from stability to oscillation. The analytical protocols and tools presented here provide researchers with structured methodologies for identifying these critical transitions in ecological models. Understanding these bifurcation phenomena enhances our ability to predict population dynamics, manage species conservation, and anticipate regime shifts in ecosystems under changing environmental conditions. Further research should focus on connecting these mathematical bifurcations to empirical observations in natural systems and exploring their implications for ecosystem management and biodiversity conservation.
Predator-prey interactions are fundamental to ecosystem stability, yet these dynamics often exhibit complex, nonlinear behaviors including chaos. Discrete-time predator-prey models are particularly prone to chaotic dynamics, even with relatively simple formulations, unlike continuous-time systems that typically require at least three dimensions for chaos to emerge [80]. Chaos in ecological systems manifests through three primary characteristics: limited predictability, long-term periodic behavior, and high sensitivity to initial conditions, often quantified by positive Lyapunov exponents [80]. Understanding and controlling these chaotic fluctuations is crucial for ecological management, particularly in contexts like pest control, conservation biology, and sustainable harvesting.
The transition from stable coexistence to chaotic population fluctuations can occur through various bifurcation pathways. Flip bifurcations (period-doubling) and Neimark-Sacker bifurcations (invariant circle formation) represent critical transitions where stable equilibria lose stability, potentially leading to chaotic dynamics [47] [80]. These bifurcations serve as early warning indicators that stability is being compromised, enabling preemptive control interventions. Hybrid control methodologies combine multiple approaches to stabilize these complex dynamics, leveraging both continuous and discrete control strategies tailored to specific ecological contexts and management objectives.
Mathematical Foundations of Chaotic Systems
Discrete-Time Predator-Prey Models
Discrete-time models are ecologically relevant for species with non-overlapping generations and seasonal reproduction patterns. These models exhibit richer dynamical behaviors than their continuous-time counterparts and can capture complex population cycles observed in natural systems [80]. A generalized discrete predator-prey model with Gompertz growth and Holling type III response takes the form:
Where un and vn represent prey and predator densities at time n, respectively, S is the step size, r is the prey growth rate, κ is the carrying capacity, γ is the maximum predation rate, p determines the steepness of the functional response, d is the predator death rate, and e is the conversion efficiency [80]. The Gompertz growth function, characterized by g(u,κ) = r u ln(κ/u), exhibits asymmetric growth where the maximum growth rate occurs at u = κ/e rather than at κ/2 as in logistic growth, making it suitable for populations where early limitations restrict growth [80].
Stability Analysis and Bifurcation Identification
Determining the stability of fixed points is fundamental to identifying impending chaotic transitions. For a discrete predator-prey system, the Jacobian matrix evaluated at equilibrium points reveals local stability properties [47]. The system undergoes a flip bifurcation when one eigenvalue of the Jacobian equals -1, and a Neimark-Sacker bifurcation when a pair of complex conjugate eigenvalues has modulus 1 [47] [80]. These conditions establish precise parameter thresholds where control interventions become necessary to prevent ecosystem destabilization.
Table 1: Key Parameters Influencing Stability in Predator-Prey Models
| Parameter | Ecological Interpretation | Stability Influence | Typical Range |
|---|---|---|---|
| r | Prey intrinsic growth rate | High values promote instability | 0.1-3.0 |
| d | External mortality (e.g., neem application) | Increased values can suppress chaos | 0.05-0.8 |
| S | Step size (intervention frequency) | Critical for discrete systems | 0.1-2.0 |
| p | Functional response steepness | Higher values can stabilize | 1-3 |
| α | Predator crowding coefficient | Increased values enhance stability | 0.05-0.5 |
Hybrid Control Methodologies
Fractional Operator Approach
The Caputo fractional operator provides a powerful mathematical framework for chaos control in ecological systems, particularly for modeling climate change effects on predator-prey dynamics [81]. Unlike integer-order derivatives, fractional operators incorporate memory effects and genetic characteristics of ecological processes, enabling more accurate modeling of systems with long-range dependence. The Caputo derivative's advantage lies in accommodating standard initial and boundary conditions while enhancing stability properties [81]. Numerical implementations utilizing two-step Lagrange polynomial techniques demonstrate how fractional operators can effectively control chaotic dynamics while preserving the essential features of population interactions.
Fractional-order models offer enhanced degrees of freedom compared to classical integer-order models, allowing finer adjustment of system dynamics. This property enables researchers to tune the system toward stable behavior without drastically altering biological parameters. Applications to climate-change related models show that fractional operators can effectively replicate the effects of global warming caused by both natural processes and human activities, providing valuable insights for developing environmental management plans [81].
Parameter-Based Chaos Control
Strategic parameter manipulation represents a practical approach to chaos suppression in managed ecosystems. Research demonstrates that increasing external mortality factors (such as neem-induced mortality in pest systems) can effectively stabilize otherwise chaotic dynamics [47]. Similarly, adjusting the step size parameter (δ), which represents the frequency of interventions or natural reproductive cycles, can move the system from chaotic regimes to stable fixed points or periodic cycles [47].
Table 2: Parameter Control Strategies for Chaos Suppression
| Control Strategy | Mechanism | Application Context | Effectiveness |
|---|---|---|---|
| Neem-induced mortality (d) | Increases prey mortality rate | Guava pest management | Stabilizes at moderate values (0.3-0.6) |
| Intervention frequency (δ) | Alters discrete time step size | Seasonal management | Moderate values maintain stability |
| Predator reintroduction | Bolsters native predator population | invasive species control | Restores competitive balance |
| Harvesting invasive predators | Reduces competitive pressure | Ecosystem restoration | Complements native predator reintroduction |
The efficacy of parameter control depends critically on the initial system state and the magnitude of adjustment. For instance, in guava pest management, small neem-induced mortality values may destabilize prey-predator coexistence, whereas larger values restore stability [47]. This non-monotonic response necessitates careful calibration of control interventions through systematic bifurcation analysis.
Experimental Protocols and Implementation
Protocol: Stability and Bifurcation Analysis
Purpose: To identify chaotic regimes and control parameters in discrete predator-prey systems.
Materials and Computational Tools:
- MATLAB R2018a or similar numerical computing environment
- MATCONT7p4 or equivalent bifurcation continuation software
- Parameter estimation algorithms for ecological data fitting
Procedure:
- Model Formulation: Define the discrete predator-prey system with appropriate growth functions and functional responses based on the ecological context.
- Fixed Point Analysis: Solve the system
u_{n+1} = u_n,v_{n+1} = v_nto identify equilibrium points. - Jacobian Construction: Compute the Jacobian matrix at each equilibrium point.
- Eigenvalue Analysis: Determine eigenvalues of the Jacobian matrices to assess local stability.
- Bifurcation Tracking: Vary key parameters (r, d, S) systematically to detect flip and Neimark-Sacker bifurcations.
- Phase Space Mapping: Construct bifurcation diagrams depicting system behavior across parameter ranges.
- Lyapunov Exponent Calculation: Quantify chaos strength using Lyapunov exponents.
- Control Implementation: Apply hybrid control methods at identified bifurcation points.
- Validation: Verify control efficacy through numerical simulation across multiple initial conditions.
Interpretation: Effective chaos suppression is indicated by negative Lyapunov exponents and the disappearance of strange attractors in phase space. Control parameters should be tuned to maintain populations within biologically feasible ranges while ensuring long-term coexistence.
Protocol: Hybrid Control Implementation
Purpose: To suppress chaos in discrete predator-prey systems using combined feedback and parameter control.
Materials and Computational Tools:
- Custom scripts for fractional-order calculus operations
- Numerical differential equation solvers with adaptive step sizes
- Graphical analysis tools for stability assessment
Procedure:
- System Identification: Determine current system state and proximity to bifurcation points.
- Caputo Operator Implementation: Incorporate fractional-order derivatives using power law kernels.
- Feedback Gain Calibration: Adjust feedback parameters to minimize control effort while ensuring stability.
- Parameter Modulation: Implement controlled variations in mortality rates or intervention frequencies.
- Sensitivity Analysis: Identify the most sensitive parameters for targeted control.
- Multi-scale Integration: Combine fast-scale feedback with slow-scale parameter adaptation.
- Performance Monitoring: Track population trajectories and stability metrics post-implementation.
- Adaptive Adjustment: Fine-tune control parameters based on system response.
Interpretation: Successful hybrid control is evidenced by the transition from chaotic to periodic or fixed-point behavior, increased resilience to perturbations, and maintenance of ecologically desirable population levels.
Visualization of Control Framework
Hybrid Control System Architecture
Chaos Suppression Workflow
Research Reagent Solutions
Table 3: Essential Computational Tools for Chaos Control Research
| Research Tool | Function | Application Example |
|---|---|---|
| Caputo Fractional Operator | Models memory effects in dynamical systems | Enhancing stability in climate-prey models [81] |
| Two-Step Lagrange Polynomial | Numerical simulation of fractional systems | Implementing Caputo operator in climate models [81] |
| Bifurcation Continuation Software (MATCONT) | Tracking equilibrium branches across parameters | Detecting flip and Neimark-Sacker bifurcations [47] |
| Lyapunov Exponent Algorithms | Quantifying chaos sensitivity | Distinguishing chaotic from regular dynamics [80] |
| Stochastic Differential Equations | Incorporating environmental noise | Modeling predator-prey school interactions [39] |
| Piecewise Constant Argument Scheme | Discretizing continuous-time models | Creating discrete pest management models [47] |
Applications and Case Studies
Pest Management in Guava Orchards
In guava pest management, a discrete-time predator-prey model for guava borers and their natural enemies demonstrates how neem-induced mortality serves as an effective chaos control parameter [47]. The system dynamics follow:
Where xn and yn represent pest and predator densities, and d represents the neem-induced mortality rate. Ecological interpretation reveals that balanced neem application, appropriate timing of interventions (controlled by δ), and conservation of natural enemies are key for sustainable pest control [47]. Small neem-induced mortality values destabilize prey-predator coexistence, whereas larger values restore stability, demonstrating the non-trivial response of ecological systems to control interventions.
Managing Invasive Species
Predator-prey dynamics under invasive pressure present another application for hybrid control methodologies. When an invasive predator establishes itself in a native ecosystem, it disrupts existing predator-prey balances through interspecific competition [35]. Control strategies include:
- Reintroduction/migration of native predators to restore competitive balance
- Harvesting of invasive predators to reduce competitive pressure
- Environmental challenges exploitation leveraging invasive species' maladaptation
The mathematical framework incorporates these control mechanisms through additional terms in the dynamical equations, representing reintroduction rates, harvesting efforts, and reduced conversion efficiency for invasive species [35]. This multi-pronged approach demonstrates how hybrid control strategies can address complex ecological invasions where single-method interventions prove insufficient.
Hybrid control and chaos suppression techniques provide powerful methodologies for managing complex predator-prey dynamics in ecological systems. The integration of fractional operators, parameter manipulation, and bifurcation-based control strategies enables researchers and conservation managers to stabilize potentially chaotic population fluctuations while maintaining biologically feasible coexistence states. Implementation requires careful parameter calibration through systematic stability analysis and sensitivity assessment, with control efficacy validated through numerical simulation and ecological monitoring. As ecological systems face increasing pressures from climate change, invasive species, and human management, these sophisticated control methodologies will play an increasingly vital role in sustainable ecosystem management.
Maximum Sustainable Yield (MSY) represents a fundamental concept in resource management, referring to the maximum quantity of a population that can be harvested without endangering its long-term survival [82]. In predator-prey systems, this principle becomes complex due to the interdependent dynamics between species. Recent research has demonstrated that in multi-patch environments where prey and predator populations interact across discrete habitat patches, specific conditions can lead to the total MSY of connected patches exceeding the sum of MSYs from isolated patches [82]. This counterintuitive finding has significant implications for fisheries management and ecological conservation, challenging traditional single-population approaches to sustainable harvesting.
The mathematical foundation for these developments stems from modified predator-prey models that incorporate spatial distribution and migration effects. Earlier models like the NERA framework, which categorized drug users into non-users (N), experimental (E), recreational (R), and addict (A) groups, demonstrated the applicability of predator-prey analogies to non-ecological systems but lacked limitations in growth and decay variables, preventing observation of oscillatory or chaotic regimes [83]. Contemporary approaches have addressed these limitations through the incorporation of functional response limitations and migration parameters between patches.
Key Parameters in Multi-Patch Predator-Prey Models
Table 1: Core parameters in multi-patch prey-predator models with harvesting [82]
| Parameter | Mathematical Symbol | Biological Meaning | Role in MSY Determination |
|---|---|---|---|
| Intrinsic growth rate | ri | Maximum per capita growth rate of prey in patch i | Determines recovery potential of prey population |
| Carrying capacity | Ki | Maximum prey population supported in patch i | Sets baseline for population size |
| Predation rate | ai | Rate at which predators capture prey in patch i | Influences predation pressure |
| Conversion efficiency | e | Efficiency converting prey biomass to predator biomass | Affects predator growth response |
| Mortality rate | di | Natural mortality rate of predators in patch i | Determines baseline predator loss |
| Fishing effort | E | Harvesting intensity applied to predators | Direct control variable for yield |
| Migration rate | ε | Rate of movement between patches | Spatial connectivity parameter |
Comparison of MSY Scenarios
Table 2: MSY outcomes under different connectivity regimes [82] [84]
| Scenario | Patch Configuration | Migration Rate | Key Finding | Mathematical Condition |
|---|---|---|---|---|
| Isolated | n patches | ε = 0 | Total yield equals sum of individual patch MSYs | MSYtotal = ΣMSYi |
| Homogeneous | Symmetric prey movement | ε → ∞ | Total yield equals sum of isolated patch MSYs | MSYtotal = ΣMSYi |
| Heterogeneous | Asymmetric parameters | ε → ∞ | Total yield can exceed sum of isolated patch MSYs | MSYtotal > ΣMSYi |
| Moderate connectivity | n patches with differential migration | 0 < ε < ∞ | Yield depends on specific parameter configuration | Case-specific outcome |
Analytical Protocols
Protocol 1: MSY Calculation for Single-Patch Systems
Purpose: To determine the Maximum Sustainable Yield for a predator species in an isolated patch where only predators are harvested.
Experimental Workflow:
Procedure:
- Model Formulation: Begin with the standard Rosenzweig-MacArthur or Lotka-Volterra predator-prey model with logistic prey growth and linear functional response.
- Equilibrium Analysis: Set derivatives to zero and solve for equilibrium values of prey (x) and predator (y) populations as functions of fishing effort E.
- Yield Function Definition: Define the yield function as Y(E) = E · y(E), where y(E) is the predator equilibrium as a function of effort.
- Optimization: Differentiate Y(E) with respect to E and solve for the critical point where dY/dE = 0.
- Validation: Verify the critical point represents a maximum by checking the second derivative condition d²Y/dE² < 0.
- MSY Calculation: Compute MSY = Y(E) where E is the optimal effort from step 4.
Validation Metric: The resulting predator population at E* should be positive and the prey population should not be driven to extinction.
Protocol 2: Multi-Patch MSY with Fast Migration
Purpose: To determine MSY in connected patch systems where migration occurs at a much faster timescale than population dynamics.
Experimental Workflow:
Procedure:
- System Setup: Formulate the complete n-patch model with prey and predator dispersal terms as shown in Equation Set 2.
- Fast-Slow Decomposition: Apply singular perturbation theory by taking the limit as migration rate ε → ∞.
- System Aggregation: Use Tykhonov's theorem to derive an aggregated system representing the meta-population dynamics.
- Equilibrium Computation: Calculate the equilibrium values for the aggregated system.
- Yield Comparison: Compute the total yield for the connected system and compare with the sum of yields from isolated patches.
- DIG Identification: Identify conditions leading to Dispersal-Induced Growth (DIG) where connectivity enhances sustainable yield.
Validation Metric: The aggregated model should preserve the essential dynamics of the complete system while being mathematically tractable.
Protocol 3: Parameter Estimation Using Direct Integral Method
Purpose: To estimate parameters of predator-prey models from experimental time-series data while avoiding local optima in likelihood functions.
Experimental Workflow:
Procedure:
- Experimental Design: Conduct microcosm experiments monitoring predator and prey populations over time with replicated treatments. For soil systems, maintain controlled humidity conditions (e.g., 20-100% water content) [85].
- Model Specification: Construct a system of ODEs with compartments for free predators (P), prey (N), and predator-prey complexes (C), incorporating a refuge parameter (r) for spatial heterogeneity.
- Direct Integral Implementation: Further develop the direct integral approach that exploits separability of states and parameters to overcome complex likelihood surfaces [85].
- Parameter Optimization: Estimate key parameters including interaction rate (a), refuge density (r), multiplication factor (k), and bdelloplast decay rate (s).
- Model Validation: Contrast parameter estimates with known values from literature; for microbial systems, compare estimated conversion ratios with directly measured values.
- Management Application: Implement estimated parameters in management strategies to determine optimal harvesting efforts.
Validation Metric: Parameter estimates should be biologically plausible and consistent with independently measured values where available.
The Scientist's Toolkit
Research Reagent Solutions
Table 3: Essential materials for experimental predator-prey research [85]
| Research Reagent | Specification | Function in Experiment |
|---|---|---|
| Sand microcosms | 10g fine sand per flask | Creates structured habitat with natural heterogeneity |
| Bacterial prey | Burkholderia stabilis st.2 | Model prey organism for microbial systems |
| Bacterial predator | Bdellovibrio bacteriovorus 109 J | Model predator organism for experimental ecology |
| HEPES buffer | Standard concentration | Maintains pH during experimental manipulations |
| Dilution plating materials | Sterile equipment and media | Quantifies predator and prey concentrations |
| Soil humidity controls | 20-100% water content (w/w) | Tests effect of environmental conditions on dynamics |
Economic Optimization Framework
The economic optimization of harvesting strategies extends beyond biological MSY to incorporate economic factors. While not explicitly detailed in the search results, the integration of market data from precision harvesting technologies (projected to reach $29.79 billion by 2030) with biological models represents a promising frontier [86]. Modern precision harvesting technologies incorporate yield monitoring systems, field mapping, and data analytics that can provide real-time feedback for adaptive management strategies.
Economic optimization typically involves:
- Cost Integration: Incorporating fixed and variable costs of harvesting operations
- Price Modeling: Accounting for market price fluctuations and quality premiums
- Dynamic Optimization: Using optimal control theory to determine time-varying effort strategies
- Risk Management: Incorporating uncertainty in population estimates and environmental conditions
The conditions under which MSY is enhanced in connected systems [82] [84] provide opportunities for economic gains through coordinated management across patch boundaries, potentially reducing enforcement costs while increasing sustainable yields.
The increasing frequency of biological invasions poses a significant threat to global biodiversity and ecosystem stability. Effectively managing these invasions requires robust predictive frameworks that integrate ecological theory with practical conservation strategies. This article presents application notes and protocols centered on mathematical modeling approaches for invasion management, specifically addressing reintroduction programs, migration dynamics, and biological control systems within predator-prey interaction research. The protocols outlined below provide researchers with standardized methodologies for designing, implementing, and analyzing invasion management strategies, with particular emphasis on spatially explicit modeling and experimental validation.
Theoretical Framework and Key Mathematical Models
Mathematical models provide the foundational framework for predicting invasion dynamics and testing management interventions. The following table summarizes principal models used in invasion ecology.
Table 1: Key Mathematical Models in Invasion Ecology
| Model Type | Key Equations/Components | Primary Applications | References |
|---|---|---|---|
| Allometric Trophic Network (ATN) Model | ( \frac{dNi}{dt} = riNi - \sum{j} p{ij}NiN_j ) Body-mass structured interaction coefficients | Predicting population dynamics in trophic networks; modeling consumption rates based on body size. | [87] |
| Modular Dispersal Model (MDiG) | Spatially explicit, individual-based model in GRASS-GIS; XML-defined demographic and dispersal submodels. | Simulating spatiotemporal spread in realistic landscapes; investigating habitat fragmentation effects. | [88] |
| Process-Based Species Distribution Model (SDM) | Integrates demographic processes, dispersal kernels, and environmental response functions. | Projecting establishment and spread under novel habitat and climate conditions. | [88] |
| Spatially Explicit Spread Framework | Combines a dispersal model, landscape generator, and landscape metrics. | Systematic investigation of habitat change impact on establishment and spread. | [88] |
Application Notes and Experimental Protocols
Protocol 1: Testing Trait-Based Trophic Interaction Models
This protocol is designed to test hypotheses regarding which species traits (e.g., body mass, micro-habitat use) dominate trophic interactions and are necessary to accurately model population dynamics.
1.1. Hypotheses Formulation:
- H1: In simple two-species treatments, predator impact on prey increases with predator-prey body mass ratio up to an optimal point [87].
- H2: Habitat overlap between predator and prey positively correlates with predation rates [87].
- H3: In complex communities, predators susceptible to intraguild predation will show reduced impact on shared prey due to avoidance behavior [87].
- H4: Models parameterized with body mass and habitat use data will explain more variation in species abundances than body-mass-only models [87].
1.2. Experimental Design and Organism Selection:
- Select a community of terrestrial arthropods as the model system [87].
- Choose predator and prey species to create a gradient of body mass ratios and micro-habitat use (e.g., ground vs. vegetation foragers).
- Design treatments with varying complexity: two-species (predator-prey), three-species (intraguild predation potential), and multi-species communities.
1.3. Data Collection and Sampling Regime:
- Body Mass: Measure and record body mass for all individuals.
- Habitat Use: Quantify micro-habitat use via behavioral observations or trapping data across different landscape strata.
- Population Abundances: Conduct frequent population counts. Rely on model sensitivity analysis to determine the optimal timing and frequency of sampling to maximize information content relative to effort [87].
- Interaction Strengths: Document predator-prey interaction frequencies and outcomes.
1.4. Model Parameterization and Validation:
- Parameterize the baseline ATN model using only body mass data.
- Parameterize the extended ATN model incorporating terms for micro-habitat use (
νijfor spatial overlap) and intra- and interspecific interference [87]. - Compare the predictive power of both models against the empirical abundance data from the experiment to test H4.
Protocol 2: Experimental Test of Native Predator Preference for Invasive Prey
This protocol uses choice experiments to determine if native predators actively prefer invasive prey, which is critical for identifying potential evolutionary traps.
2.1. Study System Setup:
- Native Predator: The endangered Everglade snail kite (Rostrhamus sociabilis plumbeus) [89].
- Native Prey: The Florida apple snail (Pomacea paludosa) [89].
- Invasive Prey: The exotic apple snail (Pomacea maculata) [89].
- Study Regions: Select regions with different invasion histories (e.g., Kissimmee Chain of Lakes with longer history vs. Everglades with more recent invasion) to test for experience-based effects [89].
2.2. Experimental Procedure:
- Snail Preparation: Collect native and exotic snails. Measure the shell length of each snail to the nearest mm. Group snails into size classes [89].
- Experimental Trials: Present individual snail kites with simultaneous choices in a controlled field setting. A single trial involves offering a kite a choice between:
- A native and an exotic snail of the same size.
- Snails of different sizes within and across species.
- Ensure the density and presentation of prey are standardized and controlled across all trials [89].
- Data Recorded: For each trial, record the species and size of the snail consumed first. The first choice is the indicator of preference [89].
2.3. Data Analysis:
- Analyze preference using statistical models (e.g., logistic regression) with prey choice as the dependent variable and species, size, and region as independent variables.
- A lack of preference for species, coupled with a preference for medium-sized snails (typical of large native snails), suggests consumption of exotics in the wild is driven by their high abundance, not active preference [89].
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Materials and Tools for Invasion Management Research
| Item/Reagent | Function/Application | Specification/Example |
|---|---|---|
| GRASS-GIS Software | Open-source platform for running spatially explicit models like MDiG on real-world landscapes. | http://grass.osgeo.org [88] |
| Modular Dispersal Model (MDiG) | Spatially explicit, stochastic model to simulate population dynamics and dispersal in heterogeneous landscapes. | http://github.com/ferrouswheel/mdig [88] |
| Landscape Generator | Creates replicated artificial landscapes with controllable spatial properties (e.g., habitat size, connectivity) for theoretical experiments. | Custom software integrated within the modeling framework [88] |
| Landscape Metrics | Quantifies landscape structure (e.g., patch size, connectivity) to relate spatial pattern to ecological processes. | Metrics like habitat connectivity and configuration [88] |
| Choice Experiment Arena | A controlled setting to conduct predator preference trials, eliminating confounding factors of prey density and availability. | Standardized field setup for presenting prey choices to predators like snail kites [89] |
Visualization of Workflows and Interactions
The following diagrams, generated using Graphviz, illustrate the core logical workflows and relationships described in the application notes. The color palette is restricted to the specified brand colors, with explicit text coloring to ensure high contrast for readability.
Trait-Based Interaction Modeling Workflow
Predator Preference Choice Experiment
Invasion Spread Modeling Framework
Parameter Inference, Model Validation, and Comparative Frameworks
Parameter estimation is a cornerstone of building accurate and predictive mathematical models in ecology. For predator-prey research, which relies heavily on differential equation models, determining the correct parameters from observational data is essential for understanding system dynamics, forecasting population changes, and informing conservation or management strategies. This Application Note details established and emerging computational methodologies for parameter estimation, framed within the context of modeling predator-prey interactions. We provide a structured comparison of techniques, detailed experimental protocols, and essential toolkits to guide researchers in selecting and implementing the appropriate approach for their specific research problem.
The process of parameter estimation, or model calibration, involves finding the set of parameter values that minimize the discrepancy between a model's output and experimental data. In predator-prey ecology, this typically means fitting the solutions of ordinary differential equations (ODEs) or delay differential equations (DDEs) to time-series data of species abundances.
Table 1: Comparison of Parameter Estimation Methods in Predator-Prey Research
| Method Category | Key Examples | Underlying Principle | Primary Applications in Predator-Prey Research | Key Advantages | Key Limitations |
|---|---|---|---|---|---|
| Direct Equation Discovery | SINDy, Ensemble SINDy (E-SINDy) [66] | Sparse regression to identify model structure & parameters directly from data. | Deriving governing equations from population time-series without pre-specified model structure. | Does not require an a priori model; discovers parsimonious equations. | Sensitive to noise and data sparsity; E-SINDy was developed to mitigate this [66]. |
| Optimization-Based (Frequentist) | Nonlinear Least Squares (NLS) [90] | Finds parameters that minimize the sum of squared differences between model and data. | Parameter estimation in models with pre-defined structure (e.g., Lotka-Volterra, Holling Type II). | Conceptually straightforward, widely implemented in software. | Can converge to local minima; requires good initial guesses. |
| Bayesian Inference | Hierarchical Bayesian Models (HBM) [91], Bayesian Calibration [92] | Uses Bayes' theorem to derive posterior probability distributions for parameters. | Integrating multiple data sources (e.g., field and lab data); robust uncertainty quantification [91] [92]. | Quantifies full uncertainty in parameters; incorporates prior knowledge. | Computationally intensive; requires specification of prior distributions. |
| Global Sensitivity & Calibration | Bayesian Framework with SA and Model Selection [92] | Combines parameter estimation with sensitivity analysis (SA) and model selection criteria (AIC, BIC). | Comparing multiple candidate models; identifying most influential parameters [92]. | Provides a comprehensive model assessment and selection workflow. | Complex workflow with multiple stages of analysis. |
Detailed Experimental Protocols
Protocol 1: Model Discovery using SINDy and Ensemble SINDy
Application: For identifying the functional form of the predator-prey interaction equations directly from data when the underlying model is unknown [66].
Workflow Diagram: SINDy Model Discovery Workflow
Step-by-Step Procedure:
Data Preparation and Pre-processing:
- Input: Gather time-series data of prey and predator populations,
X = [x₁(t), x₂(t), ..., xₙ(t)], wherenis the number of state variables (e.g.,n=2for moose and wolf populations) [66]. - Normalization: Normalize the data, for example, by dividing each population count by its standard deviation to create a dataset where each feature has a standard deviation of 1 [66].
- Numerical Differentiation: Compute the time derivative of the data,
dX/dt, using numerical methods (e.g., finite differences, total variation regularization, or neural networks). The quality of this step is critical for the success of SINDy.
- Input: Gather time-series data of prey and predator populations,
Library Construction:
- Construct a library
Θ(X)of candidate nonlinear functions that could describe the system's dynamics. A typical library might include:- Constant terms:
1 - Polynomial terms:
X,X^P₂,X^P₃(whereP₂andP₃represent quadratic and cubic nonlinearities) - Trigonometric terms:
sin(X),cos(X) - Other functions:
1/X, etc. [66]
- Constant terms:
- The library should be sufficiently large to capture the true dynamics but not so large as to be computationally prohibitive.
- Construct a library
Sparse Regression:
- Formulate the linear system:
dX/dt = Θ(X) Ξ, whereΞ = [ξ₁, ξ₂, ..., ξₙ]is a matrix of sparse coefficient vectors to be determined [66]. - Use the Sequentially Thresholded Least Squares (STLSQ) algorithm to solve for
Ξ. This algorithm performs linear regression and then sets all coefficients below a chosen thresholdλto zero. This process is repeated until the non-zero coefficients converge. Thel₂-regularization constantαmay also be used [66].
- Formulate the linear system:
Ensemble Method for Robustness (E-SINDy):
- For noisy or limited data, employ the E-SINDy algorithm, which integrates robust bagging (bragging) techniques. This involves generating multiple bootstrapped samples of the data, applying SINDy to each sample, and then aggregating the results (e.g., using the median) to produce a final, more robust model [66].
Model Selection and Validation:
- Use model selection techniques like the Akaike Information Criterion (AIC) or Bayesian Information Criterion (BIC) to select the best model from the candidate models generated by SINDy with different thresholds or library terms [66] [92].
- Validate the final model,
dx/dt = Θ(x^T) ξₖ, on a withheld portion of the data not used during the identification process.
Protocol 2: Bayesian Calibration for a Predefined Model
Application: For estimating parameters and their uncertainties in a known model structure, combining prior knowledge with new data. Ideal for integrating different data types and robust uncertainty quantification [91] [92].
Workflow Diagram: Bayesian Model Calibration Workflow
Step-by-Step Procedure:
Define the Mathematical Model:
- Start with a predefined model structure, such as a system of ODEs. For example, a model incorporating a Holling Type-II functional response and multiple delays (
σ₁, σ₂, τ) for gestation and maturation [90].
- Start with a predefined model structure, such as a system of ODEs. For example, a model incorporating a Holling Type-II functional response and multiple delays (
Specify Prior Distributions:
- For each parameter to be estimated, specify a prior distribution based on existing literature, expert knowledge, or previous experiments. For instance, if a mortality rate is known to be positive and likely small, a Gamma distribution might be an appropriate prior.
Construct the Likelihood Function:
- The likelihood function quantifies the probability of observing the experimental data given a specific set of model parameters. It typically assumes that the discrepancies between the model output and the data are normally distributed, though other distributions can be used.
Sample the Posterior Distribution:
- Use Markov Chain Monte Carlo (MCMC) sampling algorithms (e.g., Metropolis-Hastings, Hamiltonian Monte Carlo) to draw samples from the joint posterior distribution of the parameters. This distribution is proportional to the product of the likelihood and the prior distributions.
- Tools like Stan, PyMC, or JAGS are commonly used for this computationally intensive step.
Diagnostics and Validation:
- Check MCMC convergence using diagnostics (e.g., trace plots, Gelman-Rubin statistic
ˆR). - Validate the calibrated model by checking its predictive performance against validation data. Sensitivity analysis can then be used to identify the parameters to which the model output is most sensitive [92].
- Check MCMC convergence using diagnostics (e.g., trace plots, Gelman-Rubin statistic
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Computational Tools and Reagents for Parameter Estimation
| Item Name | Function / Role in Workflow | Example Uses / Notes |
|---|---|---|
| Time-Series Population Data | The fundamental input for all parameter estimation methods. | e.g., Moose-Wolf data from Isle Royale (1959-2019) [66], aphid-ladybeetle data [92]. Data quality is paramount. |
| Normalization Scripts | Pre-processing data to ensure numerical stability and equal weighting of variables. | Normalizing data by standard deviation or mean [66]. Implementable in Python (NumPy/SciPy) or R. |
| Numerical Differentiation Tools | Calculate derivatives from noisy data for methods like SINDy. | Finite differences, Savitzky-Golay filters, or total variation regularization. |
| SINDy/E-SINDy Algorithm | Core engine for sparse identification of nonlinear dynamics. | Implemented in the PySINDy package in Python. Key parameters: threshold λ, regularization α [66]. |
| MCMC Sampling Software | Engine for drawing samples from complex posterior distributions in Bayesian inference. | Stan, PyMC (Python), or rstan (R). Requires specification of model, priors, and likelihood. |
| Model Selection Criteria | Objective metrics to compare the goodness-of-fit of different models while penalizing complexity. | Akaike Information Criterion (AIC) and Bayesian Information Criterion (BIC) [66] [92]. |
| Sensitivity Analysis Tools | Identify parameters with the greatest influence on model output to guide estimation and refinement. | Methods like Latin Hypercube Sampling (LHS) and Partial Rank Correlation Coefficient (PRCC) [66]. |
Within the broader context of research on mathematical models for predator-prey interactions, experimental validation in controlled systems is paramount for bridging theoretical predictions and real-world dynamics. While classic models like Lotka-Volterra equations describe idealized oscillatory relationships, their practical application requires validation through tractable experimental systems [8] [93]. Soil microcosms represent a powerful platform for this purpose, enabling researchers to study microbial predator-prey interactions—such as those between bacteriovorous protists and their bacterial prey—with a level of control impossible in field studies. This document outlines detailed application notes and protocols for employing soil microcosms to validate and refine mathematical models of predator-prey dynamics, with a focus on generating high-quality, quantitative data for model parameterization.
Key Experimental Protocols in Soil Microcosm Research
The following section details specific methodologies adapted from recent literature for investigating predator-prey dynamics and microbial community responses in soil microcosms.
Protocol: Establishing Base Cation-Amended Microcosms to Investigate Nutrient Limitation
This protocol tests how nutrient availability, a key parameter in many predator-prey models, influences the functional composition of microbial communities, including predator populations [94].
1. Materials:
- Soil: Nutrient-poor forest soil (e.g., Hyperdystric Cambisol), sieved to 2 mm.
- Fertilizer Solutions: Aqueous solutions of potassium chloride (KCl) and magnesium chloride (MgCl₂), prepared with deionized water and pH-adjusted to match the native soil pH.
- Microcosms: 125 mL nominal glass bottles.
- Equipment: Scale, pH meter, foam plugs, incubation chamber.
2. Procedure: 1. Dispense 10 g (dry weight equivalent) of sieved soil into each glass bottle. 2. Apply treatments in triplicate: * Control (Ct): Add a volume of pH-adjusted deionized water. * K-fertilized (K): Add a volume of KCl solution to achieve a target exchangeable K content (e.g., 0.23 cmol⁺ kg⁻¹). * Mg-fertilized (Mg): Add a volume of MgCl₂ solution to achieve a target exchangeable Mg content (e.g., 0.32 cmol⁺ kg⁻¹). 3. Mix the soil and solution thoroughly within each microcosm. 4. Seal the microcosm with a foam plug to allow gas exchange while minimizing water loss. 5. Incubate in the dark at a constant temperature (e.g., 25°C) for up to 2 months. 6. Maintain soil moisture by weighing microcosms weekly and replenishing with distilled water. 7. Destructively harvest microcosms at multiple time points (e.g., 15, 30, 45, 60 days) for analysis.
3. Key Measurements for Model Validation:
- Soil Chemistry: Measure exchangeable K⁺, Mg²⁺, and cationic exchange capacity (CEC) at each harvest [94].
- Functional Trait Analysis: Quantify the abundance of specific functional groups (e.g., mineral-weathering bacteria) via culture-dependent bioassays and quantitative PCR (qPCR) of taxonomic markers (e.g., for genera Burkholderia and Collimonas) [94].
- Community Metabolism: Profile metabolic potential using Biolog EcoPlates and measure basal soil respiration with MicroResp systems [94].
Protocol: Quantifying Nitrate Utilization Dynamics under pH Perturbation
This protocol uses a consumer-resource framework to model how environmental stress (pH shift) affects a functional process (nitrate utilization), analogous to a stress-induced shift in predator-prey dynamics [95].
1. Materials:
- Soil Slurries: Soil collected from multiple sites along a natural pH gradient, mixed with water.
- Perturbation Agents: Strong acid (e.g., HCl) and strong base (e.g., NaOH) solutions.
- Inhibitor: Chloramphenicol solution to inhibit protein synthesis.
- Nitrate Source: Potassium nitrate (KNO₃) solution.
- Microplates: Suitable for anaerobic incubation and high-throughput metabolite measurement.
2. Procedure: 1. Create soil slurries from each sample. 2. Perturb the pH of the slurries across a defined range (e.g., pH 3 to 9) using the acid/base solutions. 3. Amend all slurries with a final concentration of 2 mM nitrate. 4. For each soil and pH condition, set up two parallel microcosms: * Untreated: To measure total activity (pre-existing + growth). * Chloramphenicol-treated: To measure pre-existing metabolic activity without growth. 5. Incubate microcosms under anaerobic conditions for 4 days. 6. Monitor nitrate and nitrite concentrations daily using colorimetric assays or ion chromatography.
3. Data for Model Parameterization:
- The linear rate of nitrate depletion in chloramphenicol-treated samples provides a direct measure of pre-existing functional biomass.
- The non-linear (e.g., exponential) nitrate dynamics in untreated samples indicates growth of the functional population, constrained by nutrient availability [95].
The workflow for this protocol is outlined in the diagram below.
Quantitative Data Presentation and Analysis
Data generated from microcosm experiments must be synthesized for direct use in mathematical models. The following tables summarize exemplary data types.
Table 1: Representative Soil Chemical Properties Following Experimental Fertilization [94]
| Treatment | Exchangeable K (cmol⁺ kg⁻¹) | Exchangeable Mg (cmol⁺ kg⁻¹) | Cationic Exchange Capacity (CEC) | pH |
|---|---|---|---|---|
| Control | 0.12 ± 0.004 | 0.07 ± 0.008 | Unchanged | Unchanged |
| K-Fertilized | 0.23 ± 0.02 | 0.05 ± 0.007 | Unchanged | Unchanged |
| Mg-Fertilized | 0.12 ± 0.004 | 0.32 ± 0.05 | Unchanged | Unchanged |
Table 2: Functional Response of Microbial Communities to Carbon Amendments [96]
| Carbon Source | Application Dose (% C eq soil dw⁻¹) | Effect on High-Affinity H₂-Oxidizing Bacteria (HA-HOB) Activity | Change in Bacterial Alpha Diversity |
|---|---|---|---|
| Cellulose | 0.1% | Stimulated | Minor or No Change |
| Cellulose | 1%, 3%, 5% | No Effect or Suppressed | Minor or No Change |
| Sucrose | 0.1% | Slightly Suppressed | Minor Change |
| Sucrose | 1%, 3%, 5% | Strongly Suppressed (∼50% abatement) | Significant Loss |
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Reagents and Materials for Soil Microcosm Experiments
| Item | Function/Application in Experiment |
|---|---|
| Chloramphenicol | A protein synthesis inhibitor used to separate pre-existing enzyme activity from new microbial growth in metabolic studies [95]. |
| Biolog EcoPlates | Microplates containing 31 different carbon sources to profile the metabolic potential and functional diversity of soil microbial communities [94]. |
| PCR & qPCR Reagents | For absolute quantification of total bacterial/fungal abundance (using 16S rRNA/ITS gene targets) and specific functional genes (e.g., hhyL for hydrogenase) [94] [97]. |
| MicroResp System | A colorimetric system for measuring soil basal respiration and substrate-induced respiration responses in a high-throughput format [94]. |
| DNA Extraction Kit (e.g., DNeasy PowerLyzer PowerSoil) | For standardized and efficient extraction of high-quality genomic DNA from complex soil matrices, essential for downstream molecular analyses [96]. |
Modeling Framework: From Data to Dynamical Models
Data from the above protocols feed directly into mathematical models. The classic Lotka-Volterra framework provides a starting point but requires refinement for microbial systems [8] [93]. The consumer-resource model used in the pH perturbation study is an excellent example of a more mechanistic approach [95]. It can be represented by the following differential equations, which are highly suitable for modeling microbial predator-prey dynamics:
[ \begin{aligned} \frac{dA}{dt} &= -rA \cdot x \cdot \frac{A}{KA + A} \quad \text{(Nitrate/Prey Consumption)} \ \frac{dx}{dt} &= \gamma \cdot x \cdot \left( \frac{A}{KA + A} \right) \cdot \left( \frac{C}{KC + C} \right) \quad \text{(Predator/Functional Biomass Growth)} \ \frac{dC}{dt} &= -rC \cdot x \cdot \frac{C}{KC + C} \quad \text{(Limiting Nutrient Consumption)} \end{aligned} ]
Where:
- (A): Concentration of nitrate (or prey).
- (x): Abundance of functional nitrate-utilizing (or predatory) biomass.
- (C): Concentration of a growth-limiting nutrient (or secondary resource).
- (rA, rC): Maximum consumption rates.
- (KA, KC): Half-saturation constants (affinities).
- (\gamma): Maximum growth rate of biomass.
The structure and flow of this modeling approach are depicted below.
The study of predator-prey interactions represents a cornerstone of theoretical and computational ecology, providing critical insights into population dynamics, ecosystem stability, and evolutionary processes. Traditional approaches have relied heavily on mathematical frameworks, such as the Lotka-Volterra equations, and agent-based Monte Carlo simulations to model these complex, co-evolutionary systems [98] [99]. However, accurately analyzing and predicting the intelligent adaptation of interacting species remains a formidable challenge in computational biology [98].
The integration of modern machine learning (ML) techniques is revolutionizing this field by offering powerful new tools for stability analysis and behavioral prediction. These data-driven approaches can uncover complex patterns that are difficult to capture with traditional mechanistic models alone. This application note explores the integration of machine learning methodologies—from deep reinforcement learning to classification algorithms—for enhancing the analysis of predator-prey ecosystem stability, providing detailed protocols for their implementation within ecological research.
Application Notes & Protocols
Protocol 1: Stability Classification with Ensemble Learning
The following protocol details the procedure for using ensemble learning methods, specifically Random Forest classifiers, to determine the stability of fixed points in discrete-time predator-prey models. This approach serves as a computational surrogate for analytical stability analysis, offering significant efficiency advantages for complex models [47].
Background and Principle: In discrete-time ecological models, the stability of fixed points determines whether populations will coexist stably, oscillate, or exhibit chaotic dynamics. Traditional analytical methods involve computing Jacobian matrices and their eigenvalues, which can be computationally intensive for models with multiple parameters [47]. Machine learning classifiers can learn the mapping from model parameters to stability regions directly from data, enabling rapid stability assessment.
Experimental Workflow:
Model Discretization and Data Generation:
- Begin with a continuous-time predator-prey model incorporating key ecological features such as logistic prey growth, neem-induced mortality (or other external interventions), and predator crowding effects [47].
- Discretize the model using an appropriate scheme, such as the piecewise constant argument method, to obtain a system of difference equations:
- ( x{n+1} = xn e^{\delta (r - a xn - b yn - d)} )
- ( y{n+1} = yn e^{\delta (-s + c xn - \alpha yn)} )
- Where ( xn ) and ( yn ) represent prey and predator densities at time ( n ), ( r ) and ( s ) are intrinsic growth and mortality rates, ( a ) and ( \alpha ) quantify intraspecific competition, ( b ) and ( c ) define predation interaction strength, and ( d ) represents external mortality [47].
- Systematically sample the parameter space ( (r, a, b, c, d, s, \alpha, \delta) ) using methods like Latin Hypercube Sampling.
Stability Labeling:
- For each parameter set, compute the Jacobian matrix ( J ) at the non-trivial fixed point.
- Calculate the eigenvalues ( \lambda1, \lambda2 ) of ( J ).
- Assign stability labels based on the eigenvalues:
- Stable Node: ( |\lambda1|, |\lambda2| < 1 )
- Unstable: ( |\lambda1| > 1 ) or ( |\lambda2| > 1 )
- Flip Bifurcation: ( \lambda1 \approx -1 ) or ( \lambda2 \approx -1 )
- Neimark-Sacker Bifurcation: Complex eigenvalues with ( |\lambda| \approx 1 )
Classifier Training and Validation:
- Split the generated dataset into training (70%), validation (15%), and test (15%) sets.
- Train both Decision Tree and Random Forest classifiers on the training set. The Random Forest, as an ensemble method, typically provides superior accuracy and smoother stability boundaries [47].
- Tune hyperparameters (e.g., maximum tree depth, number of trees, minimum samples per leaf) using the validation set to optimize performance.
- Evaluate final model performance on the held-out test set, reporting metrics such as accuracy, precision, recall, and F1-score.
Feature Importance Analysis:
- Use the trained Random Forest model to compute Gini importance or permutation importance for each input parameter.
- This analysis reveals which ecological parameters most strongly influence system stability, providing biological insights. For instance, studies have shown that prey dynamics are often driven by prey-related parameters ( (r, a, b) ), while predator persistence is strongly influenced by conversion efficiency ( (c) ) and natural mortality ( (s) ) [47].
Applications: This protocol is particularly valuable for rapid assessment of management strategies, such as determining the optimal intensity and timing of biopesticide application (e.g., neem) to suppress pest (prey) populations without destabilizing the ecosystem or driving natural predator populations to extinction [47].
Protocol 2: Predictive Modeling via SINDy and Deep Learning
This protocol outlines two distinct approaches for building predictive models of predator-prey dynamics: one using system identification from population data, and another using deep learning to forecast individual pursuit trajectories.
Part A: System Identification from Population Time Series
Background: Sparse Identification of Nonlinear Dynamics (SINDy) is a data-driven technique that discovers governing equations directly from time-series data, without requiring prior knowledge of the system's functional form. It is especially useful for deriving parsimonious models from noisy ecological data [66].
Experimental Workflow:
Data Collection and Preprocessing:
- Collect longitudinal population data for predator and prey species (e.g., the long-term moose-wolf data from Isle Royale National Park) [66].
- Normalize the data by subtracting the mean and dividing by the standard deviation of each population time series to ensure features are on a comparable scale.
- Numerically compute the time derivatives ( \dot{x} ) and ( \dot{y} ) from the normalized data ( x(t) ) and ( y(t) ).
Library Construction:
- Construct an extensive library ( \Theta(X) ) of candidate nonlinear functions that could describe the system dynamics. For ecological systems, this typically includes:
- Constant and Polynomial Terms: ( 1, X, X^{P2}, X^{P3} ) (e.g., ( x, y, x^2, y^2, xy ))
- Other Potential Terms: Trigonometric functions, rational terms.
- The library matrix is defined as: ( \Theta(X) = \begin{bmatrix} | & | & | & | \ 1 & X & X^{P_2} & \cdots \ | & | & | & | \end{bmatrix} ).
- Construct an extensive library ( \Theta(X) ) of candidate nonlinear functions that could describe the system dynamics. For ecological systems, this typically includes:
Sparse Regression and Model Selection:
- Formulate the regression problem: ( \dot{X} = \Theta(X) \Xi ), where ( \Xi ) is a matrix of sparse coefficient vectors to be determined.
- Employ the Sequentially Thresholded Least Squares (STLSQ) algorithm to promote sparsity, iteratively setting small coefficients to zero.
- To enhance robustness with limited or noisy data, use the Ensemble SINDy (E-SINDy) variant, which applies SINDy to multiple bootstrapped subsets of the data and aggregates the results [66].
- Select the final model using information criteria (AIC or BIC) to balance goodness-of-fit against model complexity.
Model Validation and Sensitivity Analysis:
- Validate the discovered model by simulating its dynamics and comparing predictions to held-out data.
- Perform global sensitivity analysis, such as Latin Hypercube Sampling with Partial Rank Correlation Coefficient (PRCC) analysis, to quantify how uncertainty in the model parameters impacts key outputs like population stability or oscillation periods [66].
Part B: Trajectory Prediction in Pursuit-Escape Interactions
Background: Deep learning models can capture the high-dimensional, nonlinear, and interactive nature of pursuit-evasion behaviors at the individual level, which are difficult to model with differential equations alone [100].
Experimental Workflow:
Dataset Creation:
- Construct a Pursuit-Escape Confrontation (PEC) dataset. This involves recording interactions, for example, between a predatory mouse and an evasive robotic bait, tracking their trajectories with high temporal resolution [100].
- Annotate the data with positions, velocities, and headings of both predator and prey over time.
Model Architecture (PursuitNet):
- Implement a deep learning architecture that integrates:
- Transformer Encoders: To capture long-range dependencies and attention mechanisms focusing on critical moments in the interaction.
- Graph Convolutional Networks (GCNs): To model the dynamic spatial relationships between predator and prey. The graph structure can be updated over time, with nodes representing agent positions and edges representing their relative distances or headings.
- Temporal Convolutional Networks (TCNs): To extract features from the time series of past trajectories.
- The model should input a sequence of past states and output predictions of future trajectories.
- Implement a deep learning architecture that integrates:
Model Training and Evaluation:
- Train the model using mean squared error (MSE) or similar loss functions between predicted and true future trajectories.
- Evaluate performance on a test set of unseen interactions, using metrics like Average Displacement Error (ADE) and Final Displacement Error (FDE) to quantify prediction accuracy.
Applications: Predictive models of pursuit dynamics have applications beyond ecology, including robotics, autonomous vehicles, and multi-agent simulation systems, where understanding and forecasting competitive, interactive motion is crucial [100].
Visualization of Workflows
The following diagrams illustrate the core logical and experimental workflows described in the protocols.
Stability Classification Workflow
Prediction Modeling Pipeline
The Scientist's Toolkit: Research Reagent Solutions
The following table details key computational tools, algorithms, and platforms essential for implementing the machine learning protocols described in this note.
Table 1: Essential Research Reagents and Tools for ML-Based Predator-Prey Research
| Tool/Reagent Name | Type/Category | Primary Function in Research | Example Application Context |
|---|---|---|---|
| Random Forest Classifier | Ensemble Learning Algorithm | Classifies the stability of ecosystem fixed points by learning from parameter-eigenvalue relationships [47]. | Determining safe application thresholds for biopesticides to avoid destabilizing predator-prey systems [47]. |
| SINDy/E-SINDy Algorithm | System Identification Method | Discovers parsimonious, interpretable governing equations directly from noisy population time-series data [66]. | Deriving a model for moose-wolf dynamics from long-term Isle Royale census data [66]. |
| PursuitNet Architecture | Deep Learning Model | Predicts future trajectories in competitive pursuit-evasion interactions by modeling spatio-temporal relationships [100]. | Forecasting the evasion path of a prey based on the predator's approach angle and speed [100]. |
| Multi-Agent Reinforcement Learning (MARL) | Reinforcement Learning Framework | Models co-adaptive learning, where predators and prey continuously evolve their strategies in response to each other [98]. | Simulating the long-term co-evolution of hunting and escape behaviors in a virtual ecosystem [98]. |
| VColCOS Φ / Colias-IV Robots | Swarm Robotics Platform | Provides a physical platform to validate simulated multi-agent interactions with real-world noise and constraints [101]. | Testing if pursuit algorithms developed in simulation produce similar emergent behaviors with physical robots [101]. |
| Stochastic Differential Equation (SDE) Models | Mathematical Modeling Framework | Incorporates environmental noise and stochasticity into agent-based movement models for more realistic simulations [39]. | Studying how random disturbances affect the success rates of different collective hunting strategies in fish schools [39]. |
The table below consolidates key quantitative findings and parameters from the referenced studies, providing a benchmark for comparison and implementation.
Table 2: Summary of Quantitative Data from ML-Ecology Studies
| Study Focus | Key Model/Algorithm | Performance Metrics / Key Findings | Critical Parameters Identified |
|---|---|---|---|
| Stability Classification [47] | Random Forest & Decision Tree | Random Forest achieved higher accuracy and smoother stability boundaries compared to a single Decision Tree. | Prey dynamics: r (growth), a (self-crowding), b (predation pressure). Predator persistence: c (conversion efficiency), s (mortality) [47]. |
| Equation Discovery [66] | Ensemble SINDy (E-SINDy) | Successfully discovered a governing model for the moose-wolf system from 61 data points (1959-2019), validated with sensitivity analysis (PRCC). | Model structure and coefficients were derived directly from normalized population data [66]. |
| Trajectory Prediction [100] | PursuitNet (Transformer+GCN+TCN) | Effectively predicted competitive pursuit trajectories with abrupt turns; outperformed models designed for smoother pedestrian motion. | Model captured dynamic spatial relationships (graph edges) and temporal dependencies for forecasting [100]. |
| Co-Evolution & Learning [98] | Multi-Agent Deep RL | RL-enabled predators achieved sustainable coexistence with prey, showing reduced extinction risk and ecologically plausible dynamics (e.g., oscillations). | Policies were learned through interaction, based on rewards for survival and successful hunting/escaping [98]. |
| Collective Hunting [39] | Stochastic Differential Equations | Collective hunting (center/nearest attack) enhanced capture efficiency, but benefits diminished beyond a critical predator group size due to competition. | Efficiency depends on the balance between school size, attack strategy, and intra-predator interference [39]. |
The study of predator-prey interactions represents a cornerstone of ecological modeling, providing critical insights into population dynamics, ecosystem stability, and species conservation. The quantitative analysis of these complex biological systems relies heavily on mathematical models and computational algorithms to interpret experimental data and predict system behaviors. This application note establishes a structured framework for evaluating algorithmic performance within predator-prey research, presenting standardized metrics, detailed experimental protocols, and visualization tools designed to enhance reproducibility and cross-study comparison. By implementing rigorous evaluation standards, researchers can more effectively quantify model accuracy, computational efficiency, and predictive validity across diverse ecological contexts, ultimately advancing our understanding of species interactions and ecosystem dynamics.
Performance Metrics for Predator-Prey Models
Evaluating algorithmic performance in predator-prey modeling requires multiple metrics to assess different aspects of model quality, from predictive accuracy to computational efficiency. The selection of appropriate metrics must align with the specific research objectives and data characteristics.
Table 1: Core Performance Metrics for Predator-Prey Algorithm Evaluation
| Metric Category | Specific Metric | Mathematical Definition | Interpretation in Predator-Prey Context | Ideal Value |
|---|---|---|---|---|
| Predictive Accuracy | Mean Absolute Error (MAE) | MAE = (1/n) * Σ|yi - ŷi| |
Average absolute difference between predicted and observed population sizes | Closer to 0 |
| Root Mean Square Error (RMSE) | RMSE = √[(1/n) * Σ(yi - ŷi)²] |
Standard deviation of prediction errors, penalizes larger errors | Closer to 0 | |
| Classification Performance | Accuracy | Acc = (TP+TN)/(TP+TN+FP+FN) |
Correct classification of system states (e.g., coexistence, extinction) | Closer to 1 |
| Area Under ROC Curve (AUC) | Area under receiver operating characteristic curve | Ability to distinguish between different dynamic regimes | Closer to 1 | |
| Computational Efficiency | Training Time | Total computation time for model development | Practical feasibility for complex systems | Lower preferred |
| Inference Time | Time to generate predictions from new inputs | Responsiveness for real-time applications | Lower preferred |
When applying these metrics, researchers must consider dataset characteristics that significantly impact interpretation. For classification tasks involving imbalanced datasets (e.g., rare extinction events), accuracy alone can be misleading [102]. In such cases, metrics like precision, recall, and the F1-score provide a more nuanced evaluation of model performance. Similarly, for probabilistic models, likelihood-based measures and proper scoring rules offer robust assessment frameworks.
Experimental Protocols for Algorithm Evaluation
Standardized Workflow for Model Comparison
Implementing a rigorous experimental protocol ensures fair and reproducible comparison of algorithmic approaches. The following structured workflow adapts established machine learning evaluation methodologies to the specific requirements of ecological modeling [102] [103].
Table 2: Experimental Protocol for Predator-Prey Algorithm Assessment
| Protocol Step | Implementation Details | Specific Considerations for Ecological Models |
|---|---|---|
| 1. Problem Definition | Define specific prediction target (e.g., population at t+1, stability classification) | Clearly state ecological hypothesis and modeling objectives |
| 2. Data Preparation | Collect historical population data; Handle missing values; Address temporal autocorrelation | Consider environmental covariates; Account for sampling effort variations |
| 3. Feature Engineering | Create lagged variables; Calculate derived metrics (growth rates, interaction strengths) | Incorporate seasonal indicators; Domain knowledge-driven feature creation |
| 4. Model Training | Split data chronologically (not randomly); Use rolling window validation for time series | Ensure sufficient cycles for oscillation capture; Balance model complexity with data availability |
| 5. Model Evaluation | Apply metrics from Table 1; Use statistical tests for performance differences | Evaluate ecological plausibility alongside statistical performance |
| 6. Model Deployment | Implement in production environment; Establish monitoring for performance drift | Plan for adaptive management applications; Establish revision triggers |
A critical consideration in this workflow is the temporal splitting of data. Unlike traditional random splitting, chronological partitioning preserves the time-dependent structure of ecological data, preventing data leakage and providing a more realistic assessment of predictive performance [102]. For predator-prey systems exhibiting oscillatory behavior, the training dataset must contain sufficient complete cycles to capture the fundamental dynamics.
Advanced Methodologies for Specific Research Contexts
Probabilistic Analytical Modeling (PAM)
For analyzing individual-level predator-prey interactions, Probabilistic Analytical Modeling (PAM) integrates deterministic dynamics with experimental measurements of natural variation [23]. The PAM methodology proceeds through four structured phases:
- Dynamic Model Selection: Choose or develop a pursuit-evasion model (e.g., Pure Pursuit, Deviated Pure Pursuit) that articulates predator or prey tactics [23]
- Parameter Distribution Fitting: For each probabilistic parameter, fit a probability density function (PDF) to experimental kinematic measurements [23]
- Success Metric Definition: Mathematically define and calculate the expected value of key success metrics (e.g., capture probability, survival rate) using probability theory [23]
- Sensitivity Analysis: Systematically vary PDF means to determine parameter influence on the expected value of the success metric [23]
This approach successfully predicted survivorship patterns in zebrafish larvae using measured probability density functions as parameters, demonstrating its utility in data-driven ecological modeling [23].
Incorporating Disease Dynamics
When investigating predator-prey systems affected by pathogens, the SIR (Susceptible-Infectious-Recovered) framework extends traditional modeling approaches [8]. The experimental protocol requires:
- Population Stratification: Divide both predator and prey populations into susceptible, infectious, and recovered compartments [8]
- Transmission Parameterization: Quantify disease transmission rates within and between species using maximum likelihood methods [8]
- Interaction Modification: Assess how disease-induced vulnerability alters predation rates and functional responses [8]
This approach enables researchers to evaluate how algorithmic performance varies when accounting for disease-mediated interactions, such as the increased susceptibility of infected prey [8].
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Research Tools for Predator-Prey Algorithm Development
| Tool/Category | Specific Examples | Function in Research | Implementation Considerations |
|---|---|---|---|
| Programming Environments | Python with Scikit-learn, R with deSolve | Model implementation, parameter estimation, and simulation | Scikit-learn provides comprehensive machine learning algorithms [103] |
| Specialized Modeling Frameworks | Prophet (time series), PAM (individual interactions) | Handling seasonal dynamics, incorporating probabilistic elements | Prophet effectively manages changepoints and seasonalities [104] |
| Data Visualization Tools | Carbon Charts, Viz Palette | Accessible result presentation, color palette evaluation | Viz Palette analyzes just-noticeable differences between colors [105] |
| Statistical Analysis Packages | SAS, IBM SPSS Modeler | Advanced statistical modeling, comprehensive forecasting | SAS offers robust statistical modeling for complex forecasting needs [104] |
| Model Evaluation Suites | Custom metric implementations, Statistical test frameworks | Performance assessment, significance testing of differences | Proper statistical tests are essential for comparing classifier performance [102] |
Workflow Visualization
Research Workflow for Algorithm Evaluation
Probabilistic Analytical Modeling Approach
Mathematical models of predator-prey interactions, particularly the Lotka-Volterra equations, have served as fundamental tools in theoretical ecology and beyond since their development in the early 20th century [1] [8]. These models provide a simplified mathematical framework to describe the oscillatory dynamics observed between interacting species, where the growth rate of one population is intrinsically linked to the size of the other [1]. The classic Lotka-Volterra equations are expressed as:
dx/dt = αx - βxy dy/dt = -γy + δxy
where x represents prey density, y represents predator density, α is the prey growth rate, β is the predation rate, γ is the predator death rate, and δ is the predator growth rate due to prey consumption [1].
Despite their conceptual elegance and historical importance, these models operate under significant simplifying assumptions that limit their direct application to complex biological systems [8]. They assume unlimited food supply for prey, constant environmental conditions, homogeneous population distributions, instantaneous population responses, and limitless predator appetites [1]. In laboratory settings, these assumptions create "too idealized" conditions that fail to capture crucial environmental interactions, while in nature, the "amount of environmental variance, the presence of competing mechanisms, and natural disturbances" further challenge model accuracy [8].
Quantitative Analysis of Model Limitations and Extensions
Table 1: Core Limitations of the Basic Lotka-Volterra Model
| Limitation Category | Specific Deficiency | Biological Reality | Impact on Predictive Accuracy |
|---|---|---|---|
| Population Structure | Does not account for age, sex, or genetic differences between organisms [8] | Populations have complex age structures and genetic diversity that affect reproduction and survival rates | Fails to predict population resilience to harvesting or environmental stress |
| Resource Constraints | Prey population grows indefinitely without predators [8] | Resources are finite; prey growth is limited by carrying capacity | Overestimates prey population sizes and oscillation amplitudes |
| Interaction Dynamics | Assumes linear predator-prey interactions and immediate effects [8] | Ecological interactions involve time lags and non-linear functional responses | Incorrectly predicts phase relationships and stability properties |
| Environmental Factors | Ignores environmental stochasticity, disease, and competing species [8] | Populations exist in complex ecosystems with multiple interacting factors | Cannot account for external disturbances or multi-species dynamics |
| Spatial Considerations | Assumes homogeneous mixing of populations [1] | Organisms are distributed heterogeneously across landscapes with limited mobility | Fails to predict metapopulation dynamics and spatial refuge effects |
Table 2: Extended Predator-Prey Modeling Approaches
| Model Extension | Key Features | Mathematical Formulation | Addresses Which Limitations |
|---|---|---|---|
| Density-Dependent Prey Growth | Incorporates carrying capacity for prey population [8] | dx/dt = rx(1 - x/K) - αxy | Prey overpopulation; More realistic growth constraints |
| SIR-Based Epidemic Models | Divides populations into Susceptible, Infected, Recovered compartments [106] | dS/dt = -βIS; dI/dt = βIS - γI; dR/dt = γI | Disease impacts; Complex interaction pathways |
| Probabilistic Analytical Modeling (PAM) | Incorporates natural variation in kinematic parameters [23] | E[Y] = ∫h(x)f_X(x)dx | Behavioral variability; Individual differences |
| Ratio-Dependent Functional Response | Predation rate depends on predator-prey ratio rather than just prey density [1] | dx/dt = rx - α(x/y)y; dy/dt = βα(x/y)y - δy | Unrealistic predation at low prey densities |
Experimental Protocols for Model Validation and Application
Protocol: Parameterizing Lotka-Volterra Models with Laboratory Data
Purpose: To empirically determine the parameters (α, β, γ, δ) of the Lotka-Volterra equations using controlled laboratory experiments with protist or arthropod systems.
Materials and Reagents:
- Model Organisms: Prey species (e.g., Paramecium aurelium), Predator species (e.g., Didinium nasutum)
- Growth Medium: Sterile nutrient media appropriate for the chosen species
- Environmental Chamber: Temperature-controlled incubator with light cycle control
- Counting Apparatus: Microscope with counting chamber or automated image-based counting system
- Data Recording: Statistical software for parameter estimation (R, MATLAB, or Python with SciPy)
Procedure:
- Monoculture Experiments: Establish separate cultures of prey and predator species to determine intrinsic growth (α) and death (γ) rates. Monitor population densities every 12 hours for 5-7 generations.
- Predation Rate Quantification: Introduce fixed predator densities to varying prey densities and measure consumption rates over 2-4 hour intervals to estimate the predation coefficient (β).
- Predator Growth Efficiency: Provide predators with known quantities of prey and monitor predator reproduction rates to determine conversion efficiency (δ).
- Coupled Dynamics: Initiate cultures with varying initial prey:predator ratios and census populations daily until oscillations dampen or populations collapse.
- Parameter Estimation: Use nonlinear least-squares regression to fit the Lotka-Volterra equations to the coupled dynamics data, optimizing parameter values to minimize residual sum of squares.
- Model Validation: Compare predicted oscillations to observed population dynamics using goodness-of-fit measures (R², AIC).
Troubleshooting:
- If oscillations dampen too quickly, consider adding spatial refuges for prey or implementing the density-dependent modification.
- If parameter estimates vary significantly between replicates, increase sample size and ensure environmental conditions remain constant.
Protocol: Incorporating Disease Dynamics Using SIR Framework
Purpose: To extend predator-prey models to account for infectious disease impacts using the SIR compartmental framework.
Materials and Reagents:
- Experimental System: Suitable host-pathogen system (e.g., flea-tomato spotted wilt virus, butterfly-baculovirus)
- Diagnostic Tools: Pathogen detection assay (PCR, ELISA, or plaque assay)
- Containment Facilities: Appropriate biosafety level accommodations for the pathogen
- Tracking System: Individual marking techniques (tags, dyes, or genetic markers)
Procedure:
- Compartment Establishment: Divide populations into Susceptible (S), Infected (I), and Recovered (R) compartments through experimental infection and monitoring.
- Transmission Rate Estimation: Place susceptible individuals with infected conspecifics at varying densities and measure infection rates over time to estimate transmission coefficient (β).
- Recovery Rate Determination: Monitor infected individuals until clearance of infection or death to estimate recovery rate (γ).
- Integrated Dynamics: Establish mesocosms with predators and prey where prey populations include all three SIR compartments.
- Multi-model Fitting: Simultaneously fit SIR parameters and predator-prey parameters to the experimental data.
- Intervention Testing: Use the parameterized model to test theoretical interventions (vaccination, culling, habitat modification).
Protocol: Probabilistic Analytical Modeling for Individual Variation
Purpose: To incorporate natural behavioral variation into pursuit-evasion models using the PAM framework.
Materials and Reagents:
- High-Speed Tracking: Video recording system capable of ≥100 fps
- Behavioral Arena: Controlled environment with appropriate spatial dimensions
- Tracking Software: Automated or semi-automated motion tracking (e.g., MATLAB Tracking, ImageJ TrackMate)
- Statistical Analysis Tools: Software capable of probability density function fitting
Procedure:
- Kinematic Data Collection: Record predator-prey interactions (e.g., fish pairs) from multiple angles to extract 3D kinematic data.
- Parameter Distribution Fitting: For each relevant parameter (speed, flush distance, escape angles), fit probability density functions to the experimental measurements.
- Tactic Identification: Determine whether predators use pure pursuit, deviated pure pursuit, or constant absolute target direction strategies [23].
- Expected Value Calculation: Using probability theory, calculate the expected value of success metrics (capture probability, survival probability) according to the equation: E[Y] = ∫h(x)f_X(x)dx [23].
- Sensitivity Analysis: Vary the means of the PDFs and recalculate expected values to determine which parameters most influence interaction outcomes.
- Model Refinement: Iteratively refine the analytical model to better match observed outcomes while maintaining analytical tractability.
Visualization of Model Relationships and Limitations
Figure 1: Relationship between core predator-prey models, their limitations, and the extensions developed to address these limitations for biological applications.
Research Reagent Solutions for Predator-Prey Experimental Systems
Table 3: Essential Research Materials and Analytical Tools
| Category | Specific Item/Technique | Function in Research | Application Notes |
|---|---|---|---|
| Model Organisms | Protists (Paramecium-Didinium) | Classic laboratory system for testing oscillation dynamics | Short generation times allow rapid data collection; sensitive to environmental conditions |
| Model Organisms | Fish species (Bluefish-Zebrafish) [23] | Study pursuit-evasion kinematics and probabilistic outcomes | Enable high-speed behavioral tracking; natural predator-prey relationships exist |
| Tracking Software | ImageJ with TrackMate plugin [107] | Automated motion tracking and trajectory analysis | Open-source solution; requires optimization for specific organisms and recording conditions |
| Parameter Estimation | Nonlinear regression algorithms (LSQ nonlinear in SciPy) | Fitting model parameters to experimental data | Requires good initial parameter guesses; sensitive to noise in population counts |
| Probability Analysis | PDF fitting toolboxes (MATLAB Statistics, SciPy.stats) [23] | Characterizing natural variation in behavioral parameters | Essential for implementing PAM framework; choice of distribution affects results |
| Experimental Arenas | Mesocosms with environmental control | Intermediate-scale systems bridging lab and field studies | Allow manipulation of specific factors while maintaining some ecological complexity |
| Diagnostic Assays | Pathogen detection (PCR, ELISA) [106] | Monitoring disease status in SIR-extended models | Required for compartmental assignment in epidemic models; sensitivity affects accuracy |
Conclusion
Mathematical modeling of predator-prey interactions has evolved far beyond its ecological origins, emerging as a versatile framework for understanding complex biological systems across disciplines. Foundational principles now integrate with sophisticated computational methods, while robust stability analysis and bifurcation control provide crucial troubleshooting tools for system management. The validation through parameter inference and comparative frameworks ensures model reliability, particularly as these approaches find expanding applications in biomedical contexts. For researchers and drug development professionals, these models offer powerful analogies for tumor-immune dynamics, with emerging insights into resource competition, immunoediting, and treatment optimization. Future directions should focus on refining multi-scale models, enhancing machine learning integration, and developing specialized frameworks that address the unique constraints of biomedical systems, particularly in personalized medicine and therapeutic strategy development.
References
- 1. Lotka–Volterra equations [https://en.wikipedia.org/wiki/Lotka%E2%80%93Volterra_equations]
- 2. Alfred J. Lotka and the origins of theoretical population ecology [https://pmc.ncbi.nlm.nih.gov/articles/PMC4534218/]
- 3. The Lotka-Volterra Model: Its History and Applications [https://video.bellarmine.edu/media/Sheridan+Payne+-+The+Lotka-Volterra+ModelA+Its+History+and+Applications/1_5tudb72g]
- 4. Lotka, Volterra and the predator–prey system (1920–1926) [https://link.springer.com/chapter/10.1007/978-0-85729-115-8_13]
- 5. Predator-Prey Models [https://sites.math.duke.edu/education/webfeats/Word2HTML/Predator.html]
- 6. Lotka Volterra Equations [https://rutagokhale.com/lotka-volterra-equations/]
- 7. 1.4: The Lotka-Volterra Predator-Prey Model [https://math.libretexts.org/Bookshelves/Applied_Mathematics/Mathematical_Biology_(Chasnov)/01%3A_Population_Dynamics/1.04%3A_The_Lotka-Volterra_Predator-Prey_Model]
- 8. Mathematical Models of Predator-Prey Population Dynamics [https://bioengineering.hyperbook.mcgill.ca/mathematical-models-of-predator-prey-population-dynamics/]
- 9. The Circle of Life: The Mathematics of Predator-Prey ... [https://kids.frontiersin.org/articles/10.3389/frym.2021.651131]
- 10. Lotka-Volterra Model - an overview [https://www.sciencedirect.com/topics/earth-and-planetary-sciences/lotka-volterra-model]
- 11. Ratio-Dependence in Predator-Prey Systems as an Edge ... [https://www.frontiersin.org/journals/ecology-and-evolution/articles/10.3389/fevo.2021.725041/full]
- 12. A comparison of two predator–prey models with Holling's ... [https://www.sciencedirect.com/science/article/abs/pii/S0025556408000205]
- 13. A discretized ratio-dependent Holling-Tanner predator-prey ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12140255/]
- 14. A delayed ratio-dependent predator–prey model of ... [https://link.springer.com/article/10.1007/s11071-013-1121-3]
- 15. Dynamics of a delayed discrete semi-ratio-dependent ... [https://advancesincontinuousanddiscretemodels.springeropen.com/articles/10.1186/1687-1847-2011-7]
- 16. Consistent discretization of a ratio-dependent predator– ... [https://link.springer.com/article/10.1186/s13662-025-04016-5]
- 17. Dynamics of a predator–prey model with generalized ... [https://www.sciencedirect.com/science/article/abs/pii/S0025556420300857]
- 18. Dynamical analysis of a ratio-dependent predator–prey model ... [https://advancesincontinuousanddiscretemodels.springeropen.com/articles/10.1186/s13662-018-1625-8]
- 19. 16.2: Quantifying Predator-Prey Dynamics [https://bio.libretexts.org/Courses/Gettysburg_College/01%3A_Ecology_for_All/16%3A_Antagonistic_Interactions/16.02%3A_Quantifying_Predator-Prey_Dynamics]
- 20. Epidemic Dynamics in the Spatio-Temporal Predator-Prey ... [https://www.frontiersin.org/journals/applied-mathematics-and-statistics/articles/10.3389/fams.2025.1642676/abstract]
- 21. Spatiotemporal Dynamics of a Predator–Prey Model with ... [https://www.mdpi.com/2227-7390/13/15/2474]
- 22. Dynamic complexity of a delayed spatiotemporal predator ... [https://www.frontiersin.org/journals/applied-mathematics-and-statistics/articles/10.3389/fams.2025.1523276/full]
- 23. Probabilistic analytical modelling of predator–prey ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6364652/]
- 24. Multiple preferred escape trajectories are explained by a ... [https://elifesciences.org/articles/77699]
- 25. Estimating prey activity curves using a quantitative model ... [https://www.sciencedirect.com/science/article/abs/pii/S0304380024002564]
- 26. Emergent properties from organisms to ecosystems [https://pmc.ncbi.nlm.nih.gov/articles/PMC2675173/]
- 27. The role of emergence in living systems [https://medium.com/neo-cybernetics/the-role-of-emergence-in-living-systems-ec8ea7a0d1ab]
- 28. The concepts of emergent and collective properties in ... [https://www.sciencedirect.com/science/article/abs/pii/S0304380005001389]
- 29. Chaos and bifurcations of a discretized Holling-II prey- ... [https://www.nature.com/articles/s41598-025-04333-5]
- 30. Ecological sensitivities to the interplay of Allee effects, prey ... [https://link.springer.com/article/10.1140/epjb/s10051-025-01050-w]
- 31. Impact of the Allee Effect on the Dynamics of a Predator ... [https://www.mdpi.com/2227-7390/13/4/633]
- 32. Influence of fear and allee effects on stability and species ... [https://www.sciencedirect.com/science/article/abs/pii/S100757042500526X]
- 33. Learning to fear novel stimuli by observing others in the ... [https://www.sciencedirect.com/science/article/abs/pii/S0149763425000065]
- 34. The elegant complexity of fear in non-human animals - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC9788375/]
- 35. From invasion to coexistence: A mathematical modeling ... [https://www.sciencedirect.com/science/article/abs/pii/S0960077925011397]
- 36. A Mathematical Model Supporting a Hyperpredation Effect in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8004525/]
- 37. Exploring coexistence mechanisms in a three-species ... [https://pubmed.ncbi.nlm.nih.gov/35605380/]
- 38. Species coexistence in the reinforcement learning paradigm [https://arxiv.org/html/2508.17599v1]
- 39. Modeling Predator-Prey Dynamics with Stochastic ... [https://arxiv.org/html/2510.08642v1]
- 40. The (Mathematical) Modeling Process in Biosciences - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4686688/]
- 41. Stochastic dynamics of predator-prey interactions | PLOS One [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0255880]
- 42. Fitting stochastic predator–prey models using both ... [https://www.sciencedirect.com/science/article/abs/pii/S0040580921000046]
- 43. of the stability of a Analysis - predator model... | PLOS One prey [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0305179]
- 44. SciML: Open Source Software for Scientific Machine Learning [https://sciml.ai/]
- 45. On validation and invalidation of biological models [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/1471-2105-10-132]
- 46. Consistent discretization of a ratio-dependent predator–prey ... [https://advancesincontinuousanddiscretemodels.springeropen.com/articles/10.1186/s13662-025-04016-5]
- 47. Machine learning and bifurcation analysis in a discrete ... [https://www.nature.com/articles/s41598-025-24544-0]
- 48. Using multi-delay discrete delay differential equations to ... [https://arxiv.org/html/2410.09451v1]
- 49. Stability analysis and chaos control in a discrete predator ... [https://www.aimspress.com/article/doi/10.3934/math.2024656]
- 50. Investigating the impact of discretization techniques on real ... [https://www.sciencedirect.com/science/article/pii/S2405844024156228]
- 51. Predator - prey models: a review on some recent adaptations [https://arxiv.org/html/2501.16860v1]
- 52. Optimal control of agent-based models via surrogate ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11790234/]
- 53. An agent-based approach for modelling collective dynamics in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7423381/]
- 54. Using agent-based modelling to inform wildlife ... [https://www.sciencedirect.com/science/article/abs/pii/S0304380021000764]
- 55. Learning to hunt: A data-driven stochastic feedback control ... [https://www.sciencedirect.com/science/article/pii/S0022519324003060]
- 56. Discussions on Qualitative & Quantitative Data in the ... [https://rofasss.org/2022/05/16/qq-data-in-abm/]
- 57. MATHEMATICA tutorial, Part 2.3: Predator-Prey Equations [https://www.cfm.brown.edu/people/dobrush/am34/Mathematica/ch3/lotka.html]
- 58. Predator-Prey in Tumor-Immune Interactions: A Wrong ... [https://www.frontiersin.org/journals/immunology/articles/10.3389/fimmu.2021.668221/full]
- 59. Dynamics of a Model of Tumor–Immune Cell Interactions ... [https://www.mdpi.com/2227-7390/13/13/2200]
- 60. Tumor-infiltrating lymphocytes and tumor-associated ... [https://www.frontiersin.org/journals/immunology/articles/10.3389/fimmu.2025.1655176/full]
- 61. Mathematical modeling of tumor-immune interactions [https://arxiv.org/html/2511.00507v1]
- 62. The Role of the Tumor Microenvironment (TME) in ... [https://pubmed.ncbi.nlm.nih.gov/40141358/?utm_source=FeedFetcher&utm_medium=rss&utm_campaign=None&utm_content=14EXV6AaFU8htrIOCjRMdpDNiKtgASVCScQXcx3qOBm2jl8k8j&fc=None&ff=20250327111340&v=2.18.0.post9+e462414]
- 63. Tumor-Infiltrating Lymphocytes (TILs): How Our Immune ... [https://oncodaily.com/oncolibrary/tils-tumor-infiltrating-lymphocytes]
- 64. Cellular dynamics of tumor microenvironment driving ... [https://www.sciencedirect.com/science/article/abs/pii/S0304383524006670]
- 65. Drug‐Use Safety Enhancement Model—Theory and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12039681/]
- 66. Modeling Moose–Wolf interactions in Isle Royale National ... [https://www.nature.com/articles/s41598-025-08874-7]
- 67. The leading neighborhood-level predictors of drug overdose [https://www.sciencedirect.com/science/article/abs/pii/S0376871621006384]
- 68. 8. Evidence-Based Prevention and Treatment Models [https://iopn.library.illinois.edu/pressbooks/druguseandmisuse/chapter/evidence-based-prevention-and-treatment-models/]
- 69. Mathematical Analysis of a Prey–Predator System [https://www.mdpi.com/2297-8747/24/1/22]
- 70. Local and global stability analysis of HIV/AIDS by using a ... [https://www.nature.com/articles/s41598-024-82872-z]
- 71. Mathematical Analysis of an Infectious Disease Model [https://link.springer.com/article/10.1007/s44198-025-00333-1]
- 72. Mathematical modeling for COVID-19 transmission dynamics [https://pmc.ncbi.nlm.nih.gov/articles/PMC8760842/]
- 73. Hopf bifurcation [https://en.wikipedia.org/wiki/Hopf_bifurcation]
- 74. ODE-Project The Hopf Bifurcation [https://faculty.sfasu.edu/judsontw/ode/html-snapshot/nonlinear04.html]
- 75. Neimark-Sacker bifurcation [http://www.scholarpedia.org/article/Neimark-Sacker_bifurcation]
- 76. Neimark-Sacker bifurcation of a two-dimensional discrete- ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4759445/]
- 77. Qualitative analysis and phase of chaos control of the ... [https://www.nature.com/articles/s41598-022-23074-3]
- 78. Exploring chaos and bifurcation in a discrete prey–predator ... [https://www.nature.com/articles/s41598-024-62439-8]
- 79. Chapter 11 Hopf bifurcation in a predator-prey model [https://staff.fnwi.uva.nl/a.m.deroos/projects/QuantitativeBiology/43-HopfPoint-Rosenzweig.html]
- 80. Dynamical transitions and chaos control in a discrete ... [https://www.sciencedirect.com/science/article/abs/pii/S0960077925010847]
- 81. Chaos control and sensitivity analysis of climate change ... [https://www.nature.com/articles/s41598-025-09182-w]
- 82. Enhancing maximum sustainable yield in a patchy prey– ... [https://www.sciencedirect.com/science/article/abs/pii/S1476945X24000357]
- 83. Chaos in a predator–prey-based mathematical model for ... [https://www.sciencedirect.com/science/article/abs/pii/S009630031830969X]
- 84. Enhancing maximum sustainable yield in a multi-patch ... [https://ui.adsabs.harvard.edu/abs/2025MMNP...20...13M/abstract]
- 85. Modelling and parameter inference of predator–prey ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5310726/]
- 86. Precision Harvesting Industry Analysis Report 2025 [https://finance.yahoo.com/news/precision-harvesting-industry-analysis-report-112100754.html]
- 87. From theory to experimental design—Quantifying a trait ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5918917/]
- 88. A modeling framework for the establishment and spread ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5648669/]
- 89. Experimental Test of Preferences for an Invasive Prey by an ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0165427]
- 90. Two-prey predator model with Holling Type-II functional ... [https://link.springer.com/article/10.1007/s12190-025-02544-7]
- 91. A Model to Translate Molecular Detection Into Predation ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12550487/]
- 92. A new modelling framework for predator-prey interactions [https://www.sciencedirect.com/science/article/abs/pii/S1574954123001978]
- 93. Predator–Prey models | Research Starters [https://www.ebsco.com/research-starters/mathematics/predator-prey-models]
- 94. A microcosm approach highlights the response of soil ... [https://www.nature.com/articles/s41598-019-50730-y]
- 95. Functional regimes define soil microbiome response to ... [https://www.nature.com/articles/s41586-025-09264-9]
- 96. Carbon amendments in soil microcosms induce uneven ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10716739/]
- 97. A Basic Guide to Real Time PCR in Microbial Diagnostics [https://pmc.ncbi.nlm.nih.gov/articles/PMC5288344/]
- 98. Co-Evolution of Predator-Prey Ecosystems by Reinforcement ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8069842/]
- 99. A reinforcement learning-based predator-prey model [https://www.sciencedirect.com/science/article/abs/pii/S1476945X1930039X]
- 100. A deep learning model for predicting competitive pursuit ... [https://www.sciencedirect.com/science/article/abs/pii/S0006899325001933]
- 101. Translating Virtual Prey-Predator Interaction to Real-World ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10742093/]
- 102. How to design the fair experimental classifier evaluation [https://www.sciencedirect.com/science/article/abs/pii/S1568494621001423]
- 103. Machine Learning Algorithms: An Experimental Evaluation ... [https://www.mdpi.com/1999-4893/15/4/130]
- 104. 4 Predictive Analytics Models Driving 2025 Insights [https://proschoolonline.com/blog/predictive-analytics-models-transforming-forecasting]
- 105. Color palettes and accessibility features for data ... - Medium [https://medium.com/carbondesign/color-palettes-and-accessibility-features-for-data-visualization-7869f4874fca]
- 106. Mathematical models to study the biology of pathogens and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8961237/]
- 107. Various Approaches to the Quantitative Evaluation of ... [https://www.mdpi.com/2073-8994/14/1/7]